IP transmission
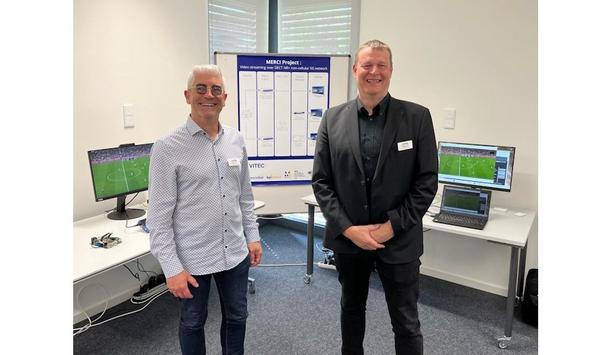
VITEC, a market-renowned provider of IPTV, video streaming, and digital signage solutions, and RFmondial, a specialist in wireless transmission technology, have announced a groundbreaking achievement: the world's first demonstration of ultra-low latency (below 100 ms) video streaming over DECT NR+, the new non-cellular 5G standard. Achieved as part of the Sennheiser-led Franco-German-backed project MERCI, the demonstration took place at a public workshop in Hannover, Germany on April 19, 2024....
DigiCert, a global provider of digital trust, announced the first World Quantum Readiness Day, which will take place on September 26, 2024. This initiative aims to spotlight the critical need for current security infrastructures to adapt to the imminent reality of quantum computing. Quantum computing Quantum computing promises unparalleled computational power and will transform industries by making certain tasks exponentially faster. However, this leap forward also presents significant...
VuWall, a technology pioneer in video wall control systems and unified visualization solutions, proudly announces significant enhancements to its VuStream 150 H.264 HDMI video encoder. The VuStream 150, part of the VuStream series of encoders and decoders, seamlessly integrates with the PAK video wall, KVM nodes, and VuScape controllers, while being centrally configured and managed by the TRx centralized management software platform. Cost-effective solutions "Our commitment to continual enhan...
Durite, pioneers in vehicle safety, lighting, and auto electrical parts supply, have commissioned a new demonstration vehicle designed to bring their range of road safety products closer to fleet operators throughout the UK. The Durite-branded demo’ van is fully equipped with a selection of the company’s latest safety additions, including DVR kits, 4G live-streaming DVR and CCTV kits, AI and Progressive Safe Systems, innovative lighting, and smart telematics tracking. Vehicle...
In an industry breakthrough that will pave the way for quantum computing advancements for Internet of Things (IoT) devices, Telefónica, IDEMIA Secure Transactions (IST) and Quside announce the launch of Quantum-Safe connection for industrial IoT devices. This project is part of a long-term collaboration between Telefónica and IDEMIA Secure Transactions, which has already announced some significant milestones, such as the deployment of the world’s first quantum-safe 5G SIM ca...
dormakaba announces a ground-breaking innovation in sustainable property management: a new fire-tested battery backup for uninterrupted power supply (ED UPS) to door automation (ED 100/250). This innovation marks a significant step for the Scandinavian markets Denmark, Finland, Norway, and Sweden which are the first countries to start with the launch in April and May 2024. Integrated battery backup The outstanding innovation is the integrated battery backup for a continuous power supply in...
News
An upcoming seminar for security professionals, hosted by Synectics on 14 May 2024 in London, aims to help public space operators make the right decisions regarding AI surveillance technology. AI-driven video surveillance ‘Navigating the Future: AI in Public Space Security’ is free to attend and will discuss how AI-driven video surveillance analytics can be used, proactively and forensically to protect members of the public. It is aimed at anyone responsible for security in a public space, from towns and cities, hospitals, and transport hubs to campuses and major event venues. Benefits of implementing AI technologies Jon Squires, Head of Technology Partnerships and Enterprise Solutions at Synectics, said, “We’ve put this event together to delve into the transformative power of AI and how it will shape the future of security and surveillance." "During the day, we’ll discuss the latest real-world applications, the challenges and benefits of implementing AI technologies, and the ethical and legal considerations accompanying its widespread adoption.”
Euralarm urges the European Commission to extend the Article 11(3) exemption of the Batteries Regulation to include smoke alarm devices, carbon monoxide alarms, and gas alarms. These products should meet the following criteria: Life Protection: Explicitly designed to protect human lives within living environments. EN Product Standard: Tested and approved according to valid EN standards. 10-Year Battery: Powered by a portable battery that reliably supplies the device for at least 10 years. Recycling Safety: Easily removable batteries to ensure safe handling in recycling centers. Only products meeting all four conditions should be considered for exemption. Background Portable batteries that users can remove and replace using commercially available tools While it is often beneficial to have portable batteries that users can remove and replace using commercially available tools throughout the product’s lifespan, there are cases where this may not be appropriate and could even compromise user safety and appliance functionality. One such scenario applies to devices like smoke alarms, carbon monoxide detectors, and gas alarms. Portable battery These safety devices are designed for use in residential settings, alerting occupants to fire, smoke, or hazardous gases (especially during sleep) so they can respond appropriately and evacuate if necessary. To ensure proper operation, all these products incorporate a portable battery. Notably, a significant number of these devices in Europe (particularly smoke and CO alarms) come with permanently soldered 10-year batteries. This category of products explicitly serves to safeguard human lives within their living environment and includes: Smoke Alarms (according to hEN 14604) Carbon Monoxide Alarms (according to EN 50291-1) Gas Alarms (according to EN 50194-1) Justification Life-Saving Purpose: The primary function of these devices is to safeguard lives within residential environments. Sensor-Based Service Life: Unlike conventional product design considerations, the service life of these devices relies solely on physical sensors. It is determined by physical conditions and limits. 10-Year Batteries: A significant subset of these devices operates on a single battery throughout their entire 10-year service life. This level of sustainability and efficiency is remarkable. Permanently Soldered Batteries: Given their purpose and longevity, it is neither practical nor necessary for end-users to replace batteries. Consequently, 10-year batteries are now permanently soldered. Safety Risk: Introducing replaceable 10-year batteries would not only be futile but also pose safety risks similar to those associated with hearing aids.
Mayflex, the distributor of Converged IP Solutions, has signed a partnership agreement to become a ‘Value Added Distributor’ for the Ruijie and Reyee by Ruijie brands in the UK. Ruijie Networks is a global industry-renowned manufacturer of Wired and Wireless network infrastructure products and solutions. Founded in 2003, Ruijie has seen steady growth and achieved many accolades in that time and was recognized in the Gartner 2020 Magic Quadrant for its Wired and Wireless LAN Access Infrastructure products. The Ruijie brand is focused on the Enterprise and the Reyee by Ruijie brand is targeted at the SMB market. Significant focus on R&D Ross McLetchie, Mayflex Sales Director commented: “We are delighted to bring the Ruijie and Reyee by Ruijie brands into the Mayflex portfolio. It’s a brand name that might not be that familiar to our customers in the UK, but we’ve been extremely impressed by the quality of the products and the scale of their organization." He adds, "They have an extensive product offering for both wired and wireless solutions, from an entry-level budget switch to an enterprise core data center switch, they can provide a total solution. Ruijie has a significant focus on R&D with a total of eight R&D Centers and as 55% of their personnel are engaged in R&D it’s no surprise that their offering is feature-rich and constantly evolving. With their cloud-based platform that is free for life and with no subscriptions or licenses required, the total cost of ownership is much lower when compared to many of the competitors.” Limited lifetime warranty Ross McLetchie continues: “Customers purchasing Ruijie from Mayflex will benefit from a limited lifetime warranty on all managed switches and all wireless access points and all products will be sold with a 30 day no quibble returns option. Our sales and technical teams have gone through extensive training to ensure that they fully understand the product set and can advise our customers on the best products to suit their needs." He concludes: “We’ve analyzed the range and the market and we will be stocking significant quantities of the key products for next-day free delivery to the UK mainland. To make it easier to get to grips with the range, we’ve created a simple online tool for customers to enter the competitor product codes to find out the Ruijie or Reyee equivalent.”
