Industrial & commercial security applications
The Honourable Society of Lincoln’s Inn is one of the four Inns of Court and operates as an active and thriving society of lawyers, sprawling across 11 acres in central London and dating as far back as 1422. The title of “Lincoln’s Inn” refers both to the Society and the location, which houses the Society’s facilities, numerous barristers’ chambers, and several solicitors’ offices. Inns of Court The Inns of Court originally provided accommodation for...
Security office in commercial and residential building requires state-of-the-art solutions that can keep up with the demands of modern surveillance and threat detection. With space-efficient design, high-performance processing, coupled with advanced data protection, NVR NViS 5704, a powerful video analytics solution, enable seamless surveillance operations and enhanced security measure in edge AI applications. These capabilities empower security office to efficiently monitor and analyze video...
Makita, one of the world's renowned manufacturers of cordless, electric, and garden tools, has opened a completely new headquarters in Banska Bystrica, Slovakia. At this location, Makita stock and distribute batteries for cordless tools plus run wholesale supply logistics from their warehouse. Single, intuitive system At a facility like this, simplicity and clarity for both security managers and daily site users were essential. They demanded a single, intuitive system to control every ac...
Makita, one of the world's major manufacturers of cordless, electric, and garden tools, has opened a completely new headquarters in Banska Bystrica, Slovakia. At this location, Makita stock and distribute batteries for cordless tools plus run wholesale supply logistics from their warehouse. At a facility like this, simplicity and clarity for both security managers and daily site users were essential. They demanded a single, intuitive system to control every access point for...
In 2020, the forest areas in Dali Prefecture, Yunnan Province were reported to have reached 1.855 million hectares, ranking among the top in the country. In addition to absorbing carbon dioxide, conserving water sources, and maintaining water and soil, these ancient forests also shelter a large number of rare wild animals and plants. These natural wonders are a risk if a forest fire breaks out, causing drastic damage and endangering the inhabitants of the forest. Wireless transmission systems...
A manufacturing facility is a tough testing ground for any access control solution. By their nature, premises usually require multiple types of locks, including a range of cylinder types and sizes, as well as padlocks. They often need locks that work both inside and outdoors. For this reason, many manufacturing plants retain outdated mechanical locking solutions, sacrificing the added control of an electronic solution. Programmable key solution criteria The right programmable key soluti...
News
Sweden-based AP&T supplies production solutions to manufacturers worldwide, including automation, presses, furnace systems, and tooling, for the manufacturing of press-hardened vehicle parts for the automotive industry. Car manufacturers are using lighter sheet materials, such as aluminum and thinner steel, to form robust parts for car body frames. When pressed, these lighter materials still produce a strong body frame meeting required safety standards without adding unnecessary weight to a car’s build which can drain both fuel and battery life. Measure and monitor sheet materials AP&T needed a solution to measure and monitor sheet materials before and after pressing. It is necessary to guarantee even heat distribution from the furnace before the sheets are pressed, the exact placement of the sheets, and to ensure that there are no hot spots after the sheets were cooled in the press tool. If any of these three conditions is not met, the required mechanical properties of the safety-relevant components will not be reached. This causes rejected parts, wasted materials, and additional manufacturing time. Also, the press tool itself might be damaged. The IPHA System - Thermal imaging for non-contact temperature monitoring To save car manufacturers time and money by preventing defect-pressed parts, AP&T reached out to Swedish thermal imaging integrator Termisk. Termisk designed an Infrared Press Hardening Analysis (IPHA) vision system that can measure the three main factors affecting sheet pressing quality: temperature before and after pressing, and sheet placement in the press. Using Teledyne FLIR thermal imaging cameras mounted to the sides of press machines, the IPHA system measures the temperature of metal sheets using the Teledyne FLIR A70 smart sensor camera (previously A315) or Teledyne