Public security
For K12 education pioneers, embarking on a journey to upgrade security controls can present a myriad of questions about finding the best-fit solutions and overcoming funding hurdles. A majority of public-school districts today are faced with outdated infrastructure and security controls, requiring necessary upgrades. By addressing these concerns head on, schools will ensure a safer environment for both students and staff, mitigating risks posed by unforeseen physical and digital threats. Common...
Security Industry Authority announced the award of £72,000 from its grant for good causes fund to seven registered charities and community interest companies across the UK. This brings the total grants awarded by the SIA using cash confiscated from criminals to over £250,000. Through this fund, the UK’s private security industry regulator distributes money recovered through proceeds of crime confiscation orders. Grants are used to benefit the private security industry and impr...
Metrasens, a provider of advanced detection systems for security and safety applications, is pleased to announce its partnership with the Central Indiana Educational Service Center (CIESC), which provides cooperative purchasing programs for member school districts across Indiana. Through this partnership, CIESC member schools, as well as 270 other districts that are members of other Education Service Centers (ESC) across Indiana, can purchase Metrasens Ultra weapons detection systems through th...
Johnson Controls, the global pioneer for smart, healthy, and sustainable buildings, has announced the renewal of its reseller partnership with Everbridge. The collaboration aims to assist security pioneers with a centralized view of physical assets and external risk factors—such as geopolitical threats or natural disasters—that could impact organizational safety and resiliency. Partnership with Everbridge “Not only do today’s security pioneers face the challenge of sta...
ASSA ABLOY ACCENTRA™ and DoorBird provide a comprehensive solution for property owners looking to enhance the security of their property while adding valuable convenience for their residents and staff. Secure and convenient With this new integration, the DoorBird IP video intercom can be managed seamlessly within the ACCENTRA Mult-family dashboard, eliminating the need to manage two separate systems. ACCENTRA allows a secure and convenient way for residents and staff to access all...
Genetec, a provider of unified security, public safety, operations, and business intelligence solutions, is pleased to announce its plans for the Passenger Terminal Expo 2024, taking place in Messe Frankfurt, Germany from April 16 – 18, 2024. Airport portfolio The company will be present at stand #D220, demonstrating its full airport portfolio designed to reduce security risk, improve planning, and automate airport operations. Representatives will be on hand to discuss the latest Genetec...
News
Amid escalating security concerns for places of worship in the UK, the Home Office has launched two pivotal schemes to enhance protective measures. The Places of Worship Protective Security Funding Scheme and the Protective Security for Mosque Schemes aim to combat hate crimes and ensure safety during religious gatherings by funding physical measures such as CCTV, fencing, and alarms. Complexities of security solutions Aware of this disquieting matter, Jacksons Fencing, a security specialist based in the UK, commissioned a white paper study to address the complexities of designing security solutions for places of worship amidst rising hate crime offenses. With over 145,000 crimes reported in England and Wales alone in 2023, rising from over 41,000 in 2013, the research aims to uncover the unique challenges and propose strategies to enhance the protection against criminal activities. Study findings The findings underscore the critical need for improved security measures in religious spaces Findings from Jacksons Fencing’s recent study are alarming: 59% of respondents have been subjected to a hate crime or attack. Additionally, other findings underscore the disturbing regularity of these incidents: 74% indicate that their religious institution is targeted by a crime annually, with 62% experiencing attacks occurring at least twice a year. These findings underscore the critical need for improved security measures in religious spaces. Identifying the most pressing threats While larger criminal organizations often dominate discussions on crime, our research emphasizes the significant impact of individual perpetrators. Vandalism emerges as the most concerning criminal act (29%), followed closely by theft crimes (32%), often involving burglaries targeting donation boxes for monetary gain. Moreover, verbal assaults or harassment make up nearly a quarter of reported offenses (24%), trespassing (23%), and physical assaults (18%) are disturbingly common occurrences. A call for collaborative action Our findings enabled us to analyze crime statistics within specific religious communities and compare them across all places of worship in the UK. Churches face a higher prevalence of vandalism (75%) and burglary (30%). Theft stands out as the primary concern in Islamic institutions, constituting 45% of all mosque-related incidents. However, Muslims face a higher incidence of verbal attacks (40%), more than double the proportion experienced by Christians (21%). Trespassing poses the main challenge for temples (49%) and gurdwaras (50%). Hinduism also contends with robbery issues (46%), while Sikhs encounter a significant amount of verbal harassment (50%). Refuges of security A quarter of respondents noted discernible improvements in security measures during their visits Despite the escalating instances of criminal activity targeting places of worship (as reported by 81% of respondents witnessing either a static or increased crime rate over the past five years), there is a prevailing sentiment among 44% that safety measures have undergone enhancements. In line with the research, a quarter of respondents noted discernible improvements in security measures during their visits to places of worship, with 38% acknowledging tighter controls over access to premises and grounds. The Government’s allocation of £28 million for religious buildings and places of worship, with a significant portion earmarked for the most affected communities, particularly the Muslim community, is a step in the right direction. Nonetheless, 15% of respondents express concerns that their place of worship has become less secure compared to five years ago. Moving forward Peter Jackson, Managing Director, of Jackson Fencing, emphasizes the importance of striking a balance between security and aesthetics, “The design of on-site security should deter trespassers and prevent crime, while also fostering a welcoming atmosphere and instilling a sense of calm. Achieving this delicate equilibrium is paramount." He adds, "We anticipate that our findings and primary suggestions will be a step in the right direction for stakeholders in physical security to collaborate with religious communities toward a shared objective of safeguarding places of worship, which hold immense significance for numerous communities across the UK."
Hexagon’s Safety, Infrastructure & Geospatial division announced Qognify, a pioneering provider of physical security solutions, has officially adopted the Hexagon corporate identity and fully integrated into the division as the physical security business unit. Following the acquisition of Qognify by Hexagon in April 2023, this event marks a new era in physical security and public safety innovation, enabling customers to safeguard their assets, infrastructure and communities. Hexagon’s wider portfolio The combined strength of these products and Hexagon’s wider portfolio, including public safety More than 4,000 organizations worldwide depend on Qognify’s powerful video management software and physical security information management solutions. The combined strength of these products and Hexagon’s wider portfolio, including public safety solutions that help to protect one billion people, provides customers more options to increase situational awareness, streamline operations and mitigate risks. Many organizations from both the private and public sectors are already using Qognify physical security solutions in combination with other Hexagon solutions, creating a powerful ecosystem of technologies. Advantage of Hexagon’s position Mladen Stojic, President of Government, Transportation, Defense and Security at Hexagon’s Safety, Infrastructure & Geospatial division states: “By rebranding and integrating Qognify into Hexagon, we are fostering a culture of innovation and collaboration. It will enable us to deliver cutting-edge technologies that will redefine the future of physical security and public safety. As one, we will unlock synergies for enhanced capabilities, bring added value to customers and expand our reach into additional markets.” Hexagon will continue to leverage the strong global partner network established by Qognify, providing partners the opportunity to take advantage of Hexagon’s position as a worldwide technology pioneer. Partners can tap into new business areas, as well as serve existing clients with a truly holistic solution set from a single trusted source. Hexagon’s physical security solutions Hexagon is also committed to progressing the VMS upgrade program. The program enables customers of Qognify’s Ocularis and NiceVision products to move to Qognify VMS and benefit from new, advanced capabilities. Customers and partners will have the opportunity to experience Hexagon’s physical security solutions and explore its wider portfolio of technologies at events around the world, including Hexagon LIVE EMEA in Wiesbaden, Germany, and ISC West in Las Vegas.