barox Kommunikation AG, the global manufacturer of professional standard managed and unmanaged switches, PoE media converters, and IP extenders, will be showing their range of Ethernet switches and Device Management System (DMS) VMS integration at the CCTV User Group’s ‘Relentless - A Focus on The Future’ event, 22-24 April, Whittlebury Park Conference Centre. Public Space Surveillance At the event, barox will be showing their support of Public Space Surveillance applications by demonstrating ease and depth of integration to 3rd party VMS control systems, via an unparalleled range of integration plugins; including those available for Genetec, Milestone, Advancis, and Geutebruck. With barox Ethernet switch integration, enhanced diagnostic data showing the status of cameras and switches enables the fast pinpointing of network or device issues, enabling faults and outages to be diagnosed remotely. For example, if a network camera fails to respond, barox switches can be used to select a device and send a re-boot command, saving invaluable device downtime. barox DMS barox DMS tools include PoE monitoring, cable diagnostics, and remote switch traffic monitoring In addition, with barox’s integrated DMS, numerous helpful network monitoring functions allow the visualization and analysis of all hardware and connectivity. barox DMS tools include PoE monitoring, cable diagnostics, and remote switch traffic monitoring where per port live data traffic is shown on a graphical chart, allowing the whole video network and all connected cameras to be analyzed. This key capability stands barox apart from other network equipment manufacturers and has proved to be both valuable and ‘game-changing’ in the management of Public Safety CCTV networks. System performance, management, and efficiencies “While having been established in the DACH region for over 25 years, barox is relatively new to the UK market,” says Sarah Moss, barox Sales Manager UK & Eire. Sarah Moss adds, “We are, therefore, delighted to be joining the established and highly reputed CCTV User Group Conference this year and are looking forward to demonstrating to group members how barox can optimize system performance, management, and efficiencies of video networks all while reducing costs, and health and safety risks.” Innovative switch solutions Peter Webster, MSyI, Director, CCTV User Group & NASCAM commented, "The CCTV User Group is thrilled to welcome barox as an exhibitor at our upcoming event." He adds, "With their innovative switch solutions and commitment to advancing the industry, barox will add tremendous value, fostering collaboration and helping to shape the future of surveillance technology." Relentless event Peter Webster continues, “At ‘Relentless - A Focus on The Future’, attendees will have the opportunity to experience first-hand the innovative range of barox managed and unmanaged industrial media converters, professional PoE video switches, and VMS integration plug-in solutions offered by barox." He states, "We believe that their presence at this event will inspire attendees to embrace the latest advancements in video transmission technology. Together, we are shaping the future of security, and with barox as a key partner, we are confident in our collective ability to drive positive change within the industry."
Global technology, software and engineering pioneer, Emerson will present the future of automation through its Floor to Cloud™ approach and innovative automation solutions at Hannover Messe in Hannover, Germany on April 22-26, 2024. Emerson will demonstrate how real-time visibility and control can drive sustainability, enhance overall equipment effectiveness (OEE) and empower teams using data-informed decision-making. This is the first year Emerson’s booth will be housed in hall 11 at booth C20. Hall 11 is the Automation, Motion & Drives area, bringing together Emerson solutions all in one place. Attendees are invited to experience the impact of Floor to Cloud™ technology through immersive demonstrations. Emerson Floor to Cloud™ solutions A unique PACSystems™ display will monitor the energy use of the Emerson and nearby booths A unique PACSystems™ display will monitor the energy use of the Emerson and nearby booths to highlight how industrial edge control systems, software, and analytics can maximize equipment and resources to continuously optimize operations. Attendees will learn how to create a “machine signature” and how this process extends the equipment lifecycle. Visitors can also create a preliminary project plan using Emerson Floor to Cloud™ solutions to visualize anticipated decarbonization outcomes, cost-savings, and timelines. Experts from the Test and Measurement Business will also be on hand at the booth. Emerson experts will be on-site with solutions from Afag™ ASCO™, AVENTICS™, Branson™, CoreTigo, Movicon™, National Instruments, PACEdge and PACSystems™ brands. In addition to product demos, the booth will have an innovation station where interesting topics will be presented and explained during the show. The interactive hub will feature scheduled showings that visitors can experience for themselves. Presentation and event highlights Emerson will also host a VIP press event at the booth. During the invite-only event, attendees will hear from Emerson thought leaders and get an exclusive look at Emerson innovations in a relaxed atmosphere. Further details on the event will be announced closer to the show opening. Product highlights AVENTICS Series Advanced Electronic System (AES) With Integrated OPC UA The award-winning AVENTICS Series Advanced Valve (AV) system with Advanced Electronic System (AES) is the first pneumatic valve system with an integrated Open Platform Communications Unified Architecture (OPC UA). The AES helps interoperability challenges and accesses data more easily, while the digital twin integration improves productivity efficiency and reduces costs. In 2022, the AVENTICS Series AV system with Advanced AES won an Endeavor IDEA! Award, earned silver in the LEAP Awards, and was named a finalist for the NED Innovation Awards. AVENTICS Series AF2 Flow Sensor AF2 sensors enable rapid intervention if leaks occur, helping optimize energy consumption AVENTICS Series AF2 Flow Sensors have helped plants around the world successfully reduce compressed air consumption and improve energy efficiency. By monitoring air consumption in pneumatic systems, AF2 sensors enable rapid intervention if leaks occur, helping optimize energy consumption, reach net-zero targets, prevent machine downtime and reduce costs. Emerson now offers a high-flow model of this advanced sensor that propels compressed air monitoring beyond individual machines to benefit larger air lines and systems. This expanded capability allows users to easily optimize energy consumption across an entire packaging facility and improve overall plant sustainability. Multimedia Monitoring Solution The multimedia monitoring solutions, including CoreTigo wireless communication, analyze water, compressed air, gases, electricity, steam (WAGES), and other utilities. The Edge Analytics Dashboard measures efficiency, optimizes productivity and avoids or reduces downtime. Emerson experts will demonstrate the multimedia monitoring cabinet solution and the insights it offers, which will support meeting sustainability goals. Movicon.NExT HMI/SCADA Advanced Movicon NExT.AR solves operational problems through visualization tools that allow personnel Movicon.NExT™ HMI/SCADA is a highly modular, highly scalable platform that goes beyond SCADA to solve automation problems for both CPGs and original equipment manufacturers (OEMs), from the single machine level to a complete plantwide IIoT project implementation. Among Movicon.NExT modules, Movicon Pro.Lean™ provides performance data and analytics for evaluations of OEE and Movicon Pro.Energy™ measures and tracks consumption, while the advanced Movicon NExT.AR solves operational problems through visualization tools that allow personnel to evaluate previously unreachable equipment. For maximum flexibility, Emerson also provides Movicon WebHMI, an HTML5-based visualization tool that can be used as a stand-alone HMI product running on Windows or Linux operator panels, or as a Web Client for Movicon.NExT SCADA applications, as well as Connext™, an industrial protocol gateway. PACSystems Panel Industrial edge software and solutions help analyze and solve problems where they occur — at the machine edge. PACSystems Edge Solutions is the most advanced portfolio of edge computing and control systems and includes edge hardware and software that help significantly simplify problem-solving at the machine level and allow easy, cost-effective analytics and communication at the edge. Included in the panel is the PACSystems RSTi-EP CPE200 compact controller