FLIR A615 camera depending on the required image quality. Accurately measuring heat distribution on shaped metal sheets The IPHA system features a Teledyne FLIR thermal imaging camera on each side of the press with wide-angle lenses. The setup ensures the temperature is measured accurately for the whole surface area of the 3D-shaped sheet material. The process is automated, so once pieces are inside the press, the press-line controller system signals to IPHA to take an image and analyze it. Once the positioning and temperature are determined as ok, a signal is sent back to the press line to proceed. High-resolution thermal images Similarly, it then measures the sheet temperature and inspects heat distribution after pressing, after the shaped part is cooled. Unless there are any issues or alarms raised, there is minimal interference needed from an operator. The high-resolution thermal images make it quick and easy to identify hot spots and measure the areas where the material has not reached the correct temperatures. The system makes tool pressing and changeovers quick and simple too. The software allows manufacturers to pre-set temperature analysis parameters for the different pressing tools used. This allows the IPHA system to re-configure quickly during changeovers. Accurate and flexible thermal imaging solutions Teledyne FLIR’s A70 image streaming camera is ideal for advanced condition monitoring. In this case, the Teledyne FLIR A70 is capable of monitoring the temperature and heat distribution on steel sheets, even with raised parts, using non-contact temperature sensors. The wide-area monitoring capabilities of the A70 cameras mean that two cameras: one on each side of the press is enough to monitor the large steel sheets. The cameras will alert operators to any issues so they can investigate and rectify them immediately to prevent wasted materials and additional production time. Teledyne FLIR A615 camera For sites that require higher thermal imaging quality, the Teledyne FLIR A615 camera is a powerful alternative to the A70 in IPHA. Offering the same non-contact temperature measurement, the A615 provides higher accuracy and can detect temperature differences even at long distances. Termisk has implemented at least 40 IPHA systems for pressed part manufacturer AP&T worldwide. The thermal imaging solution can be installed on new lines or retrofitted to existing lines.
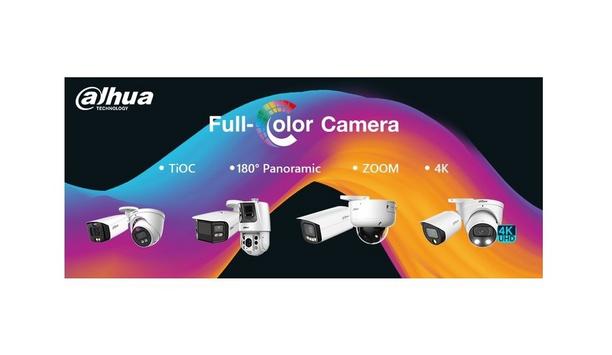
Over the years, Dahua has continuously invested in the development and innovation of Full-color technology to solve the monitoring challenges brought by low illumination. In 2018, the company launched the Starlight and Starlight+ technologies which enable cameras to effectively capture color details in low-light environments. 24/7 color monitoring Focusing on further improving low-light monitoring, Dahua officially released the Full-color concept in 2020, realizing 24/7 color monitoring by introducing F1.0 super aperture, 1/1.8 '' high-performance sensor for large targets, and Dahua’s self-developed ISP 4.0 technology. The color information of key targets in the scene can be captured even at night, which can be used as evidence in case of an investigation or backtracking. Dahua Full color 2.0 technology Dahua TechMonth showcases some of the integrations of Full-color technology for customers and end users In 2021, the company continued to upgrade its technology and launched the Dahua Full color 2.0 technology. It further expanded the Full-color “family” and integrated 4K, panoramic, zoom, and other technologies to facilitate the development of high-end products, provide a more comprehensive product system, and enhance low-light surveillance. To elaborate more about this remarkable technology, Dahua TechMonth showcases some of the integrations of Full-color technology that create more business value for customers and end users. Recap of solutions Following is a short recap of these amazing solutions: Full-color + TiOC The TiOC (three-in-one camera) has 3 main features: Smart Dual Illuminators, Active Deterrence, and AI. It can effectively warn off intruders with active deterrence, and notify users in time with real-time alarm, providing pro-active video surveillance to properties that require 24/7 security. TiOC utilizes Full-color technology to capture color footage in dark scenarios. Also, its smart exposure technology realises time-sharing control and prevents the interference of flashing red & blue light in the image. To see TiOC in action, check out this video. Full-color + Panoramic The Dahua Full-color Dual Lens 180° Panoramic PTZ & IPC devices are equipped with dual sensors that deliver a 180-degree field of view. After the right and left lenses to capture an image, the camera calculates the feature values of the left and right images to avoid warping and pixel loss using standardized image correction technology. The Dahua advanced pixel-level metadata fusion algorithm then enables seamless splicing of the image, resulting in a seamless 180° wide-angle image. Panoramic IPC The Panoramic IPC offers EPTZ that provides a panoramic image of the scene, as well as sub-images that focus on specific areas or targets. For the panoramic PTZ camera, both panoramic and detailed views support AI functions and can be independently deployed in different directions to cover wider areas. Full-color + ZOOM The motorized varifocal lens of the upgraded Dahua Full-color 2.0 network cameras has approx. 