Emergencies, natural disasters, crises, and military conflicts: experts say that efficient civil protection can only be ensured if fire services, emergency, and disaster response services cooperate even more closely at the international and interdisciplinary levels – reason enough for 'Safeguarding tomorrow' to have been selected as the motto of INTERSCHUTZ 2026. The world's renowned trade fair for fire and rescue services, civil protection, safety & security aims to motivate everyone actively involved in those sectors to focus even more strongly on topics such as innovation, foresight, and cooperation. Artificial intelligence (AI) “Innovation means, for example, the handling and use of artificial intelligence (AI),” says Bernd Heinold, INTERSCHUTZ Project Manager at Deutsche Messe, adding “Foresight means thinking ahead and in scenarios so that all protective measures and preparations for tomorrow can be taken right now today. And cooperation is the key that enables individual measures to coalesce into the greater whole." Heinold emphasizes that close networking of all players in hazard prevention is one of the essential prerequisites for coping with future challenges and ever-changing requirements. About INTERSCHUTZ INTERSCHUTZ is the world's renowned trade fair for fire brigades, rescue services and civil protection. The next show takes place from 01 to 06 June 2026 in Hannover, Germany and runs under the motto of ‘safeguarding tomorrow’. The INTERSCHUTZ portfolio includes all products and services in the fields of Fire Fighting, Fire Prevention, Rescue Services, Civil Protection, Communications & Control Center Solutions, and Protective Equipment. International events within the INTERSCHUTZ portfolio are AFAC Australia, REAS Italy and the China International Emergency Management Exhibition (CIEME). The next INTERSCHUTZ will take place from June 01 - 06, 2026 at the exhibition grounds in Hanover.
Allied Universal®, the world’s pioneering security and facility services provider, announced tips for music festival safety. With warmer months fast approaching, so too are popular summer events such as music festivals. Though fun, festivals can present significant safety risks. They attract large crowds, are prone to heavy alcohol consumption, and drug use, and feature large temporary infrastructure. Allied Universal views safety as non-negotiable and encourages attendees to review and consider the following safety tips to ensure they have a fun and safe festival experience. Prioritize safety, not capturing content If unsafe activity or a fight breaks out, move to safety, not to record. Well-being is more important than “likes”. If they see someone in distress, alert event staff instead of their followers. More safety tips Stay Cool and Hydrated Wear sunscreen, a hat, and sunglasses. Drink lots of water. Find shade often. Learn The Way Around Grab or download a festival map for reference. Locate exits and remember that in an emergency, the closest exit may not be the best one to use. Know where the restrooms, first-aid tents, food, camping, and chill-out zones are. Exercise Care Around Temporary Structures Don’t lean, pull, or climb on temporary structures- they could collapse and fall. Use the Buddy System Don’t go to a crowded event alone. A helping hand in a crowd crush can mean the difference between life or death if they’ve fallen or become injured. Establish a meeting place and time with friends, in case they get separated. Beware of Pickpockets Always keep an eye on their belongings. Keep Cash and Important Information with them Carry a small amount of cash in case their credit cards are stolen or misplaced. Write down contact information so they can call someone if their phone runs out of charge or they get separated from their device. Responsible Use of Alcohol and Recreational Drugs Alcohol and drug use are prevalent; if they are of legal age, be responsible. Never drive while intoxicated – call a sober friend, rideshare service, or taxi. Protect Their Hearing Bring hearing protection if needed. If they can’t cope with the loud noise, move away from the speakers for a while.
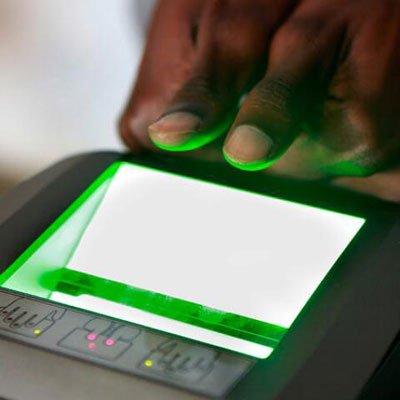
IDEMIA Public Security, the global provider of biometric and secure identity solutions for government, travel, and law enforcement has once again proven its leadership, showcasing the most accurate algorithms in the National Institute of Standards and Technology’s (NIST) latest Evaluation of Latent Fingerprint Technologies (ELFT) tests. NIST ELFT NIST ELFT is the global benchmark for latent fingerprint and palm print identification used to identify latent fingerprints and palm prints found at crime scenes. For the fourth time in a row, IDEMIA Public Security leads the market with the most accurate and fastest (among the most accurate) algorithms. Low FPIR IDEMIA demonstrated vastly superior performance in palmprint identification In addition to accuracy, which increases the chances of identifying leads in law enforcement investigations, IDEMIA’s algorithms showed a very low False Positive Identification Rate (FPIR at less than 8% whereas the nearest competitor is at above 11%), allowing the latent examiner to process more cases, accurately and faster. Furthermore, IDEMIA demonstrated vastly superior performance in palmprint identification, another highly significant contribution. Using this technology, the human-artificial Intelligence (AI) duo becomes more productive, and the examiner’s valuable time is optimized. Fast, accurate, and fair solutions IDEMIA is committed to the highest level of performance to provide fast, accurate, and fair solutions. As a result, IDEMIA’s customers can solve crimes more quickly, while the communities and the world are made a safer place. These ELFT results come on the heels of other recent high-ranking performances in NIST benchmarks, further demonstrating IDEMIA’s technology leadership. These include: FINGERPRINT: 1 in the NIST Proprietary Fingerprint Template (PFT) III benchmark on all test datasets in December 2023, 1 in NIST ELFT February 2024, 1 in the mFIT Challenge in June 2022, FACE: 1 in fairness and demonstrated lack of bias for the NIST Face Recognition Vendor Test (FRVT) in January 2023, IRIS: 1 in the latest NIST Iris Exchange (IREX 10) ranking in September 2023. Multi-Biometric Search Services (MBSS) solutions "Based on our performance in this benchmark, we can confirm our long-term commitment to investing in further developing the technology and creating continuously more value for the customers. Our ability to offer cutting-edge products goes hand in hand with our long-standing 50-plus-year pledge to provide law enforcement agencies with the best systems on the market." "I am very proud to announce that the latest algorithms submitted to this benchmark are already available in our flagship Multi-Biometric Search Services (MBSS) solutions. I would like to congratulate our teams of developers on their hard work and innovation," said Jean-Christophe Fondeur, IDEMIA Public Security Chief Technology Officer.
TraiCon Events will be hosting India’s premier cybersecurity event titled “Cyber Revolution Summit” scheduled on 25th and 26th April 2024 in New Delhi, India. This summit will feature keynote presentations and panel discussions with top security experts from various industries covering a range of topics, including cybersecurity innovations, data privacy & security, risk management, network security, threat detection & intelligence, and vulnerability management. Platform for public & private alliances This summit is an indisputable platform for public & private alliances, where this summit aims to bring 500+ pre-qualified CISOs, CIOs, heads of cyber security, digital transformation, IT infrastructure, information and communication technologies, and other experts in this domain to discuss the potential and recent trends of cybersecurity. Many system integrators, IT security solution providers, cybersecurity companies, cloud & data security, threat management, cyber software, and cybercrime companies will be participating in the Cyber Revolution Summit as Sponsors or Exhibitors who will be showcasing their host of solutions for the future of cyberspace.