family, which delivers large PLC capability in a compact, rugged design. It provides security-by-design, open programming, and open communications built-in, significantly reducing cost and complexity. AVENTICS Series SPRA Electric Rod-Style Linear Actuator A wide range of mounting accessories ensures a simple selection of the right linear motion key AVENTICS Series SPRA electric rod-style linear actuator is an efficient, high-performance actuator that offers improved load capacity, accuracy, and reliability. In addition to outstanding precision and repeatability, the Series SPRA is also extremely versatile and flexible, with a choice of three different screw technologies that allow implementation in a wide variety of (demanding) applications. Compliance with the ISO-15552 standard, easy-to-use online sizing and selection tools, and a wide range of mounting accessories ensure a simple selection of the appropriate linear motion solution for the application. AVENTICS AV Valve Systems AVENTICS Advanced Valve Systems form a reliable basis for both compact handling systems and complex automation solutions. Especially in the area of machine safety, the AV family offers intelligent solutions that significantly reduce effort when creating a safe design. The valves of the AV family — AV03 and AV05 — have set standards with their diagonal spool in both sizes. They are characterized by an excellent volume flow ratio and a record-breaking energy balance. With the serial Advanced Electronic System (AES) interface, the AV valve system communicates effortlessly with modern controllers via all common fieldbus systems. Modular electronics form the basis for high networking, flawless data transmission, and integration into Internet-of-Things concepts. Edge Devices and Software Emerson edge devices combine the best deterministic controllers on the market with secure, nondeterministic controllers for analytics and machine learning algorithms to proactively optimize business outcomes. These rugged devices are designed for remote industrial areas and equipped with vendor-agnostic PACEdge software to safely run nondeterministic applications. This reduces latency and meets all application performance requirements. AVENTICS G3 Electronic Fieldbus Platform AVENTICS valve design of the Series G3 electronic fieldbus forum replaces rooted, hard-wired solutions In highly automated machines, the AVENTICS valve system of the Series G3 electronic fieldbus platform replaces conventional, hard-wired solutions. It integrates communication interfaces with pneumatic valve systems that have input/output (I/O) capabilities. This next-generation electronic platform provides easy access to connections. It is easy to assemble, install, commission, and maintain. The functionality of the G3 enables programmable logic controllers to turn valves on and off more efficiently and transmit I/O data from sensors, indicator lights, relays, individual valves, or other I/O devices on a channel basis over various industrial networks. The G3 has an easy-to-read graphic display, which can be used for configuration, commissioning, and diagnostics. It offers application, performance, and serviceability improvements for Original Equipment Manufacturers (OEMs) and end users alike. Compressed Air Manager The Compressed Air Manager provides visualization and benchmarking for compressed air and gas consumption for a machine, production line, or across multiple sites. A pre-designed Edge-enabled cabinet solution powers the monitoring and serves as a foundation to connect and scale across multiple machines and lines via the AVENTICS Series AF2. The Compressed Air Monitoring App, which comes pre-installed on the Edge Device is easily configurable and continuously monitors and analyses data coming from the sensors. The Compressed Air Manager transforms available data via an embedded dashboard with KPIs where operators can easily visualize consumption trends, costs, benchmarks, and CO2 impact. This data empowers users with greater insights to help reduce energy costs, improve sustainability, and streamline maintenance. Branson GSX-E1 Ultrasonic Welder The welder’s market-pioneering encryption technology ensures data integrity and security The Branson GSX-E1 ultrasonic welder, and the advanced automation systems it enables, help manufacturers improve efficiency and reach sustainability goals. Controls automatically monitor critical weld parameters in real-time, delivering actionable performance and diagnostic data to help determine OEE (overall equipment effectiveness), enable traceability, and optimize maintenance. The welder’s market-pioneering encryption technology ensures data integrity and security. Compared to joining techniques like heat sealing, adhesives, or mechanical fasteners, ultrasonic welders like the Branson GSX-E1 use less electricity, require no consumable materials, and yield less waste, cutting assembly-line carbon footprints. Wireless Automation Solutions Optimize every stage of the manufacturing process with real-time control, monitoring, and data analysis provided by next-generation wireless automation solutions from Emerson and CoreTigo. These wireless automation solutions connect devices and unlock trapped data. The combination of expertise from Emerson and industrial wireless technology from CoreTigo results in a fully connected ecosystem that can reduce inefficiencies and help customers get to market faster. Wireless automation systems feature IO-Link Wireless, a deterministic, highly reliable, and scalable universal wireless communication protocol with low latency (5 milliseconds) and low synchronization rates (tens of microseconds).
Pyronix proudly announces the update of its renowned EURO 46, introducing the EURO 76 product line, marking an important progression in the company’s commitment to delivering customer-focused solutions that reliably address ever-evolving security needs. EURO 76 Laurence Kenny, Marketing Director, said, “The EURO 76 retains all the innovative features that made its predecessor a standout in the security industry." He adds, "With its hybrid capabilities, the EURO 76 seamlessly integrates both wired and wireless technologies, offering unparalleled flexibility in security system installations.” out-of-the-box capabilities Laurence Kenny continues, “We are proud of the fact that our supply chain and stock availability are industry-pioneering, working closely with our key distribution partners. We ensure that our valued installers have the product they need when they need it.” He states, “The EURO 76’s position in the market with a large zone count, superior out-of-the-box capabilities, and an extremely competitive price point, offers installers the perfect solution for their hybrid installations.” Communication devices, expanders, keypads, and readers The panel's 76 zones and 6 areas allow users extensive customization possibilities The EURO range includes a wide variety of communications devices, expanders, keypads, and readers to suit any installation, alongside Grade 2 and Grade 3 options, which allows the EURO 76 to adapt to diverse security requirements with ease. The panel's 76 zones and 6 areas allow users extensive customization possibilities, ensuring comprehensive coverage of large residential properties or a variety of commercial installation use cases. Wireless capabilities Coupled with the wireless capabilities of the panel, installers can easily add the award-winning Enforcer range to the system, simplifying takeovers or expanding systems on maintenance visits with additional wireless contacts, PIRs, or the award-winning CarDefender. “With InSite UDL software, installers can also save time and money with remote programming and diagnostics. This software also facilitates the remote execution of one of the compulsory annual system maintenances, using ARM (Automatic Remote Maintenance),” said Laurence Kenny. Smooth integration Pyronix apps provide a comprehensive connection for remote control, real-time monitoring, notifications The control panel's IP readiness ensures smooth integration with modern networks, delivering convenience and accessibility for users, alongside connectivity with Pyronix's range of smartphone apps, integrating cameras, smart home devices, and security systems on one platform. Pyronix apps provide a comprehensive connection for remote control, real-time monitoring, notifications, and more. Advancing security technology Laurence Kenny continues, “The introduction of the EURO 76 range underscores the dedication Pyronix has to advance security technology and exceeding customer expectations." He adds, "As a company at the forefront of innovation, Pyronix continues to provide evolving solutions that empower installers and users to protect what matters most.” The EURO 76 is available to purchase in distribution.