5x optical zoom capability and auto-focus function, providing clear color details of the monitored scene even after zooming in. With its long-distance illumination capability, the camera can also capture a clear full-color image even from far distances. Full-color + 4K The Dahua Full-color 4K camera delivers enhanced color images and surveillance footage 24/7. It adopts a 1/1.2” image sensor (currently Dahua's best low-light IPC sensor) that provides a 110% pixel size increase compared to a common 8MP sensor. Its F1.0 large aperture can capture more available light and the maximum light energy that the sensor can receive is increased by 2 times. Success Case: Schwarze Berge Wildlife Park Located in Rosengarten Germany, the Schwarze Berge (Black Mountains) Wildlife Park covers an area of about 50 hectares. It is home to nearly a thousand of animals from approximately 100 species grazing in Europe. The administration of the park was looking for a comprehensive camera system that can perform many tasks. “We chose Dahua because it customized a complete solution to meet all our needs,” says Arne Vaubel, Managing Director of the Schwarze Berge (Black Mountains) Wildlife Park. Full-color and thermal imaging In this project, a full series of innovative cameras equipped with key technologies" “In this project, a full series of innovative cameras equipped with key technologies, such as Full-color and thermal imaging are adopted." "We are glad to see that through our cameras, the park can monitor the living environment and health status of wild animals at any moment without disturbing them, which also helps the park realize efficient operation and management,” explains Kai Wockenfuß, Pre-Sales Support Technical Engineer of Dahua Technology GmbH. Fixed-focal Warm LED Bullet WizMind Network Camera One notable Dahua camera deployed in the park is the 8MP Full-color Fixed-focal Warm LED Bullet WizMind Network Camera. It is equipped with a high-performance sensor and large aperture lens, enabling it to capture clear color images when it’s dark or during the night. With its photosensitivity technology, the camera can capture more available light and display more colorful footage of the monitored scene, providing 24/7 monitoring of the wildlife in the park. The future of Dahua Full-color technology With the success of Dahua Full-color in the market, what does the future holds for this amazing technology? For starters, minimizing white light pollution is at the top of the list. Some cameras with full-color capabilities in the market still use white light, which can affect the human eye and cause severe light pollution in the monitored scene. Touchless Full-color cameras are one solution that Dahua has been exploring through its multi-spectrum algorithm. The Dahua Multi Spectrum Fusion technology extracts the details and brightness of the visible spectrum and infrared spectrum to make the fusion brightness close to the visible light brightness, which then enables the camera to provide better images. AI integration Another aspect that Dahua is focusing on is the deeper integration of Full-color with AI Another aspect that Dahua is focusing on is the deeper integration of Full-color with AI. Full-color technology is continuously being upgraded, and with that comes more intelligent solutions that can realize clear HD images at night, like it is during day time. The TiOC, for example, combines Full-color, AI, and Active Deterrence (warning lights and siren) into one comprehensive solution, realizing a closed-loop system that involves early warning, active deterrence, and backtracking. It has been recognized by many authoritative organizations in the industry and even received distinctive awards. Intelligent analysis and computing What’s more, the constant development of this technology can enable Full-color imaging to be directly applied to intelligent analysis and computing. It will become a mainstream technology that everyone can avail and use to optimize their scenarios, which is in line with Dahua’s mission of “Enabling a safer society, and smarter living.”