Expert commentary
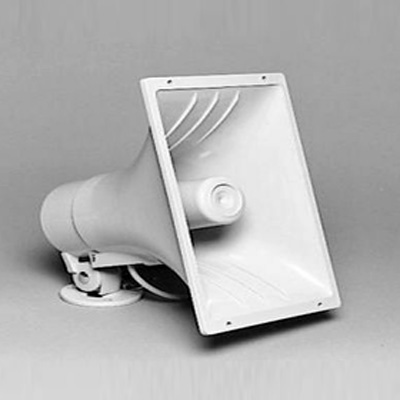
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realize, however, that some of these traditional security measures are becoming antiquated and no longer cutting. The now and future of overnight security is in remote guarding. Pioneered by companies like Los Angeles-based Elite Interactive Solutions, which was founded back in 2007, remote guarding is revolutionizing the overnight security business. Minimizing criminal activity Remote guarding is fast becoming the most popular choice among commercial end-user property owners Remote guarding utilizes a combination of cutting-edge technology, “digital guards,” highly trained security agents, and local law enforcement if and when necessary to minimize the potential of criminal activity. For those adequately enlightened to its overwhelmingly impressive crime prevention capabilities, remote guarding is fast becoming the most popular choice among commercial end-user property owners to secure and protect their investments. What Is Remote Guarding? Remote guarding is a revolutionary concept and increasing trend in security systems that utilize a combination of methods to effectively analyze potential threats to property. Cameras and/or other monitoring devices running highly advanced algorithmic software are installed in strategic areas or vulnerable places onsite and remotely located security agents are immediately notified of any activity within a designated perimeter of the property. A blend of AI, cybersecurity, and video analytics When properly deployed by an expert provider, the technology stack includes a proprietary blend of video analytics, artificial intelligence, cybersecurity, and more. Done right, “noise” is effectively filtered out, allowing agents to act on legitimate alerts and achieve zero false alarms communicated to first responders. Today, there are a lot of terms and descriptions tossed around about remote guarding, remote video, virtual guarding, etc., but those attributes must be present to represent the true definition of the offering and its many virtues. Realtime situational awareness Many systems have a two-way speaker that allows the security agent to give a verbal warning When specially trained security agents are alerted to trespassers, possible intruders, or other suspicious activity, they analyze the situation in real time and determine the necessary level of action. Many systems have a two-way speaker that allows the security agent to give a verbal warning, known as a voice-down, to the individual(s) that they are being watched. Most perpetrators, often believing the response is emanating directly from security personnel on the property itself rather than from a remote command center, flee immediately. However, if the threat persists, the security agent enlists local law enforcement to get on the scene. Customized remote guarding When properly deployed, remote guarding systems are also customized to specific properties. A team of consultants visits the client’s property to evaluate its vulnerabilities and where to best place cameras and/or other monitoring devices for system efficacy. Traditional Security Shortfalls According to Keith Bushey, a retired commander for the Los Angeles Police Department, there is much frustration between law enforcement officers and potential victims of crime due to the historically unreliable performance of traditional burglar alarm systems and central monitoring stations. He states about 90% of security-related calls are false alarms, a problem that has been well-documented through the years. Onsite challenges When a legitimate emergency does occur, the perpetrators have often already done their damage When a legitimate emergency does occur, the perpetrators have often already done their damage and/or escaped by the time law enforcement arrives. Onsite security guards are not the remedy either as they bring their own set of issues and challenges. Unexpected costs Traditional security systems can also have unexpected costs. The cost is not only in the security guards’ paycheck or the cost of the equipment itself. The cost comes when an actual incident occurs. In worst-case scenarios, the security guard(s) are injured, the business suffers inventory loss, and/or damage is sustained to the property. The medical and other costs for the security guard(s), the loss of inventory, property damage, deployment of law enforcement resources, and possible fallout of legal expenses all add up. Even in the best-case scenario, false alarm expenses incur if law enforcement is dispatched. These, among many others, are some of the primary issues that remote guarding resoundingly answers as a superior alternative. A Bounty of Benefits Remote guarding systems have been proven to cut costs and be more effective than traditional security systems. Even though the monthly monitoring costs of remote guarding are significantly higher than traditional intrusion detection system monitoring, the much higher effectiveness in crime reduction, elimination of false alarms, and augmenting or replacement of manned guards result in a substantially higher return on investment (ROI) to the end user. Easy tracking of threats The security cameras already have their image captured on record, making them easier to track down For example, case studies have demonstrated reduced security costs for clients by 60%, on average. These reductions have come from the costs of security staff, inventory, or property loss, plus saving money on insurance premiums and deductibles. The nature of remote guarding reduces the risk and costs of false alarms, with professional security agents able to determine an actual threat before law enforcement is called. In a rare instance when a perpetrator escapes before law enforcement arrives or can detain the individual(s), the security cameras already have their image captured on record, making them easier to track down and identify. Reduction of false alarms The significant reduction in false alarms is greatly appreciated by law enforcement, as it allows them to focus on real emergencies or crises. Better relationships are also developed between clients and law enforcement, as remote guarding systems are highly reliable in providing accurate and real-time information to officers as they approach the scene. In short, it assists law enforcement in doing their job more effectively, as well as more safely thanks to having eyewitness information before engaging in an active crime scene. Partnership When you combine the decreased cost with the increased efficiency and success rate, it is easy to see why many commercial end-user property owners across the country are making the shift to remote guarding. It’s also an outstanding opportunity for professional security dealers and integrators to partner with a remote guarding services provider to bring a superior solution to their end customers and pick up a recurring monthly revenue stream in the process.
The autumn equinox, which marks the start of autumn, occurs this weekend on Saturday, September 23. With darker evenings ahead, the experts at ADT have shared five ways to maximize your home's security. Author's quote Michele Bennett, General Manager at ADT UK&I comments: “Opportunistic thieves use darkness to their advantage, so it’s no surprise that the number of burglaries committed increases when the darker nights draw in." He adds, "Our 2022 burglary report found that burglaries are most common at night, with 58% of burglaries occurring between 6 p.m. and 6 a.m. Taking steps to optimize your home’s security before the clocks go back this year will provide reassurance that your property is as secure as possible.” Five ways to secure your property: Get a monitored alarm installed: A visible alarm system is a strong deterrent to potential burglars, as criminals are less likely to target a home that is protected. In the event of a break-in, a monitored alarm will alert you, your keyholders and depending on the package you take out, the police, ensuring a swift response to an alarm activation. Light up the dark: Well-lit exteriors make your home less appealing to potential intruders. Install motion-activated lights around any entry points, particularly porches and gardens, which alert you to movement on your property. This will also prevent burglars from operating under the cloak of darkness and increase the chance of a passerby spotting suspicious activity. Trim your garden landscape: Thieves look for escape routes and hiding spots when deciding which homes to break into, making gardens with high, overgrown hedges more likely to be targeted. This is especially true in the darker evenings, so be sure to give your garden a thorough tidy-up to make your property less likely to be targeted. It’s also advisable to ensure any tools are locked away in sheds and garages that could assist a burglar such as ladders, or a garden spade to force entry. Be smart with your lights: Using smart plugs allows you to turn on a few well-appointed lights and radios or televisions from any location from your phone. Used in conjunction with an outdoor camera or video doorbell, you can have lamps plugged into smart plugs come on when motion is detected. Programming lights to come on at different times throughout the night will help to deter burglars by making your property look occupied. Purchase a smart doorbell or outdoor camera: Smart doorbells are an effective way to deter burglars as they provide evidence in the event of a break-in, package theft, or other suspicious activity around your home. They also notify you when someone is at your door reducing the chance of you being caught out by a late evening or early morning robbery. Further encroachment Smart doorbells also act as a deterrent to unscrupulous door-to-door sellers and con artists, as video footage is recorded. In the event of a late-night door knock, you can see and speak to whoever is at your front door, without having to open the door. ADT’s new outdoor camera also has two-way audio and a high-pitch deterrent siren so you can warn off anyone from your property to deter any further encroachment.