Expert commentary
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realize, however, that some of these traditional security measures are becoming antiquated and no longer cutting. The now and future of overnight security is in remote guarding. Pioneered by companies like Los Angeles-based Elite Interactive Solutions, which was founded back in 2007, remote guarding is revolutionizing the overnight security business. Minimizing criminal activity Remote guarding is fast becoming the most popular choice among commercial end-user property owners Remote guarding utilizes a combination of cutting-edge technology, “digital guards,” highly trained security agents, and local law enforcement if and when necessary to minimize the potential of criminal activity. For those adequately enlightened to its overwhelmingly impressive crime prevention capabilities, remote guarding is fast becoming the most popular choice among commercial end-user property owners to secure and protect their investments. What Is Remote Guarding? Remote guarding is a revolutionary concept and increasing trend in security systems that utilize a combination of methods to effectively analyze potential threats to property. Cameras and/or other monitoring devices running highly advanced algorithmic software are installed in strategic areas or vulnerable places onsite and remotely located security agents are immediately notified of any activity within a designated perimeter of the property. A blend of AI, cybersecurity, and video analytics When properly deployed by an expert provider, the technology stack includes a proprietary blend of video analytics, artificial intelligence, cybersecurity, and more. Done right, “noise” is effectively filtered out, allowing agents to act on legitimate alerts and achieve zero false alarms communicated to first responders. Today, there are a lot of terms and descriptions tossed around about remote guarding, remote video, virtual guarding, etc., but those attributes must be present to represent the true definition of the offering and its many virtues. Realtime situational awareness Many systems have a two-way speaker that allows the security agent to give a verbal warning When specially trained security agents are alerted to trespassers, possible intruders, or other suspicious activity, they analyze the situation in real time and determine the necessary level of action. Many systems have a two-way speaker that allows the security agent to give a verbal warning, known as a voice-down, to the individual(s) that they are being watched. Most perpetrators, often believing the response is emanating directly from security personnel on the property itself rather than from a remote command center, flee immediately. However, if the threat persists, the security agent enlists local law enforcement to get on the scene. Customized remote guarding When properly deployed, remote guarding systems are also customized to specific properties. A team of consultants visits the client’s property to evaluate its vulnerabilities and where to best place cameras and/or other monitoring devices for system efficacy. Traditional Security Shortfalls According to Keith Bushey, a retired commander for the Los Angeles Police Department, there is much frustration between law enforcement officers and potential victims of crime due to the historically unreliable performance of traditional burglar alarm systems and central monitoring stations. He states about 90% of security-related calls are false alarms, a problem that has been well-documented through the years. Onsite challenges When a legitimate emergency does occur, the perpetrators have often already done their damage When a legitimate emergency does occur, the perpetrators have often already done their damage and/or escaped by the time law enforcement arrives. Onsite security guards are not the remedy either as they bring their own set of issues and challenges. Unexpected costs Traditional security systems can also have unexpected costs. The cost is not only in the security guards’ paycheck or the cost of the equipment itself. The cost comes when an actual incident occurs. In worst-case scenarios, the security guard(s) are injured, the business suffers inventory loss, and/or damage is sustained to the property. The medical and other costs for the security guard(s), the loss of inventory, property damage, deployment of law enforcement resources, and possible fallout of legal expenses all add up. Even in the best-case scenario, false alarm expenses incur if law enforcement is dispatched. These, among many others, are some of the primary issues that remote guarding resoundingly answers as a superior alternative. A Bounty of Benefits Remote guarding systems have been proven to cut costs and be more effective than traditional security systems. Even though the monthly monitoring costs of remote guarding are significantly higher than traditional intrusion detection system monitoring, the much higher effectiveness in crime reduction, elimination of false alarms, and augmenting or replacement of manned guards result in a substantially higher return on investment (ROI) to the end user. Easy tracking of threats The security cameras already have their image captured on record, making them easier to track down For example, case studies have demonstrated reduced security costs for clients by 60%, on average. These reductions have come from the costs of security staff, inventory, or property loss, plus saving money on insurance premiums and deductibles. The nature of remote guarding reduces the risk and costs of false alarms, with professional security agents able to determine an actual threat before law enforcement is called. In a rare instance when a perpetrator escapes before law enforcement arrives or can detain the individual(s), the security cameras already have their image captured on record, making them easier to track down and identify. Reduction of false alarms The significant reduction in false alarms is greatly appreciated by law enforcement, as it allows them to focus on real emergencies or crises. Better relationships are also developed between clients and law enforcement, as remote guarding systems are highly reliable in providing accurate and real-time information to officers as they approach the scene. In short, it assists law enforcement in doing their job more effectively, as well as more safely thanks to having eyewitness information before engaging in an active crime scene. Partnership When you combine the decreased cost with the increased efficiency and success rate, it is easy to see why many commercial end-user property owners across the country are making the shift to remote guarding. It’s also an outstanding opportunity for professional security dealers and integrators to partner with a remote guarding services provider to bring a superior solution to their end customers and pick up a recurring monthly revenue stream in the process.
The autumn equinox, which marks the start of autumn, occurs this weekend on Saturday, September 23. With darker evenings ahead, the experts at ADT have shared five ways to maximize your home's security. Author's quote Michele Bennett, General Manager at ADT UK&I comments: “Opportunistic thieves use darkness to their advantage, so it’s no surprise that the number of burglaries committed increases when the darker nights draw in." He adds, "Our 2022 burglary report found that burglaries are most common at night, with 58% of burglaries occurring between 6 p.m. and 6 a.m. Taking steps to optimize your home’s security before the clocks go back this year will provide reassurance that your property is as secure as possible.” Five ways to secure your property: Get a monitored alarm installed: A visible alarm system is a strong deterrent to potential burglars, as criminals are less likely to target a home that is protected. In the event of a break-in, a monitored alarm will alert you, your keyholders and depending on the package you take out, the police, ensuring a swift response to an alarm activation. Light up the dark: Well-lit exteriors make your home less appealing to potential intruders. Install motion-activated lights around any entry points, particularly porches and gardens, which alert you to movement on your property. This will also prevent burglars from operating under the cloak of darkness and increase the chance of a passerby spotting suspicious activity. Trim your garden landscape: Thieves look for escape routes and hiding spots when deciding which homes to break into, making gardens with high, overgrown hedges more likely to be targeted. This is especially true in the darker evenings, so be sure to give your garden a thorough tidy-up to make your property less likely to be targeted. It’s also advisable to ensure any tools are locked away in sheds and garages that could assist a burglar such as ladders, or a garden spade to force entry. Be smart with your lights: Using smart plugs allows you to turn on a few well-appointed lights and radios or televisions from any location from your phone. Used in conjunction with an outdoor camera or video doorbell, you can have lamps plugged into smart plugs come on when motion is detected. Programming lights to come on at different times throughout the night will help to deter burglars by making your property look occupied. Purchase a smart doorbell or outdoor camera: Smart doorbells are an effective way to deter burglars as they provide evidence in the event of a break-in, package theft, or other suspicious activity around your home. They also notify you when someone is at your door reducing the chance of you being caught out by a late evening or early morning robbery. Further encroachment Smart doorbells also act as a deterrent to unscrupulous door-to-door sellers and con artists, as video footage is recorded. In the event of a late-night door knock, you can see and speak to whoever is at your front door, without having to open the door. ADT’s new outdoor camera also has two-way audio and a high-pitch deterrent siren so you can warn off anyone from your property to deter any further encroachment.