More than one million electric vehicles are registered in the U.S.—and they all have to plug in somewhere. As EV charging stations pop up across the country, one of the chief questions will be how charging station users are identified, authenticated, and connected with membership or payment systems. Radio-frequency identification cards and tokens and smartphone authentication apps have emerged as two viable options for EV charging authentication. Which is best? It may depend on the user base they plan to serve. User authentication for EV charging Most electric vehicle owners have a spot to plug in while at home, either in their own garage or carport or in a designated charging spot in a tenant parking garage. But electric vehicles also need spots to charge while owners are out and about. The EV charging market is broadly divided into two tiers: Level 2 charging stations, which operate at 208-240 V and use AC power. These stations will add 20-25 miles of range in about an hour of charging. The U.S. Department of Transportation listed more than 22,800 public Level 2 EV charging stations across the nation as of mid-2020. They are commonly found in public parking lots and garages, hotels, grocery stores, malls, and other commercial areas. They may also be installed in private parking garages and business parking lots for use by tenants, employees or fleet drivers. Collecting membership data Direct Current Fast Chargers (DCFS) are designed to charge an EV battery to about 80% in 20-30 minutes. There are currently about 15,000 DCFC stations across the U.S., but their numbers are expected to explode as more people start taking EVs on longer road trips. They are commonly found along major interstate highways. As the market evolves, user authentication requirements for EV charging stations are likely to vary by type, location, and user base. Some commercial locations may provide Level 2 EV charging as a free amenity to shoppers, guests or employees. If there is no charge for the service, there may be no need to authenticate users at all— people can simply park and plug at any available spot. However, there may be a benefit to collecting membership data (e.g., shopper reward club). Private charging stations Public, for-profit EV charging stations, like gas stations, need a method to collect payment for their services. In some cases (especially at roadside DCFS stations), users may simply pay for the minutes used with a credit card—just like at the gas station pump. However, many EV charging station users are already accustomed to identifying themselves with an RFID membership card or a smartphone app. Charging networks like ChargePoint and Blink enable members to access any EV charging station within their networks with a card or smartphone app, which connects to their membership, account, and payment information. Private charging stations—such as those offered to tenants, employees or fleet drivers—may not require payment but need to ensure that only authorized drivers are accessing power and taking up valuable parking spots. An RFID card or smartphone app can be used to identify authorized drivers and track charging behaviors. Moving forward, many EV charging stations may find that they need a mix of options for users, including membership cards, smartphone apps, and a credit card payment option for out-of-network drivers. Choosing between RFID and smartphone apps In the long run, the answer may be ‘both.’ RFID cards are economical and easy to issue When user identification and authentication are desirable, which is the better option: RFID cards or smartphone authentication? Both have their uses in the EV charging market. In the long run, the answer may be ‘both.’ RFID cards are economical and easy to issue. And for some users bases, they may not have to issue a new card at all—they can take advantage of an RFID card they already carry. In many cases, it is possible to leverage existing employee IDs and membership cards for access to privately controlled EV charging stations. RFID membership cards may be a good bet for: Fleet drivers who already carry an RFID card for vehicle access. Employee parking lots and garages where people already use a card for entry. EV charging parking spots at gyms or other locations where users want to limit charging access to active members. EV charging stations Most consumers would prefer not to have to carry a physical membership card for every retail outlet On the other hand, public charging stations may find that consumers would prefer to use a smartphone app rather than receive another membership card to carry in a physical