It’s no secret that the data security sector is constantly changing. It has an annual CGR of about 12.3%. Future trends in data security Much of this has to do with the rise of cybercrime in recent years, with reports showing that cyberattacks happen as often as every 39 seconds. To combat the growing rate of cybercrime, data security has been on the rise. As we journey further into this era, it becomes evident that a spectrum of significant trends is molding the future of data security. This exploration delves into a selection of these trends, unraveling their importance and the potential implications they carry 1. AI security tools will increase Artificial Intelligence is also being used in the development of smart attacks and malware The introduction of Artificial Intelligence in the data security industry brought significant changes, especially in cybersecurity. AI has been the golden standard for face detection, natural language processing, automated threat detection, and automated security systems. Additionally, Artificial Intelligence is also being used in the development of smart attacks and malware, bypassing even the latest security protocols in data control. And as time progresses, AI security tools will flourish and dominate the scene. Let’s take a more in-depth look at three of the top AI security tools. Targeted attack analysis tool Manufacturers utilize targeted attack analysis tools to uncover targeted and stealthy attacks. Artificial Intelligence can be applied to the program’s capabilities, processes, and knowledge. For instance, Symantec launched this tool to combat the Dragon 2.0 attack in 2022. The phishing attack reprimanded multiple energy companies while trying to gain access to their operational networks. Targeted Attack Analysis Tools can analyze incidents and look for similarities from previous situations. They also help detect suspicious activities and collect all the necessary data to determine whether a specific action is malicious. Intercept X tool Results from the Intercept X Tool feature high accuracy and a low false positive rate Sophos, a British security hardware and software company, launched the Intercept X Tool. It engages a neural network that records and analyses data like a human brain. Sophos’ Intercept X Tool can extract features from a single file and perform a deep analysis. It detects malicious activities within 20 milliseconds. Plus, it’s also trained to work on bi-directional sharing and real-world feedback of threat intelligence. Results from the Intercept X Tool feature high accuracy and a low false positive rate. IBM Watson Technology IBM’s QRadar Advisor uses IBM Watson Technology, a unique AI tool for fighting cyber attacks. Artificial Intelligence can auto-investigate activities and indicators for potential exploitation or compromise. With cognitive reasoning, IBM Watson Technology can present critical insights to accelerate the response cycle. Security analysts can utilize this technology to search for threat incidents, reducing the risk of letting them fly under the radar. 2. Blockchain as a security solution It guarantees no points of failure or hackable entrances that can expose datasets inside the system Blockchain is a type of distributed ledger technology (DLT) that aims to establish trust within an untrusting ecosystem. Today it’s one of the most robust cybersecurity technologies in the industry. Blockchain utilizes a decentralized ledger system, but your team members can still gain access to transparent information in the cloud. Members can also record, pass along, and view necessary transactional data in the blockchain. The entire blockchain process maintains data integrity within the system while establishing trust among team members. It guarantees no points of failure or hackable entrances that can expose datasets inside the system. Cybersecurity, biometrics Cybersecurity primarily benefits from these features because blockchain can create a secure and robust wall between data and hackers. On top of that, blockchain ledgers can include biometrics like fingerprints and retina scans. These prevent hackers from accessing any private data. Because blockchain is decentralized, it also limits hackable data. Together with the technology’s record-keeping system, each node is provided insight into data manipulation exposing real-time cybercrime attempts. 3. Increased and widened access control Without access control, expect your company to be open to security issues, including theft, data loss, and breach of data Access control is critical in data security. More than a valuable security tool, business leaders can use access control to regulate people accessing any given resource. A company with an IT security setting can control who has the liberty to edit certain files. One of the primary goals of access control is to minimize threats or attacks to organizations and businesses to keep people and data secure. Without access control, expect your company to be open to security issues, including theft, data loss, and breach of data protection laws. Benefits The benefits of increased and widened access control include: Identifying who can access and control your data at specific time intervals. Protecting data from overwriting, accidental deletion, and malicious intent. User permissions that can be readily changed. Compliance and regulation with data privacy laws. Central management of access to data through a reporting portal or a dashboard. Multi-factor authentication Access control comes in various types and systems, so it’s critical to know the features of what you’re looking for. The most common type is multi-factor authentication or MFA. It involves multiple steps before logging in, requiring the user to enter other relevant information besides the password. Some other examples of information include biometrics, answering a security question, or entering a code sent to the user’s email address. Two-factor authentication, role-based access control Two-factor authentication further prevents unauthorized entries that can result in unnecessary data possession Two-factor authentication further prevents unauthorized entries that can result in unnecessary data possession. Another type of access control is role-based access control. In this setup, only one individual can set up access guidelines and grant permissions to specific team members within an organization. 4. Greater use of the zero-trust security model The zero-trust security model is a framework that requires every user within and outside the organization to undergo authentication, authorization, and validation. These are all essential to ensure proper security configuration before access is granted to the company’s applications and data. A zero-trust model assumes that anyone can cause data breaches and that a traditional network edge is not taken into effect. Moreover, it addresses the following modern-day challenges: Hybrid cloud environments. Security of remote workers. Ransomware threats. This framework utilizes the combination of multiple advanced technologies, including: A risk-based multi-factor authentication. Endpoint security. Identity protection. Cloud workload technology. The zero-trust model uses all these innovative tools for system identification, user verification, access consideration, and system security maintenance. Constant validation and monitoring Enforcing strict policies and compliance with data privacy laws are also essential Additionally, it also considers data encryption, email security, and asset verification before establishing connections with applications. The architecture of a zero-trust framework requires constant validation and monitoring of the users and the devices they are using. Enforcing strict policies and compliance with data privacy laws are also essential. More importantly, the zero trust architecture requires all organizations to be aware of all their available services and accounts to gain complete control of data handling and manipulation. 5. Increased privacy regulations Privacy regulations and policies guide organizations in proper data control, handling, and security. These policies guide organizations in proper data control, handling, and security. As a responsible business owner, you must comply with these regulations to avoid legal issues. With cybersecurity attacks becoming common, expect increased and stricter privacy regulations to be released in the next few years. While current policies are still taken into effect, various modifications and adjustments will occur to compete with the rising numbers of data breaches, thefts, data loss, and more. California Privacy Rights Act (CPRA) Currently, the California Privacy Rights Act (CPRA) is the most comprehensive legislation on state data privacy. It only started to take effect on January 1, 2023. The CPRA introduces the following principles: Broad individual consumer rights. Significant duties of people who need to collect sensitive and personal information. Additional definitions of data privacy and security. An individual’s duties include releasing information about data collection to concerned data subjects and proper access, correction, and deletion of information. Final thoughts 2023 is a big year for data security. Trends such as increased adoption of zero-trust policies, a greater reliance on AI security tools, and the implementation of blockchain as a security solution are all things we expect to see shortly. Staying up-to-date with these trends is important for keeping your business current and ensuring that you’re adhering to new and changing regulations. Doing so can give you an edge over the competition and keep you out of legal hot water.