Daniel May of Consort reviews the integration of access control systems in healthcare settings, outlining the benefits and key considerations decision-makers must make throughout product specifications. From patient safety and traversal to the protection of sensitive data and pharmaceuticals, healthcare environments are faced with several operational challenges. And where security remains at the forefront of decision-making, modern access control systems may often hold the answers. Physical security systems Hospitals in particular have developed into multi-faceted spaces that house hundreds to thousands of patients, staff, and visitors at any one time. In England for example, research has found in the three months leading to June 2023, an average of 44,626 people visited major hospital A&E departments each day, with over 16 million attendances typically recorded over the course of a year-not to mention an additional nine million logged at other minor units. For any building, this level of sustained footfall can request severe security difficulties For any building, this level of sustained footfall can invite severe security tests. With that, the need to deploy effective physical security systems in healthcare is clear. And so, as access control continues to become more readily adopted and new products enter the market, decision-makers are reminded to consider the requirements of their building, ensuring they select the solutions most suited to their settings and budget. Security controlled Patient safety will always remain the top priority in healthcare settings, and where matters of health and social care come into question, a diverse set of professional regulatory bodies are tasked with setting and maintaining high standards. When it comes to healthcare premises specifically, patient security and perimeter security often come hand in hand and are amongst the most pressing of challenges that decision-makers must face. To help address operational planning and potential design concerns in the NHS, the Health Building Note (HBN), provides general design guidance for healthcare buildings under HBN 00-01-citing the use of access control measures as a way of maintaining security and protecting the safety of patients, staff, and visitors. Use of access control Hospital buildings control varied levels of access for a number of security purposes Hospital buildings, for example, must control varied levels of access for a number of operational and security purposes. Routine scenarios exist where vulnerable patients are under monitoring and thus refrained from exiting the premises for their own safety, while at the same time, permitted staff must be able to reach their patients and medicines when required. For this, the use of access control is key. Equally, access credentials can also help management teams keep track of those who may be entering or exiting rooms with equipment and pharmaceutical supplies, deterring any unwanted visitors and opportunists in the process. Incorporation of access control systems On a similar note, regulations have set a minimum standard for how personal data should be stored and managed in healthcare environments, giving decision-makers an added responsibility to regulate staff-controlled areas with patient medical records. While instances of personal data breaches are rare, healthcare facilities and professionals are at legal risk should confidential data be found misused or missing. As such, the incorporation of access control systems has become essential in keeping data storage areas secure, with intuitive online systems capable of permitting access to staff with the correct credentials while simultaneously tracking who has requested clearance at digital entry points. HBN guidance Healthcare experts are better fitted to control the sheer volume of people entering and exiting To function effectively, healthcare facilities must always be perceived as safe places by the people who reside within them, and as HBN guidance implies, a unified physical security system can help address key safety and security concerns while enhancing patient and staff experience. Opportunely, access control systems are more accessible and adaptable than ever and combine several technologies such as mechanical locks and automatic doors with electronic access credentials in the form of smartphone apps, badge readers, and biometric scanners. By integrating these systems into the building’s existing infrastructure, healthcare professionals are better equipped to control the sheer volume of people entering and exiting the premises without impairing the general flow of movement and coordination around the facility. Better by design Despite the clear benefits offered to healthcare facilities, there are a number of considerations to be mindful of when choosing an access control solution. Poorly implemented systems can have an adverse effect on security and functionality - quickly costing healthcare organizations time and budget to rectify and replace the inadequate products that don’t meet the building’s requirements. For that reason, decision-makers and design teams are reminded that there is no single solution that fits all healthcare buildings. As such, it’s crucial for decision-makers to understand the systems that are being put in place throughout each of the touchpoints in their facility. Clear collaboration is required during periods of specification, where together, teams can ensure the selected product works on all angles, from meeting fire safety and sustainability standards to aesthetics and scalability. Modern access control products Scalability is a key area that decision-makers must review when selecting access control systemsFrequently overlooked, scalability is a key area that decision-makers must review when selecting access control systems. Such is their diverse nature; healthcare facilities can often change and develop as years go by, and by selecting a system that facilitates growth, such as a cloud-based solution-security and efficiency is long-established. While modern access control products are known for seamless integration, there are some systems that may restrict the ability to use different vendors throughout the remainder of the building’s infrastructure. This, in effect, causes a monopolization of products throughout the estate, which can have an adverse effect on growth by increasing costs and reducing the levels of service associated with the security system already in place. Improve security and safety A scalable and reliable access control system will continue to improve security and safety by adapting to a building’s new requirements-and all while having minimal impact on its operational network. And so, while technology will no doubt continue to influence and transform the access control market, healthcare facilities and their professionals must continue to remain educated on their own systems, ensuring they have the best options in place to keep their patients, staff, and visitors safe and secure for years to come.
Security beat
For an enterprise, addressing cyber security requires that stakeholders have immediate access to critical information compiled from multiple sources and presented where and how they need it. Various data sources monitor the cyber security status of a company’s computer systems to provide real-time visibility. Aggregating that data into visual dashboards and presenting it to operators enables any cyber security problems to be flagged quickly and resolved. Software system enhances cyber security Userful Corporation provides a software system that enhances cyber security operations for an enterprise Userful Corporation provides a software system that enhances cyber security operations for an enterprise, enabling stakeholders to envision various cyber security factors, such as application security, network security, cloud security and IoT (Internet of Things) security. The software system empowers operators to respond more efficiently. Working in conjunction with a company’s existing IT infrastructure, Userful software combines datasets from diverse systems into a visual format and delivers the information to a desktop computer, a video wall, or even to a home office. Real-time visibility “It provides a new dynamic to how cyber security issues are resolved,” said Shane Vega, Userful Corporation’s Vice President (VP) of Product Marketing, adding “The individuals who have flagged a cyber security issue may not be the ones to respond. Having real-time visibility provides more value to the overall response.” A typical cyber security operations center resembles a physical security command or emergency management hub – large video walls, individual desktop workstations, and operators that need to share information and respond quickly to any incident. Userful’s software helps in managing operations centers Userful’s software manages how data is presented in an operations center environment, without relying on proprietary hardware, operating outside an end-user customer’s IT infrastructure. Managing operations centers is a core offering for Userful Corporation, including command centers of all types, from traditional network operation centers to emergency network systems to security systems. The ability to use one software system throughout an enterprise is appealing to companies that have historically grappled with proprietary and siloed systems. Solutions that are easy to deploy, manage and scale Cyber security professionals need solutions that are easy to deploy, manage and scale" “We are a platform that can be utilized across the enterprise,” said Shane Vega, adding “Cyber security professionals need solutions that are easy to deploy, manage and scale, so they can manage all the threats every day.” Compiling and displaying information to an operations center has historically involved silos of proprietary audio/video (AV) hardware. Ironically, the hardware approach presents cyber security risks that undermine the very mission of protecting a company’s data and networks. The proprietary systems operate outside the company’s network infrastructure, and IT professionals do not have visibility into the systems. Security Orchestration, Automation and Response (SOAR) Instead of hardware, displaying information on Security Orchestration, Automation and Response (SOAR) can be accomplished using software running on off-the-shelf components, managed by the IT department and featuring all the cyber security protections required, throughout the enterprise’s network infrastructure. SOAR includes threat and vulnerability management, security incident response and security operations automation, enabling companies to collect threat-related data from several sources and automate the responses. Cyber security threats Possible threats might include an influx of packet generation, malware, someone seeking access to the network, or a malicious email. Various tools manage each threat, and each must be visualized. Because the threats are related, a comprehensive dashboard enables operators to create parallels and respond more efficiently. The software-as-a-service system ensures that all software is updated and can operate on the latest hardware In the Userful AV-over-IP scenario, an IT department takes full ownership of the computers and subsystems installed on the network. The software-as-a-service system ensures that all software is updated and can operate on the latest hardware. Companies always have an ecosystem of interconnectivity. Single platform/solution The single platform/solution also extends beyond operations centers to include meeting rooms and digital signage. All images are captured using existing protocols, such as Real Time Streaming Protocol (RTSP), HTTP Live Streaming (HLS), Web Real-Time Communication (WebRTC), and so forth. In contrast, the AV industry is hardware-centric and has been known to circumvent software approaches in order to justify selling more hardware. AV systems typically operate in terms of pixels rather than bytes of information and use proprietary software. Companies always have an ecosystem of interconnectivity Different departments in a company have historically installed their own specific AV systems, based on proprietary hardware, so that each department is siloed from the rest of the organization. Dangers of random hardware on a network Random hardware on a network, beyond the reach of the IT department, can provide access points to the network for hackers and other cyber security threats. Each proprietary hardware system exists outside the existing security protocols of the enterprise and each represents a cyber security vulnerability. Some companies end up with five or six different operations centers that involve three or four manufacturers, all siloed. Software versus hardware Our biggest challenge is to get people to understand what is possible with software versus hardware" “Our biggest challenge is to get people to understand what is possible with software versus hardware,” said Shane Vega, adding “The industry is inundated with hardware, and the risk is the unknown. Customers may not be familiar with a software solution that can accomplish what they have historically depended on hardware for.” Userful Corporation works through channel partners (integrators), who assemble complete systems using Userful software and other components, such as video screens, large-format commercial displays, groups of tiled displays, projectors – any type of display with an input. Corporate policy specifies security at every level Userful’s corporate policy specifies security at every level, including user authentication, encryption, endpoint security, air-gapped servers, information security policies, General Data Protection Regulation (GDPR), and a solution built on industry-leading IT standards. To spread the word about Userful Corporation’s capabilities related to cyber security, the company will be participating in Infosecurity Europe 2022, taking place from June 21 to June 23, 2022 at ExCeL, London, United Kingdom (UK).