wallet. Many consumers prefer to carry only their phone and one or two essential cards (such as a driver’s license and a single credit or debit card). As more retailers enable consumers to pay via a digital wallet app on their smartphones, some don’t even carry a physical credit card anymore. Most consumers would prefer not to have to carry a physical membership card for every retail outlet they visit—and that includes EV charging stations. Smartphone apps for user authentication are simple to set up and highly secure. Instead of RFID, they typically use either Bluetooth® Low Energy (BLE) or Near-field Communication (NFC) protocols. Public charging stations For the user, the experience is almost identical to RFID authentication, except they wave a smartphone over the reader instead of a card. Apps have other user benefits, too. A custom app for EV charging can be configured to help users locate or reserve charging stations, check their balance and usage history, and change their payment options right on their phone. These features make smartphone authentication ideal for consumers These features make smartphone authentication ideal for consumers accessing a network of public charging stations. However, EV charging network managers should keep in mind that some users may still want a physical membership card. Smartphone-Based authentication There are still some user populations, such as older consumers and those from lower income brackets, where smartphone ownership is not ubiquitous. If users are primarily using EV charging for a fleet vehicle, they may not want to download an application for work on their personal cell phone. Other users may find smartphone apps confusing or simply prefer to have a card for other reasons. The answer for both public EV charging networks and private charging station owners is to have an RFID reader that is capable of both card-based and smartphone-based authentication. This will provide maximum flexibility as user preferences change. Finding the right RFID reader for EV charging The ELATEC TWN4 MultiTech family of readers is ideal for authentication at EV charging stations The best RFID reader for EV charging is one that is flexible enough to meet the needs of all user populations and evolve as requirements change. The ELATEC TWN4 MultiTech family of readers is ideal for authentication at EV charging stations. The readers support 60+ RFID transponder technologies along with BLE and NFC smartphone authentication. This means that one reader can support all common technologies already in use across the entire user base—both nationally and internationally. This capability becomes important for applications where users want to enable drivers to use an existing RFID card (such as their employee or fleet ID card or an access card for a tenant parking garage) for access to charging locations. It also provides more flexibility as technologies or preferences change in the future. Supporting advanced encryption TWN4 MultiTech supports advanced encryption and security configurations for highly secure transactions between the card or smartphone and the reader. This is important for EV charging applications tied to payment or employee/driver identification. ELATEC readers are mobile-ready. The ELATEC Mobile Badge BLE NFC App offers simple and effective components for building or extending a mobile application for EV charging networks. Non-managed mobile credentialing using the ELATEC app is free. TWN4 MultiTech readers also work with multiple existing third-party managed credential systems, such as KleverKey, Safetrust, and Transact. The TWN4 MultiTech is easy to customize with the powerful Software Development Kit (DevPack) and App Blaster and Director utilities. Readers can be easily configured to support custom functionality (such as LED light flashing sequences or sounds for user feedback) and integration with backend software for easier member management. The DevPack tools make the TWN4 family the most powerful, versatile, and sustainable readers on the market. Hardware communication interfaces As electric vehicles move from niche to mainstream, EV charging infrastructure will need to grow and evolve to accommodate millions more drivers—both in the consumer market and in commercial fleets. With TWN4 MultiTech, EV charging station managers will be ready. Interested in learning more about technical considerations for RFID? Download 11 Considerations for Embedded System RFID Readers for additional advice, including operating power and consumption requirements, antenna placement, hardware communication interfaces, and more.