Security beat
A pioneer in the access control sector since 1971, AMAG Technology is looking to the future and the next generation of products that will expand its services to customers. “In our vision, we have advanced approaches that will not only provide our partners with advanced technologies but also ones that are easier to install with tools to expand their services,” says David Sullivan, who was appointed President of the venerable access control company in September 2022. New challenges at AMAG Sullivan brings a new outlook to the AMAG business, a part of Allied Universal, and a new vision to lead the company into the future. We caught up with David Sullivan to discuss his new challenges at AMAG and the journey ahead as the company looks to the future. Q: How does your background inform your approach to leading AMAG? I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry David Sullivan: With the exception of only a few short years, my career has been in access control. I have experience with several systems and have had the privilege to manage several successful access control companies. As a result, I bring a great deal of experience into my role at AMAG. I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry. Q: How would you describe AMAG’s journey over the last several years and how do you see the future? Sullivan: Prior presidents of AMAG always shared their leadership vision and direction with senior leaders located in the United Kingdom. This had an impact on the full direction of the business, sometimes limiting its ultimate success. Before I became a part of AMAG, these senior leaders that were located in the UK retired, placing for the first time the full management responsibilities of the president. This has allowed me to integrate the business into a single team, with single objectives, and a single vision. We expect to begin to reveal this new vision in the coming weeks. We are excited about the future of AMAG and believe we will surprise the industry with our new products and approach in the coming months and years. Q: How important is it that a manufacturer provides both hardware and software solutions? How does AMAG’s approach (in general) differentiate it in the market? We can design the complete solution, providing functionality that others may find more difficult to accomplish Sullivan: Regardless of the manufacturer, we all provide hardware and software. An access control solution is not complete without both. Some of us choose to make our panels, and others do not. Those who are dependent on third-party suppliers are restricted to the developments and direction of that company, and while it might be perceived to be an open technology, it still is proprietary to the hardware manufacturer. AMAG has controlled its manufacturing of panels from day one. The result means that we can design the complete solution, providing functionality that others may find more difficult to accomplish. Q: How does the breadth of AMAG’s product suite provide advantages to customers and/or integrators? Sullivan: AMAG’s product portfolio is unique and provides the end user with an end-to-end identity management solution from one company. Our Control Room PSIM, Symmetry CONNECT Identity Management Solution, Symmetry Access Control, and Symmetry GUEST solutions all integrate to provide the user with a broad set of features and capabilities from a single provider. There is no finger-pointing when we come to support your system. We hold full responsibility for making it work and can quickly provide a resolution to any application difficulties the user may be experiencing. Q: How does AMAG address the divide between on-prem and cloud systems? How do you help customers make the transition and/or plan for the future? We are in the early stages of developing our next generation of access control in which we intend to provide on-prem Sullivan: In our current product portfolio, we have three products that are cloud-based. Our mobile credential platform (Symmetry Mobile), our visitor management solution (Symmetry GUEST), and our physical identity and access management solution (Symmetry CONNECT) are all offerings that operate in the cloud. We are in the early stages of developing our next generation of access control in which we intend to provide on-prem, web client, and cloud-based offerings. One of the primary objectives is to ensure that the large installed base of systems that are out there today will be able to migrate not only to our next generation but as well to the cloud if the client so desires. Q: What is AMAG’s approach to mobile credentialing? Sullivan: As an access control provider, adding Symmetry Mobile credentialing to our portfolio just made sense. We want our customers to have a forward-thinking solution with the opportunity to save money not only on the physical badges but the cost of printing and distributing badges. Mobile credentials can be easily issued and revoked remotely, reducing administrative overhead, and eliminating the need for physical inventory management. Organizations can centrally configure what devices are used and the read range for each type of device and operating system, thus providing flexibility. Symmetry Mobile offers a customized questionnaire that controls access and reduces liabilities. Q: What has surprised you the most in your first year or so leading AMAG? Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company Sullivan: I wouldn’t say I was surprised by this as much as happy to see, but I would say that the quality of our people was a pleasant surprise. As well, the AMAG product offering is broad and has some unique elements. When coupled with the depth of the resources that we have in AMAG, I know that we are second to none. Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company that has so many talented people. Q: Please describe your dealer channel, and how you are seeking to expand it. Sullivan: The AMAG products are sophisticated and typically are installed for higher-end applications. With this sophistication comes a need to be well able to install such a solution. We have a strong group of certified and loyal partners who help us to deliver these enterprise solutions. We desire to provide our existing partners with updated and competitive systems to offer to their end users. Q: What is the security industry’s (and/or AMAG’s) biggest challenge in the next five years? We need to find ways to provide both our channel partners and the customers with solutions that are easily integrated Sullivan: I believe that the advancements that we are seeing in technology provide our industry with the opportunity to truly change how security is provided to our collective customers. As we advance these solutions, we will need to do so responsibly and in a way that helps the channel’s abilities. We need to find ways to train our partners to both install and support these more complex solutions. At the same time, we need to find ways to provide both our channel partners and the customers with solutions that are easily integrated, moving away from proprietary closed systems to open and cohesive solutions. This will ensure that the users get the best, and most complete solutions. Q: What does the industry as a whole misunderstand about AMAG -- time to set the record straight! Sullivan: Well, I am not ready to openly share where we are heading. We are in the process of putting together some advanced approaches to how we will do business with our partners. We are focused on providing tools that will enhance their services to their customers, and with products that are leading edge. I can only state that all should keep their eyes on AMAG, because over the next few years, we are going to surprise some people, and more importantly make our loyal partners quite powerful.
Acre is a company built on mergers and acquisitions (M&A). Since its founding in 2012, Acre acquired several familiar access control companies, from Vanderbilt to RS2 Technologies, Open Options to Feenics, and several others. Acre itself was acquired in 2021 by UK-based private equity firm Triton, thus launching a new chapter in the company's history. Don Joos was named the new CEO in 2022 and set about transforming Acre from a collection of acquired companies into a coherent whole (representing various brands). A year later, we recently caught up with Don Joos to discuss the "new Acre" and what's ahead. Q: How does your background inform your approach to leading Acre Security? In physical security, there is a shift to more of a software-centric versus hardware approach Joos: This is my fourth company as CEO. What I’ve found along the way is that no matter the size or type of business, there’s a common theme, the business is going through some form of evolution or transformation because the industry they're in is going through an evolution. And today, in physical security, there is a shift to more of a software-centric versus hardware approach, and there’s a shift occurring that’s pulling us to the cloud. I think a key thing here is that while the industry is evolving, we must keep a careful eye on the evolution of the customer because the customer is the one who will dictate the pace of change, and I think that is what a lot of people sometimes lose sight of. Q: It seems Acre is on the path from being a “collection of small companies” to “a collection of brands within a single company.” Joos: I think most people think of Acre as a federation of companies. Acre Security was seen more as a holding company. For me, I think the biggest misconception is just that: “This is just a federation of companies” versus “This is a business.” Acre Security is a business that has a range of portfolios to address key verticals and pivotal business problems for customers. Because of what’s happening now and the market dynamics that are occurring, it ties back to “Who is Acre Security?” We have a clear answer as to where we want to be from cloud access control versus on-premise access control. We have clear answers regarding market segments, visitor management, and intrusion. When you think about it, those are the core areas of our business. Q: What has surprised you the most in your first year or so at Acre? Joos: I think the thing that surprised me the most was how similar the problems are because I was coming into a new industry. It’s surprising how strong a correlation [security has] to other industry transformations that I’ve been a part of. Q: What are the points of differentiation among the various Acre Security brands? Joos: I think if you go back to the history of the company, it was designed to compete. That is, that's how it was set up under the logic of, “If we have three bids in a deal, it increases the odds that we're going to win one of them.” As we evolve, to have sustained