The next chapter of the Pelco saga began in May when Pelco Inc. was acquired by Transom Capital Group, a private equity firm, from Schneider Electric. Since the acquisition, Transom Capital has been working with Pelco’s management and employees to define and direct that next chapter. “The more time we spend with the company, the more excited we are about the opportunity,” says Brendan Hart, Vice President, Operations, Transom Capital Group. In addition to his position with Transom, Hart has taken on an interim line role at Pelco as Vice President of Product and Strategy. After helping to oversee Pelco’s rebuilding phase, he expects to step away from daily involvement over time. “We have gained an appreciation for nuance [since the acquisition closed],” he said. “The channels, the relations, how people buy in this industry are very nuanced. Who’s gone where and who’s done what? The interplay of hardware and software. We have gained appreciation for the nuance. And we need to be surrounding ourselves with people who know the industry, who know the multi-dimensional areas.” Transition from analog to IP systems We have to focus on who our customers are specifically and understand their needs” It’s a “transformative moment in the industry,” says Hart, given industry changes such as price erosion and the transition from analog to IP systems. “We are about to go into the world of added intelligence. It’s an interesting time to buy a security company.” Hart says the Pelco brand still has value: “The market is rooting for us.” There is also a strong portfolio of people and products to build from. Pelco maintains its headquarters in Fresno, Calif., and has a presence in Fort Collins, Colo., near Denver, and a sales office in the New York area, not to mention many global employees who work remotely. A new CEO is being recruited; otherwise, “we have a great executive team” in place, including Brian McClain, COO and President, says Hart. “In defining the new company, we have to decide first and foremost what we want to be,” says Hart. “What can we provide customers? We have to focus on who our customers are specifically and understand their needs and use cases.” Part of defining the new company is to become more aligned with a specific set of verticals that fit with Pelco’s capabilities (although they are not saying which verticals those are yet). However, “we can’t ignore what we are today as we make the transition,” says Hart. Innovation in products We want customers to see innovation in products to a point when people will say ‘this is Pelco’" “We have to let the products and experience speak for themselves. We’re focused on getting our ducks in a row and going in a new direction, but actions speak louder than words,” he says. The changes will be “more organic;” don’t expect to see a big announcement. “We want customers to see innovation in products and customer support and get those things to a point when people will say ‘this is Pelco,’” says Hart. Although not exhibiting at GSX, I found Pelco occupying a meeting room near the show floor. The room gave the company a chance to respond to integrators and consultants at GSX who had questions about what was going on with the acquisition. “Everybody is rooting for us, and we wanted the ability to get out and say ‘we’re here, we’re doing things, and we’re excited about the future,’” said Stuart Rawling, Pelco’s Vice President, Market Strategy. “This is a time for people to come and see us who maybe haven’t seen us in a while.” By ISC West in the spring, Pelco expects to have a clear message of who they are and where they’re going, he says. Aligning needs of end user “We are excited about the work we are seeing internally,” which includes “aligning resources in the right way,” says Rawling. “The fruits of the labor are being seen internally now. We will be launching new products in the next eight months, although there will not be a defined moment in time when we say ‘this is it.’ It will just be happening. Next year will be an exciting time industry-wide, and product-wise, and Pelco will have a strong voice. Brendan and team have kept us extremely busy,” says Rawling, who also was part of Pelco in the “glory days” before the acquisition by Schneider Electric. We’re so optimistic, when you combine the people and the brand and what’s happening the market” “The work product has been so transformative mindset-wise for the employees. Everybody has had the opportunity to talk to the [new] owners about what type of company we are. We can set our own vision and get reenergized and get back to the core belief of what Pelco was and what it should be. We are the master of our own destiny, aligning needs of end user with the products we can deliver. We are putting the right processes in place that work for this market. It is an exciting prospect.” In the new era, Rawling expects to target marketing more toward end-users, because they have more influence on product selection than ever before, he says. End users often learn about new products online, so Pelco will be looking to target its marketing toward educating various vertical markets about available technologies and their use cases. “We’re so optimistic, when you combine the people and the brand and what’s happening the market,” says Hart. “We have to do the work. We’re excited about what we are seeing internally.”
Choosing the right server for a video surveillance application comes down to one question: What does the customer expect from the system? Is it a retail location with two cameras that only needs video stored for 24 hours? Does the system need failover protection? What are the ramifications if a system goes down? Does business have to stop? How fast does the customer need to have access to video? Is it a regulated industry where immediate access is a requirement? How mission-critical is the video system to operations? Mission Critical Video Surveillance Solutions Such questions can point video system designers to the right technology for an application, and a manufacturer and reseller with a wide product offering ensure that the perfect solution is available and can be shipped quickly. It’s important to remember that this is not a “one size fits all” marketplace. Data capture form to appear here! Questions need to be asked on what an appropriate server solution will provide for the customer 1) JBOD - It stands for "just a bunch of disks" and refers to a collection of hard disks that have not been configured to work together. This approach is typical of stand-alone systems such as a retailer who has one or two cameras recording locally at a remote location, and who have a tolerance for occasionally losing video footage. 2) RAID 5/6 is a redundant array of independent disks in which data is stored across all the disks. The configuration provides more redundancy and reliability, better balance of disk usage, and more throughput and performance. RAID 5/6 is a redundant array of independent disks in which data is stored across all the disks 3) SAN or storage area network is a type of centralized storage providing enhanced accessibility to disk arrays. SAN provides high performance but is not as easy to expand. It is also less expensive than NAS systems. 4) NAS or network-attached storage is another type of centralized data storage. NAS systems are networked appliances containing storage drives. Benefits include faster data access, easier administration and simple configuration. NAS systems are easier to expand than SAN but provide less performance. NAS systems fit well in situations where customers have massive storage needs (or expect to in the future.) These are applications with lots of cameras and a need to retain high-frame-rate video for 180 days or longer. Typical uses include sports arenas, large cities, universities, corporate campuses and airports. Immediate Access To Video Highly available systems, such as SAN or NAS, are needed in any regulated industry. For example, in the cannabis grower market, an end user might need immediate access to video to show a compliance regulator. Gaming is another market in which immediate access to video is critical, and, for example, if a video system goes down at a table game, the gaming has to shut down, which is an expensive prospect to the casino. Therefore, reliability is critical. Video’s benefits beyond safety and security can also help to justify the costs of more expensive system Importance Of Video In Risk Mitigation In some instances, video is used primarily to manage risk, for example in litigation (or to avoid litigation) in a slip-and-fall claim or other court action. This is referred to as Loss Prevention. The ability to save thousands of dollars (or millions) by averting an expensive legal verdict can go a long way toward justifying the costs of systems. Video’s benefits beyond safety and security, such as for marketing and business analytics, can also help to justify the costs of more expensive systems. Identifying The Right Video Server Equipment Offering a variety of choices, and adapting those systems to specific applications, ensures customer satisfaction “A tradeoff of cost and needed functionality is at the center of decisions when buying server systems for video applications,” says Tom Larson, Chief Technology Officer, BCDVideo. “Identifying specifically what the customer needs from the system, and how important it is to meet those needs, points to the right choice in video server equipment. "Various technologies have advantages and some downsides, and it is the customer’s need for those advantages (and tolerance for the downsides) that determines which server equipment is right for the job.” Offering a variety of choices, and adapting those systems to specific applications, ensures customer satisfaction. The systems builder can help integrators analyze the site and project requirements and translate those into the right equipment and networking choices. What does the customer need and how much are they willing to pay for it? The real determination is “how important is the video?”