Integrated security manufacturer, TDSi has unveiled its enhanced, free-of-charge training offering, which includes an updated training facility, enhanced online booking system and a refreshed training syllabus, which focuses on its GARDiS ecosystem range. Jon Hooley, the Technical Support Manager at TDSi, commented “Over the last couple of years, much of our training has had to be conducted remotely online, but with the relaxation of social distancing rules earlier this year, we have had the perfect opportunity to further evolve and enhance our face-to-face training facilities.” Fully refurbished training facilities He adds, “Our fully refurbished and updated training facilities in Poole reflect the latest technology developments, with a firm focus on GARDiS as our flagship range of fully integrated web-enabled systems, their installation and integration with other systems.” With installers and end users upgrading from TDSi’s classic EXgarde security software solution to GARDiS, TDSi is catering for increased demand for further practical training on the flagship range. Along with TDSi’s headquarters in Poole, Dorset, United Kingdom (UK), it also offers training at its partner - Texecom’s state-of-the-art facility, located in Haslingden, Lancashire, in order to provide further choice on where to train geographically in the United Kingdom. With sessions taking place at both locations each month, TDSi’s training is highly flexible to the needs of those taking part. Revamped and fully wireless training room The sessions usually cater for six people to ensure an excellent one-to-one training experience" The revamped and fully wireless training room in Poole has been designed to provide the ideal training environment for TDSi’s Gold and Platinum-accredited partners, as Jon Hooley stated, “The majority of participants are security installers looking to enhance their knowledge and expertise in using TDSi’s integrated security systems.” Jon Hooley adds, “The sessions usually cater for six people to ensure an excellent one-to-one training experience. We do also offer bespoke paid-for options that are particularly well suited to larger groups, bespoke content requirements for end-users for example, along with an additional option of on-premises training if required.” New enhanced online booking system The new enhanced online booking system also makes the process quicker and easier, as Nick Mercer, the Marketing Manager at TDSi, commented “Bookings for the Approved Installer Training Course are now placed through the website and the whole booking process can be done in minutes.” Nick Mercer adds, “Installers registering their place will receive immediate confirmation, along with a digital ticket via email and bookings are easily managed for amends or cancellations. The platform also enables us to expand the training we offer, to include additional remote sessions, such as webinars and online training, in the future.” Well-equipped and dedicated training facility Reflecting upon TDSi’s enhanced training, Jon Hooley concludes, “While online training is invaluable, it can’t completely replace the hands-on experience and benefits of a well-equipped and dedicated training facility, and we are very excited to be welcoming our partners to the new training room.”
The Security Industry Association (SIA) announced a major milestone in its SIA OSDP Verified initiative that over 100 device models have been named OSDP Verified through the comprehensive program, which validates device conformance to the SIA Open Supervised Device Protocol (OSDP) standard. SIA OSDP standard SIA OSDP standard is an access control communications protocol standard maintained by SIA to improve interoperability, add advanced functionalities, and support AES-128 encryption for security. Already in use by many leading manufacturers, the standard offers compliance with access control installations that require advanced security or are used in government per FIPS 201-3. SIA OSDP Verified list Buyers have the confidence that the products from the SIA OSDP Verified list have been third-party tested and performed Products that are OSDP Verified are displayed in the OSDP Verified Product List and can use the SIA OSDP Verified mark in their product marketing materials. With this milestone, security integrators, specifiers, and practitioners have a wider array of OSDP offerings to recommend, and buyers have the confidence products from the SIA OSDP Verified list have been third-party tested and performed within the requirements of the OSDP standard. Program expansion “Since its launch in April 2020, the SIA OSDP Verified program has tested and validated 115 products from 18 brands substantial progress in just a little over two years, highlighting the market need and success of the program,” said Edison Shen, director of standards and technology at SIA. “The program has also welcomed three international manufacturers, and we’re seeing growing interest in both domestic and international participation.” Authoritative source The establishment of the SIA OSDP Verified program was a response to the growing adoption of OSDP in the industry The establishment of the SIA OSDP Verified program was a response to the growing adoption of OSDP in the industry