scalable growth, it is not just about going shallow and casting a wide net. It’s about creating a concentrated focus. Some of the technology is just inherently older technology. And so for me, it’s about creating migration paths for the customers to move to more modern technology, such as the cloud. I love our installed base. When you think about the cost of acquisition to get a new cloud customer, it costs a lot less when you have an installed base that you can migrate to the more modern solution versus having to spend the money and the sales energy to hunt for that next opportunity. Q: Where has Acre positioned itself in the marketplace? We can take care of your current needs, but we also have a clear migration path to take care of your future needs Joos: If you're ready to go to the cloud, we have an answer for you. If you're not ready to go to the cloud, but you're ready to take more cloud-based applications to continue to evolve, we have an answer for you. If you're not quite ready yet and you're still looking for a market-leading premises solution, we have an answer for you, and we have a migration path when you're ready down the road. So, you have a safe bet with Acre because we can take care of your current needs, but we also have a clear migration path to take care of your future needs. Q: How are you building up your team? Joos: In 2023, we’re getting a lot of core building blocks in place and making investments in people who have experience in this space or aligned industries. It is a balance. I think we need a group that understands the industry and a group that's going to come into it and challenge why we do things the way we do. I think that makes us unique: we have fresh eyes looking at things from a different perspective. With that, you’re naturally going to end up with a better answer to problems because people are comfortable challenging the status quo. Q: How are you seeking to expand your dealer channel and/or transition it from the various dealers “inherited” in previous acquisitions? Joos: The channel invests in Acre Security. Our success is their success, and so what we're proposing to them is a range of solutions that supports their longevity and their financial success. But we also continue to build out our portfolio through organic technology innovation or M&A. We're continuing to make investments in our channel strategy and how our partners interact with us We're continuing to expand their addressable market if they want to make investments with us. We're continuing to make investments in our channel strategy and how our partners interact with us. The design of our upcoming technology right now is built with the channel in mind. We want to ensure that we are not creating any channel conflict or any perceived channel conflict. I think that's usually the worst kind: when it's perceived but not real. You need to be very upfront and clear with communications. Q: What is the biggest challenge in the industry right now? Joos: Companies and customers are looking to embed security into their workflows. What I mean is these are not just standalone solutions anymore. They’re integrating with enterprise resource planning (ERP) and human resource (HR) software systems. In property management, they want it integrated into the fitness center, they want it integrated into the cafeteria areas and the dry cleaners, and so forth. So, this is about an ecosystem, and there are times when we are going to be the core, and there is going to be a lot of technology that is adjacent to us. There are times when we are the adjacency to someone else's core in a smart city or a smart building. This gets to why having an open application programming interface (API) is going to be an important part of the technology evolution. It cannot be a closed environment anymore; that is part of the past. Q: What’s next for Acre? We're constantly evolving our cloud access control as well as our on-premise access control Joos: There is a lot of work going on with integrating the business into a single Acre Security company. This is an investment year for us, we are adding people to our team. We are making a lot of investments from a systems and technology perspective. We have a lot of work right now going into integrating the business from an IT infrastructure perspective and all the tools that we use from an employee perspective. We are making a lot of investment as it relates to the commercial side. You're going to see some next-gen technology coming out from an intrusion perspective. We're constantly evolving our cloud access control as well as our on-premise access control. We're also bringing software applications, too. Q: What is Acre’s “message” going forward? Joos: One of the takeaways for me is this is not the Acre of the past. We are making some bold changes. New things are happening here; you better pay attention because clearly, something is different. I think that's one. I think the second is that as they spend time within us, they're going to realize the wide range of solutions and use cases that we can address, whether you're in access control or cloud, whether you're in intrusion, whether you are in visitor management, or whether you're looking at some network connectivity solutions. The third thing that I think people are going to see is a whole lot of energy as they talk to our people and the passion that you see from the team. If I wrap those three points up in one kind of statement there, I think my goal is that people walk away saying “Something is going on at Acre Security. We better pay attention.”
Matter is a new open-source interoperability standard that will simplify the connectivity of smart home systems, including security. The growing popularity of the Matter 1.0 standard was evident at the large Consumer Electronics Show (CES) in January in Las Vegas, where the standard was heavily promoted by companies including Google, Amazon, and Samsung. A flood of Matter-connected products is on the horizon for ship dates in the second half of 2023. Evolve, and manage IoT standards Creating the standard is the Connectivity Standards Alliance (CSA), formerly the Zigbee Alliance, which changed its name in May 2021. With 300 companies as members, CSA seeks to create, evolve, and manage Internet of Things (IoT) technology standards through a well-established, collaborative process. CSA promotes the benefits of global, open standards, and the value of the IoT to customers and consumers, and seeks to break down the barriers to broad access and adoption of IoT technologies and solutions. Matter The new brand name Matter was launched in May 2021 to designate the standard formerly known as Project CHIP (Connected Home over IP), developed by CSA member companies including Apple, Google, Samsung, and Amazon. There are currently 800 devices and apps certified to the new smart home standard, including various smart home equipment (except video cameras, which will be included in a major release in the fall of 2023). Matter version 1.0 was initial launch in October 2022. Matter 1.0 release Twice a year moving forward, Matter plans a minor release each spring and a major release each fall As part of the Matter 1.0 release, authorized test labs are open for product certification, the test harnesses and tools are available, and the open-source reference design software development kit (SDK) is complete, thus enabling new products to be brought to market. Twice a year moving forward, Matter plans updated releases, a minor release each spring and a major release each fall. Smart home interoperability Currently, a variety of CSA working groups are addressing various aspects of interoperability in the smart home, including issues such as data privacy, security, energy management, and health and wellness, says Christopher LaPré, CSA’s Head of Technology. “Implementing elements requires that the standards alliance be able to multitask on several tracks,” says LaPré. Some development is centering around connectivity and the need for a “hub” to which multiple systems can communicate and incorporate an “identity” to regulate the availability of information to various systems. The standards will enable both do-it-yourself (DIY) systems and devices deployed by professional installers. Addressing privacy requirements The new development will be guided by what installers need to succeed in the home automation" Ecosystems depend on the availability of some type of “identity” to meet privacy requirements. Rules must be implemented across the ecosystem that deploys a “trust system” to ensure privacy. Solving the challenge involves getting all the major players to the table at the technical level to meet the bar from the business and technology perspective. “Integrators and retailers will play a role as Matter continues to evolve,” says LaPré. “New development will be guided by what installers need to succeed in the home automation market.” Matter-certified devices There is still work to be done to expand the 800 certified devices to function throughout the Matter ecosystem and to add new devices over time. One goal is to simplify an integrator’s solution using fewer hubs (and possibly a single hub) to provide a wide variety of services. The timeline of adding new Matter-certified devices may be delayed by the availability of equipment in the global supply chain, says LaPré. Flexibility Multi-admin provides for the simultaneous operation of devices in multiple smart home systems A multi-admin feature of Matter enables more flexibility for multiple ecosystems. A core feature of Matter, multi-admin provides for the simultaneous operation of devices in multiple smart home systems. Accordingly, family or household members could operate the device with the digital assistant or smartphone app of their choice. A bridging protocol helps to tie existing systems together. Amazon, Apple, Comcast, Google, SmartThings, and the Connectivity Standards Alliance came together in 2019 to develop and promote this new standard, joined by fellow Alliance board member companies IKEA, Legrand, NXP Semiconductors, Resideo, Schneider Electric, Signify, Silicon Labs, Somfy and Wulian. Smart device communication Currently, member organizations span all sizes, across a range of business categories. More than 1,700 Member individuals participate in bringing the Matter specification, reference implementations, testing tools, and certification programs to life. Matter's underlying network technologies are Wi-Fi and Thread. Wi-Fi enables Matter devices to interact over a high-bandwidth local network and allows smart home devices to communicate with the cloud. Thread provides a mesh network within the home. Both the Wi-Fi Alliance and Thread Group partnered with the Connectivity Standards Alliance to help realize the vision of Matter.