Case studies
Chopin Airport in Warsaw, named after the famous Polish composer Frédéric Chopin, has recently undergone an impressive improvement in acoustic technology. System features The installation of an extensive Praesensa system from Bosch Building Technologies marks a turning point in the way information and music are transmitted and played in the airport building. The new system features advanced loudspeaker technology and a high level of automation, providing outstanding sound quality and clear, crisp voice transmission, which is of great benefit to the operator, passengers, and ground staff. Innovative technology for precise communication It uses LS1-OC100E-1 hemi-directional ceiling loudspeakers and LC1-UM12E8 built-in loudspeakers The new passenger information system is based on the Praesensa solution from Bosch. It uses LS1-OC100E-1 hemi-directional ceiling loudspeakers and LC1-UM12E8 built-in loudspeakers, which ensure that passengers at every gate are addressed with pinpoint accuracy and excellent intelligibility. Text-to-speech solution By integrating a text-to-speech solution from a third-party provider, the flight number, airline, destination, and boarding information are automatically retrieved from the central computer at Chopin Airport and reproduced in synthesized voice information. These are output in Polish and English as well as other available languages, achieving a previously unattainable sound quality. The result is a significant reduction in the workload of airport staff. Overcoming old challenges The modernization of the public address and voice alerting system was urgently needed The modernization of the public address and voice alerting system was urgently needed, as the old analog system had reached its limits. Information was often lost in an indistinct fog of sound, and manual announcements of boarding information were both time-consuming and labor-intensive. Enthusiasm for efficiency and quality The integration of the new system into the airport's existing infrastructure went smoothly, which significantly shortened the installation time. The automation and increased efficiency provided by the Praesensa system is appreciated by both staff and passengers alike. The scalability of the system ensures its suitability for future developments and requirements. “Chopin Airport now has a state-of-the-art public address system. The fact we could build on the existing IP infrastructure significantly reduced the amount of time for the installation work,” says Józef Bycul, Project Manager at Bosch Building Technologies.
A Government of India-owned multinational oil company with a registered office in Mumbai is ranked amongst the Fortune Global 500 list of the world’s biggest corporations. Owing to its consistent growth in refining capacity, the corporation is expanding at a rapid pace. Corporation challenges As a rapidly growing corporation, multi-location offices are a necessity. They have two large sheds within some distance from each other. Their other offices geographically away but in the same city had to be connected with the same telephone network. Multi-location communication can prove to be an expensive affair if communication devices are not chosen wisely. To elaborate on their challenges: Transition to modern communication with existing Infrastructure: Their investment in existing infrastructure needed protection while also a provision had to be made to modernize the communication using existing infrastructure. Managing different protocols: Interface with existing and different telecom networks requires managing different protocols, which can be cumbersome, time, and energy-consuming. Requirement of modern phone features: They required advanced features like Abbreviated Dialing, Call Pick Up, and Internal Call Restriction, to become efficient in day-to-day operations. Matrix's solution The solution offered was based on the fundamentals of Multi-location communication solutions Matrix Comsec in partnership with SMB Automation analyzed the challenges of communications and crafted a solution that was the best fit. The solution offered was based on the fundamentals of Multi-location communication solutions. This included the Matrix range of IP-PBX - ETERNITY PENX6SAC, VoIP - FXO - FXS Gateway - SETU VFX808 that optimized the feasibility of communication and helped the firm become more efficient. Products used The IP-PBX included ETERNITY PENX6SAC. This enabled them access to 4G VoLTE ports, up to 100 IP users, LDAP Client support, and much more. The VoIP - FXO - FXS Gateway included SETU VFX808 which enabled them a smooth transition to modern communication while maintaining existing infrastructure through features like 9 SIP accounts, peer-to-peer and proxy calling between distant locations, etc. The IP phones included SPARSH VP510E and SPARSH VP210. This came with features like an LCD Graphical display, Context-sensitive keys, Built-in 16 DSS Keys, Polyphonic ring tune, and much more. Application diagram Results The solution so implemented enabled the geographically distant properties to work as a single communication platform and proved to be beneficial in more than one way. The Hybrid IP-PBX enabled them to universal Network Connectivity through PSTN, GSM, and VoIP connectivity, LDAP Client Support to centralize and ease phonebook management, Logical Partitioning that prevents the conduct of any legal offenses related to Telecom regulations, and much more. The VoIP - FXO - FXS Gateway enabled them, VoIP access to traditional PBX, Multi-site connectivity with centralized telecom management, Next-generation conveyance facilities like call detail records of up to 2000 calls, Secure communication bridging with VoIP security over SRTP/TLS encryption, etc. The IP desk phones helped provide advanced features like Call Pick up, Call Forward, Call Waiting, and Call Transfer along with an Intuitive interface, that enabled employees to become efficient as well as enhanced user experience.
The proven “CAT” gaming analysis solution from German casino expert Dallmeier is also available for Sic Bo, in addition to Baccarat and Black Jack. The video-based solution offers a whole range of analysis options with which casino operators can increase the “game pace”, combat fraud, and gain valuable insights into the gaming action through real-time data collection. Optimization challenges Optimizing the gameplay at Sic Bo tables poses no small challenge to casino operators. These include potential cheating attempts, difficulties in tracking results, and operations such as late bets. Above all, however, gaming managers benefit from collecting and analyzing data that can be used to increase the game pace and optimize the efficiency of tables and dealers. “It's all about the data” Real-time tracking of important data and processes The information that can be used to optimize the gameplay at the Sic Bo table is manifold The information that can be used to optimize the gameplay at the Sic Bo table is manifold. For example, “CAT for Sic Bo” precisely records the game pace of each table based on the times for placing the bets, game phase, and payout and thus makes the performances of tables and dealers comparable. Additional information such as which fields are the most popular, information about the value of the top chip for quick identification of “high-value” bets, objective tracking of “late bets” and other events that regularly lead to discussions between players and casinos complete the portfolio. Data points from existing sources CAT for Sic Bo combines data points from existing Sic Bo consoles with CAT data captured by AI cameras above the table. In this way, data from all participating tables can be collected together and evaluated centrally. This can either be done via the Dallmeier SeMSy® casino software or the data is exported as a CSV file and can then also be evaluated by any other system. Automated Business Intelligence for the Gaming Manager This centralized capture and analysis of data provide gaming managers with insights that previously had to be laboriously collected manually by the PIT manager or were not accessible at all in a highly efficient and automated manner. This opens up a completely new field for gaming managers to optimize the profits of their Sic Bo tables: From a higher game pace to the objective evaluation of dealer performance, support in the fight against fraud to the data-driven optimization of table layout, placement, minimum bet levels, monitoring of compliance rules or promos.
Athena Security’s Concealed Weapons Detection System was selected by Champions Club Texas to protect patrons, members, and staff at a first-of-its-kind hospitality destination in Houston that features a full-service hotel, lounge, and bar with Southern-inspired cuisine and private-membership poker. Located in Houston’s expanding Westchase community, Champions Club Texas is celebrating its grand opening as a destination offering something for everyone, from business travelers seeking comfortable accommodations with well-appointed amenities to locals looking for a unique night out. Weapons detection system Athena's Concealed Weapons Detection System (WDS)/Walk Through Metal Detector is engineered to detect a wide range of mass casualty threats like handguns, shotguns, and rifles without requiring individuals to stop as they pass through the detector. There is no need to have individuals remove phones, wallets, or other extraneous items from their pockets due to the proprietary multiple-sensor detection method. The system adheres to Federal Standards while allowing both auditory and visual alert options, as seen in the best practices of Homeland Security for WDS. The concealed weapons detection system is designed to scan walking at an average speed of one person per second. Unintimidating approach Athena Security is a solution that detects weapons upon entry and is one of the many layers of security “At Champions we are raising the bar in hospitality and gaming, and that includes ensuring the most comfortable and safe atmosphere for our valued customers,” said Trent Touchstone, Director of Security, Champions Club Texas. “Athena Security is a solution that detects weapons upon entry and is one of the many layers of security protocols in place at Champions that improves the operational efficiency of our security team as a workforce multiplier.” Athena Security’s low profile, unintimidating approach is a welcome differentiator from historic metal detector tech by eliminating the need to check cell phones and keys, allowing for a better flow into the venue. Modest-full time security team Advanced analytics and management protocols allow for deep visibility and flexibility to maintain staffing levels providing the highest level of safety. Touchstone, a 28-year veteran of the United States Marshals Service Chief with a long history of threat analysis, notes that given the hotel and membership club will require 24/7 attention with a modest-full time security team, he appreciates Athena Security’s ability to provide a feature-rich entryway security experience with the ability to automate and accomplish so much remotely.