to provide an authoritative source of OSDP solutions and the market confusion for non-verified claims of product compliance with the OSDP standard. By becoming OSDP Verified and displaying the SIA OSDP Verified mark on their products, access control manufacturers can instill confidence in their customers that their devices have gone through rigorous testing as required by the OSDP standard. Benefits of SIA OSDP Verified Benefits of becoming SIA OSDP Verified include: An authoritative listing of OSDP solutions A consultative process that provides vendors with implementation and remediation guidance A lightweight, non-punitive program with no annual membership fees Continuous access to open-source testing tools and community feedback that promotes device conformance through the product life cycle
The National Cyber Security Centre (NCSC) and SANS Institute have announced details of the third edition of CyberThreat - a technical and interactive Summit that will be hosted virtually and in person. The event, designed for technical professionals across the cybersecurity industry, will return on September 12th and 13th at the Park Plaza, Westminster Bridge in London, encouraging global knowledge sharing and expertise across defensive and offensive disciplines. CyberThreat Summit CyberThreat will feature keynote speeches on the latest online dangers to organizations and insights from industry spokespeople and cyber practitioners about how to defend against sophisticated cyber attacks. The event will include interactive elements for in-person attendees, such as large-scale Capture the Flags (CTF) and “hackathons” that run over the two days. Hands-on activities There will be a blend of technical talks and hands-on activities, covering both offensive and defensive techniques" As part of the event itinerary, there will be a blend of technical talks and hands-on activities, covering both offensive and defensive techniques, as well as opportunities to network with a wide range of peers. Joining information for registrants can be found on the SANS Institute page. Through a partnership with NCSC, 75 delegate places are available to public sector employees free of charge. New opportunities Paul Chichester, Director of Operations, NCSC said, “CyberThreat is a vital event for our technology community bringing together a broad range of practitioners to develop, challenge, and inspire each other, all with a laser focus on the threats we face and the techniques we can employ to counter them." “While society has pulled together recently, our increased reliance on technology has presented new opportunities to those with malicious intent and added to the challenges we face. I am delighted that we are once again in a position for the NCSC to play its role in this event.” Share and gain new cybersecurity skills The event is designed to address the cyber skills gap and enhance cyber talent by developing new talent" James Lyne, CTO, SANS said, “Cyber Threat provides a unique opportunity for practitioners from both government and the commercial world to share cybersecurity experiences and to acquire new technical skills and knowledge.” “The event is designed to address the cyber skills gap and enhance cyber talent by developing and enthusing both new and existing talent." Combating the threat James continues, “While the last two years have brought significant disruption to the world, technology and technologists have been instrumental in enabling the international response to the pandemic, and reducing the impact on our economies, our businesses, our educators, and our families.” “The threat landscape has continued to grow and evolve, but by sharing cutting edge techniques and new solutions to ongoing problems, we can learn to combat those threats together as a community.”


Expert commentary
Changing customer needs can make specifying an alarm system that will continue to deliver in the long term a challenge. However, the latest modular alarm solutions provide the opportunity to build a more individualized system from the outset, as well as offering the ability to up-scale in the future without causing disruption. Martin Wilson, North EMEA Regional Director at Resideo, looks at how alarm specialists can use this style of solution to both benefit customers and build their own business opportunities. Holistic sense of home security An alarm system no longer needs to function on one level, alerting only to a break-in taking place In a survey of 1,000 homeowners undertaken by Resideo, the results revealed that, although deterring burglary was still a top priority, consumers were moving to a more holistic sense of home security, wanting to bring convenience, and property and life safety, into the mix. Indeed, an alarm system no longer needs to function on one level, alerting only to a break-in taking place. The latest modular alarm systems offer the flexibility to create a scalable security and life safety platform for homes and small businesses, as well as giving installers the ability to suggest future update options that can be added as and when budget or requirement allows. Valuable up-scales Finding an alarm that can be scaled over time has the obvious business benefit of ensuring it is easy to revisit and add