Case studies
An end-to-end IDIS video solution has overcome performance, quality, and affordability challenges that had hampered public space surveillance in Bristol city center. The upgrade, which tackled a growing list of problems including degraded picture quality, unreliable transmission and data storage, and poor usability, has been completed at Temple Quay and Glass Wharf by KIS Fire & Security. GDPR-compliant video surveillance The successful project is enabling significant operational improvements by the 24/7 security team that manages the site, according to Property Manager, Avison Young. The company reports faster responses to medical incidents and more effective prevention of petty crime and antisocial behavior, thanks to surveillance coverage without blind spots and the ease with which officers can retrieve and export GDPR-compliant video evidence to support police investigations. Temple Quay and Glass Wharf The original video system at the site was almost twenty years old and proving to be increasingly unreliable Temple Quay and Glass Wharf are part of the Bristol Temple Quarter Enterprise Zone which is home to hundreds of businesses, government offices, serviced offices and co-working spaces, bars, restaurants, and residential properties. The original video system at the site was almost twenty years old and proving to be increasingly unreliable, with underground cabling and equipment prone to flooding and cameras producing increasingly poor-quality images. Challenges faced "The problems were made worse by a cumbersome VMS operating system," says KIS Director - Rob Morgan, adding “The prospect of a complete system upgrade seemed daunting because it would need a complete replacement of the backbone infrastructure, cameras, recorders, etc. and a new VMS management system." He continues, "But we were able to satisfy Avison Young with IDIS technology, showing them a major public space system that we’d recently completed for Bristol Zoological Society.” IDIS Center VMS The new solution, managed by the cost and license-free IDIS Center VMS, includes NDAA-compliant 8MP IDIS PTZ cameras delivering superior images at up to 31x zoom; vandal-resistant 5MP IR dome cameras; 8-ch 4K recorders supporting UHD display; a specialist network operator’s keyboard; plus, mountings, POE switches, and all other network accessories. The system is easier to use and gives the security team complete area coverage, including full visibility KIS completed the upgrade ahead of schedule in under four months, with rapid installation supported by IDIS plug-and-play DirectIP® technology ensuring instant and seamless functionality of all devices. The system is also easier to use and gives the security team complete area coverage, including full visibility along – and across – a waterway that runs through the site. Instant device functionality “With IDIS, the instant full functionality of all devices means we can be more certain about completion times, even for major public space projects like Temple Quay and Glass Wharf,” says Rob Morgan. He adds, “The system also comes with extended warranties, and failover protection against loss of data in the event of network instability - for public area surveillance this kind of reliability is essential.” Award-winning solution “Following our successful partnership with the award-winning solution for Bristol Zoo, IDIS was delighted to support KIS with this major city center surveillance project,” says Jamie Barnfield, Senior Sales Director, IDIS Europe. He adds, “Both these projects show video technology at its best, helping to create welcoming public spaces where people can feel safe.”
Completed in 2023, Thanet Parkway Station, the new high-speed rail hub serving the Thanet area in southeast Kent, has implemented a significant infrastructure enhancement: the installation of high-quality parking barriers to optimize accessibility and safety within its premises. Investment in connectivity Thanet Parkway Station, which opened on 31st July 2023, is a testament to the region's commitment to advancing its transportation infrastructure. With a total investment of £44 million secured through a combination of council financing and various building and growth funds, the station addresses the rising demand for efficient connectivity to London and neighboring towns. Swift and convenient travel Furthermore, its ample car park, boasting space for 293 vehicles, serves as an indispensable "park and ride" facility Featuring two expansive platforms capable of accommodating 12-car trains and strategically situated on the high-speed line through Ashford International, Thanet Parkway Station offers commuters swift journeys to key destinations. Furthermore, its ample car park, boasting space for 293 vehicles, serves as an indispensable "park and ride" facility, alleviating congestion in central Thanet and providing convenient access to the surrounding areas. Enhancing safety and traffic flow To enhance safety and streamline traffic flow within the station's car park and adjoining pedestrian and cycleway, Jacksons Fencing was specified to implement a comprehensive suite of parking barriers and demarcation measures. Warden Swing Barriers were installed along the pedestrian and cycleway to regulate vehicular access. These galvanized steel barriers offer a robust solution while ensuring ease of operation for maintenance and emergency vehicles. Safeguarding pedestrian pathways Along the same path, Jacksons Fencing’s timber knee rail fencing served as an unobtrusive demarcation device. This fencing solution, constructed from kiln-dried, pressure-treated timber and galvanized steel straps, safeguards grass verges and delineates pedestrian pathways. Ensuring peace of mind Strategically positioned to enforce height restrictions within designated parking areas, Jacksons’ MaxHite parking height restriction barriers were installed. Crafted from galvanized steel and finished in a highly visible yellow polyester powder coating, the barriers provide durable protection against unauthorized access, while facilitating smooth traffic management. Each installed product comes with the assurance of Jacksons Fencing’s 25-year guarantee, symbolizing a commitment to quality and sustainability. High-quality, sustainable products Commenting on the project, Peter Jackson, Managing Director of Jacksons Fencing, underscored the transformative impact of the enhanced security measures at Thanet Parkway Station, said "As a local supplier, we’re thrilled to have been involved in this project, and it’s great to see that the developers have invested in high-quality, sustainable products, showcasing this project’s commitment to providing a lasting transport solution for the community." He adds, "Beyond parking, the upgraded access control and increased security measures not only enhance safety, but also foster a profound sense of reassurance and pride in the area for all station users."
Delta Scientific, the pioneering manufacturer of counter-terrorist vehicle control systems used globally, announced that on Monday, April 1st, a DSC501 High-Security Barricade stopped an unauthorized vehicle from entering an FBI field facility in Atlanta, Georgia. According to officials, the orange Buick Encore tried to follow an FBI employee’s car into the facility before being stopped by the Delta DSC501 barrier. The driver was then apprehended by special agents who were in the immediate area. Strength and reliability of Delta “Delta has a long history of thwarting attempts by unauthorized vehicles trying to enter facilities where they could potentially cause serious harm to civilians and structures,” states Greg Hamm, Delta Vice President of Sales and Marketing. “We are extremely proud to celebrate our 50th anniversary this year protecting the world’s most important institutions. The strength and reliability of Delta barriers is unrivaled.” FBI field office On June 27th, 2006, the DSC501 was tested to the most extreme parameters on record The DSC501’s protecting the FBI field office are the strongest in the world. On June 27th, 2006, the DSC501 was tested to the most extreme parameters on record. A 65,120-pound dump truck hit the DSC501 at 50mph and was stopped at the barrier. At the time of the test, this would have roughly equated to a K54 rating with the crash energy equaling 54,000,000 foot-pounds. ASTM M50 testing level How impressive is this? The current highest ASTM M50 testing level requires 12,500,000 foot-pounds of energy when impacting the barrier. This is a factor of over 4x which is extremely impressive considering the magnitude of the current M50 test. Contact Delta Scientific if they want to make sure the facility has the strongest, most reliable barriers on the market. They are celebrating 50 years in business in 2024.