Ipsotek, an Eviden Business at Atos Group, has announced that it was appointed to provide its AI video analytics technology at the soon-to-be-opened new Midfield Terminal Building at Abu Dhabi International Airport, in Abu Dhabi, UAE. Delivered in partnership with Atlas Security, deployment of Ipsotek’s AI video analytics solutions is anticipated to improve operations, security, and safety across various areas of the Midfield Terminal Building, which is renowned for its iconic architecture and recently gained international attention as a filming location for Mission: Impossible - Dead Reckoning Part One. Advanced surveillance capabilities Ipsotek's AI video analytics technology is well-equipped to address these circumstances Safety and security are clearly paramount in any airport environment, and Ipsotek's AI video analytics technology is well-equipped to address these concerns. The advanced surveillance capabilities of the solution enable operators to detect and identify potential threats across various zones of the airport. By leveraging intelligent algorithms and machine learning, the system can recognize suspicious behaviors, unauthorized access attempts, or other pre-defined security risks in real-time, allowing for swift response and mitigation. Ipsotek's AI video analytics By leveraging Ipsotek's cutting-edge video analytics solutions, the airport aims to enhance its security measures by effectively detecting abandoned baggage scenarios. Security teams at the airport will be able to quickly identify and respond to any unattended baggage, reducing potential security risks and ensuring a safe environment for passengers and staff. "The deployment of Ipsotek's AI video analytics solutions at the Midfield Terminal Building signifies a significant leap forward for the aviation industry," said Sophiene Marzouk, Ipsotek’s UAE Country Manager. Sophiene Marzouk adds, "We are proud to collaborate with Atlas Security to deliver state-of-the-art technology that enhances operations, security, and safety in one of the world's most iconic airport buildings." Ipsotek's solutions Ipsotek's solutions also play a crucial role in optimizing que management and crowd control “Atlas Security aspires to implement the best technology for security systems in airports and we therefore look to partner with companies bringing innovation in security applications with Artificial Analytics. One company that brings this cutting-edge technology is Ipsotek and Atlas Security is proud to work in the Midfield Terminal Building with Ipsotek,” said Khizer Rehman, Project and Technical Manager at Atlas Security. Ipsotek's solutions will also play a crucial role in optimizing que management and crowd control throughout the airport. By analyzing video feeds, the software can determine que lengths and alert airport staff to potential bottlenecks. New standards for excellence The intelligent system will empower operators to proactively manage queues, allocate resources effectively, and ensure a smooth flow of passengers. As travelers eagerly anticipate the unveiling of the Midfield Terminal Building, the deployment of Ipsotek's AI video analytics solutions is set to improve the airport experience, from safety to security and operations setting new standards for excellence in the aviation industry and turning an impossible mission into a successful deployment.
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the U.S. Department of Homeland Security SAFETY Act Designation, announced that Eastern Michigan University (EMU) in Washtenaw County, Michigan, will deploy ZeroEyes’ solution across its campus to protect students, staff, and visitors from gun-related violence. EMU selected ZeroEyes following an extensive selection process and is the first higher education institution in Michigan to adopt an AI gun detection solution. Alerts and actionable intelligence ZeroEyes' AI gun detection and intelligent situational awareness software will be layered on EMU’s existing digital security cameras. If a gun is identified, images will instantly be shared with the ZeroEyes Operations Center (ZOC), staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they will dispatch alerts and actionable intelligence, including visual description, gun type, and last known location, to local staff and the campus police force in as fast as 3 to 5 seconds from detection. Safe campus experience ZeroEyes does not conduct any kind of facial recognition, eliminating the risk of bias based on skin color Throughout this process, ZeroEyes does not conduct any kind of facial recognition, eliminating the risk of bias based on skin color or other personal characteristics. "The integration of ZeroEyes will continue Eastern’s commitment to providing a safe campus experience for all who study and work here," said James Smith, President of Eastern Michigan University. James Smith adds, "Ensuring a secure, inclusive, and open campus environment is an ongoing commitment by our Department of Public Safety (DPS) leadership and campus staff.” Multilayered security Located in Ypsilanti, Mich., EMU has an 800-acre campus, with 14,000 students and nearly 2,000 employees. ZeroEyes is the latest addition to an expanded, comprehensive, and multilayered range of security measures the university has implemented to help ensure a safe community. Other solutions include a hi-tech police dispatch center that monitors over 1,000 security cameras 24/7, key locks on classroom doors, newly installed over the summer with additional locks being added throughout the year, an emergency text alert system, and residence hall key card entry for students. Intelligent situational awareness The advance notice offered by ZeroEyes will provide our first responders with the opportunity to intervene proactively" "In the event of gun-related violence, the advance notice offered by ZeroEyes will provide our first responders with the opportunity to intervene proactively and potentially de-escalate the situation,” said Matthew Lige, Executive Director of Public Safety and Chief of Police at Eastern Michigan University. He adds, “It will also provide Department of Public Safety staff the ability to notify the campus community with timely and accurate information to make informed safety decisions.” AI gun detection “Eastern Michigan University’s dedication to the safety and welfare of its community is truly admirable,” said Mike Lahiff, CEO, and Co-Founder of ZeroEyes. He adds, “By choosing to implement ZeroEyes technology, the campus is showcasing its unwavering commitment to establish a safe and trusted learning environment. We are proud to provide the first AI gun detection solution adopted by a higher education institution in Michigan.”


Products


Round table discussion
Physical security is a large market overall, encompassing a range of diverse vertical markets, each with its own set of challenges and opportunities. The success of the security industry overall depends on the ability of companies and technologies to meet the specific needs of each vertical market. Some markets offer more lucrative opportunities than others. We asked this week’s Expert Panel Roundtable: Which vertical markets have the greatest potential for growth for physical security systems?
There is safety in numbers, or so the expression goes. Generally speaking, several employees working together tend to be safer than a single employee working alone. Even so, some environments require that workers complete their jobs alone, thus presenting a unique combination of security vulnerabilities. The U.S. Occupational Safety and Health Administration (OSHA) defines a lone worker as “an employee working alone, such as in a confined space or isolated location.” We asked this week’s Expert Panel Roundtable: How can security technologies help to protect "lone workers?"
In the United States, they are called license plate recognition (LPR) systems. In Europe, the more common term is automated license number-plate recognition (ANPR). In either case, the systems provide capabilities that can benefit a range of applications from schools to municipalities to parking lots. Newer technologies can even identify vehicle color, type, make, and model. We asked this week’s Expert Panel Roundtable: What's new with license plate recognition (LPR) and/or automated number-plate recognition (ANPR) systems?
Videos
IP transmission: Manufacturers & Suppliers
- exacqVision IP transmission
- BCDVideo IP transmission
- Axis Communications IP transmission
- Software House IP transmission
- AMAG IP transmission
- Dahua Technology IP transmission
- Honeywell Security IP transmission
- Video Storage Solutions IP transmission
- OT Systems IP transmission
- Avigilon IP transmission
- Senstar IP transmission
- Hikvision IP transmission
- March Networks IP transmission
- Messoa IP transmission
- Dallmeier IP transmission

Multi-Residential Access Management And Security
Download
Guide For HAAS: New Choice Of SMB Security System
Download
Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
Download
Hikvision: Solar Powered Product Introduction + HCP
Download
Artificial Intelligence
Download