Motorola Solutions announced its deployment of 4,000 VB400 body cameras to police forces in Austria. The nationwide rollout will help front-line teams to de-escalate potentially dangerous situations, capture evidence during operations and improve safety and transparency in all interactions. The latest Global Peace Report stated that Austria is one of the safest countries in the world, but according to the Ministry of the Interior, extremism, smuggling, and cybercrime continue to be threats to Austria's security. To meet these challenges, the Austrian government decided to invest in a number of initiatives to increase safety and security in the country, including the deployment of body cameras for the national police. VB400 body cameras They offer a pre-and post-recording ability to help ensure incidents are seized from the start “Body cameras have proven to play a crucial role in helping to improve safety at the front line, while also serving as a valuable source of evidence in criminal cases,” said Michael Kaae, corporate vice president at Motorola Solutions. “We see an increasing demand for video technology, including body cameras, in-car video, and fixed video solutions to help first responders keep their communities safe.” The VB400 body cameras will be provided with VideoManager evidence management software, enabling the secure handling and storage of evidential footage. Officers can easily upload and manage video footage, organized by time, date, and location as part of their existing daily workflows. They offer a pre-and post-recording capability to help ensure incidents are captured from the start. TETRA digital radio technology Motorola Solutions has been a trusted partner of public safety organizations in Austria for over 20 years. All public safety organizations including police, fire brigades, and emergency services rely on the reliable and secure Tetron network, which uses TETRA digital radio technology from Motorola Solutions.
In a landmark achievement for air travel technology, Zayed International Airport has successfully processed over one million passengers through Abu Dhabi’s new terminal since its inauguration on 15 November 2023. This marks a significant milestone in the journey towards enhanced travel efficiency and security, showcasing the power of cutting-edge biometric technology. Building on a long-term commitment to advancing airport capabilities, IDEMIA has been at the forefront of innovation in the UAE since 2011. The deployment of a comprehensive border management solution at Abu Dhabi Airport, featuring the world’s first multi-biometric entry/exit system, has significantly bolstered border security while simultaneously enhancing the passenger experience and throughput. The success of this groundbreaking project has led to its extension to the country’s four other international airports. Rollout of cutting-edge biometrics STJ solution uses advanced facial recognition technology to simplify the passenger venture The Single Token Journey (STJ) solution, a highlight of this collaboration, employs advanced facial recognition technology to streamline the passenger experience. By assigning a unique digital identifier to every traveler, the STJ solution eliminates the need for multiple documents, enabling passengers to move from curb to gate, including the border clearance step, in a record time of just 12 minutes. "The initial rollout of cutting-edge biometrics at Zayed International Airport underscores our dedication to enhancing airport experiences through innovation and technology, ensuring efficiency, convenience, and superior service. Once fully implemented, Abu Dhabi will pioneer as the world’s first airport with biometrics integrated at every stage, ensuring travelers enjoy a seamless, safe, and secure journey," Elena Sorlini, MD and CEO, Zayed International Airport. Efficiency of the STJ solution "We are thrilled to witness the transformative impact of our biometric solutions at Zayed International Airport’s new terminal. This milestone is not just a testament to our successful collaboration with Zayed International Airport but also a clear indicator of our commitment to enhancing the travel experience through innovation." "The processing of over one million passengers since November is a significant achievement for us, and it underscores the scalability, security, and efficiency of the STJ solution. Together, we are setting a new global standard for passenger facilitation," Osama Al Makhamreh, Vice President, Sales – Middle East & Africa, IDEMIA Public Security. Zayed International Airport’s commitment This innovative approach not only enhances security but significantly improves the overall passenger experience. The success of the STJ solution at Zayed International Airport marks a pioneering step towards transforming air travel across the Middle East and potentially the world. The initiative aligns with Zayed International Airport’s commitment to adopting cutting-edge technologies that streamline the travel process, reinforcing the UAE’s position as a pioneering hub for technological advancement and superior passenger facilitation.
Morse Watchmans, the industry pioneer in key control and asset management systems, reports a rising number of international cities and municipalities installing the company’s flagship key control system, KeyWatcher® Touch, to secure the buildings, equipment, and vehicles utilized by various municipal departments. “From public works to waste departments, courthouses, and beyond, the adoption of our KeyWatcher Touch solution continues to resonate positively across so many diverse cities,” said Tim Purpura, VP of Global Sales and Marketing, Morse Watchmans. “We take pride in knowing that our systems are being used to facilitate secure and efficient operations for some of the public’s most critical services.” New KeyWatcher Touch system By implementing effective municipal key control measures, cities can mitigate the risks associated with unauthorized key access while maintaining the operational integrity of public works. Cities and metropolises can set a foundation of trust and confidence within their communities This proactive approach not only safeguards against potential security breaches but also fosters accountability and responsible use of resources among city employees. In this way, cities and municipalities can establish a foundation of trust and confidence within their communities. In one instance, the Walworth County Public Works Department in Wisconsin implemented a new KeyWatcher Touch system after the original key box system failed to adequately support the county’s hundreds of keys for government buildings and county fleet vehicles. KeyWatcher Touch solution After seeing the success of the KeyWatcher Touch solution at the Department of Public Works, other departments within Walworth County have also begun installing their own KeyWatcher Systems. “These boxes are starting to catch on, and departments are really thinking about how they will use them for vehicles and building keys,” said John Miller, Senior Project Manager, Walworth County Public Works. The operational efficiencies of the KeyWatcher Touch solution are also appreciated Across the globe, the operational efficiencies of the KeyWatcher Touch solution are also appreciated. Blacktown City, a suburban community located approximately 22 miles west of Sydney, Australia, implemented a KeyWatcher Touch system at their Main Works Depot to help maintain usage accountability and eliminate the problem of missing or overdue vehicles, machinery, and building keys. KeyWatcher Touch automated control “We manage keys for at least 500 vehicles and machines here at the Depot and each of them has at least two to three sets of keys,” said Joe Haddad, Facility Manager, Blacktown City Main Works Depot. “Without the KeyWatcher Touch automated control and tracking, the job of accurately keeping track of these many keys would be almost impossible.”


Round table discussion
For many years, security systems produced their share of "data exhaust." Every access control action and each video image became a data point to be stored in perpetuity, with no practical way to use the data. More recently, systems have been developed to enable organizations to analyze data from sensors and other connected devices to gain valuable insights into how their systems are being used, to identify potential vulnerabilities; and even to provide insights into broader enterprise operations. We asked this week’s Expert Panel Roundtable: How are data analytics changing the course of the security marketplace?
Headlines of violence in our schools are a reminder of the need to keep educational institutions safe. In fact, if there is a positive aspect to the constant bombardment of headlines, it is that it keeps our attention perpetually focused on how to improve school security. But what is the role of physical security systems? As the new school year begins, we asked this week’s Expert Panel Roundtable: Are schools safer because of physical security systems? Why or why not?
As physical security technologies become more complex, it is incumbent on the dealer/integrator to have the skills and expertise needed to ensure that a system operates smoothly. The value of integrators increasingly rests on the skill sets they bring to bear when installing a system. If the skills are missing, there is a problem. We asked this week’s Expert Panel Roundtable: What missing skills among security integrators can cause problems for customers?
Products


White papers

Improving City Mobility Using Connected Video Technology
Download
Charting The Path To Safe Cities
Download
Securing Unmanned Infrastructure at the Network Edge
Download
Smart And Reliable Rail And Metro Operations
Download
6 Questions To Ask When Choosing A Security System
Download
Effective Access Control For Museums And Public Spaces
Download
Future-proof IP Surveillance For Harsh Environments
Download

Videos
Public security: Manufacturers & Suppliers

Multi-Residential Access Management And Security
Download
Guide For HAAS: New Choice Of SMB Security System
Download
Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
Download
Hikvision: Solar Powered Product Introduction + HCP
Download
Gunshot Detection
Download