to as customers naturally expand their existing security. With many modular designs connected via WiFi, this not only means installers can opt for the right mix of sensor options from the get-go but also that any additions can be connected to the panel and system with ease. Many control hubs have winning features in their own right. The ProSeries security panel by Resideo, for instance, has an intuitive touchscreen, easy-to-read, full-color display to reduce false alarms, plus a built-in camera, speaker and microphone, intuitive icons, and even five-day weather alerts. The ProSeries security panel by Resideo has an intuitive touchscreen Natural up-scale opportunities For instance, for those in a property prone to flooding, a flood sensor may be a worthwhile addition For the installer, it has a plug-in power connection, trouble-shooting videos, and end-user-replaceable batteries to reduce unnecessary callouts. However, to build a scalable system, this needs to be coupled with the right, flexible solutions to tackle customer concerns. Taking the time to find out what is important to the end user is vital here and can lead to natural up-scale opportunities. For instance, for those in a property prone to flooding, a flood sensor may be a worthwhile addition. Similarly, a panic button and even medical transmitters may be of benefit to others. All this, as well as other options, such as glass break detectors, door and window sensors, and indoor and outdoor MotionViewers™, are available within the ProSeries range, and can be updated or added to an installation as needed or as a property grows with minimum disruption. Adding life safety The ability to propose an alarm system that can bring together alerts for different threats – for both the home and life – under one platform, also has real appeal. Indeed, in a survey of 1,000 homeowners undertaken on behalf of Resideo, a system’s ability to alert to the dangers presented by fire and CO was mentioned as an important part of the decision-making process by 41% of participants. For many, this increased awareness may stem from the many regulation updates regarding smoke and carbon monoxide (CO) alarms that took place in 2022. In Scotland, for instance, carbon monoxide detectors were required to be fitted in any room with a carbon-fueled appliance in all homes, rented or owned. Social housing properties In England, smoke and carbon monoxide alarms were required in all social housing properties In England, from the 1st of October 2002, smoke and carbon monoxide alarms were required in all social housing properties, with carbon monoxide alarms now mandatory in the private rented sector. Wales followed suit in December for rented accommodation. The new guidance for England and Wales requires at least one smoke alarm to be installed on each storey of a property, to help alert to domestic fires more quickly, ensuring a quicker evacuation and reduced risk of fatality. For professionals, systems such as ProSeries, can be connected to a series of smoke and carbon monoxide detectors, in a ‘one-go-all-go’ setup that means the alarm will go off if one of these threats are identified. Smart and connected benefits The total Connect 2.0 app gives ProSeries end-users the ability to view and control the security platform remotely. The Resideo Pro app currently gives installers the ability to view the system and connect to the central monitoring system. The platform also supports home automation as it works with Zwave devices. The platform also supports home automation as it works with Z-wave devices. The platform also supports home automation as it works with Z-wave devices There are also extra benefits for alarm professionals too. The AlarmNet 360™platform on which ProSeries is configured gives greater insight to improve business operations, increase efficiency and deliver insights on accounts to identify additional upsell opportunities and ongoing services. Providing the ability to remotely diagnose brings valuable time-saving options and avoids unnecessary callouts. It also means the ProSeries panel and peripherals programming can be accessed anytime, anywhere, using the cloud, allowing ease of programming, troubleshooting and account management on the go. Needs and future possibilities Changing a complete alarm system to apply new functions is never going to feature highly with the end user, nor does it work where longevity and sustainability is concerned. Having the ability to build a modular system and add to this as needed, whether this is at a property or a small business, provides benefits for both customers and professionals when it comes to meeting immediate needs and future possibilities. Add connectivity and remote access to this and you have a platform that can help streamline business operations, putting professionals more in touch with customers, and helping to spot future opportunities.
The adoption of innovative and interconnected door hardware systems can help overcome the challenges associated with building security, explains Daniel May of Consort Architectural Hardware. The security of our built environment and the safety of its people is paramount throughout a building’s lifecycle. While these elements remain a primary focus at each touchpoint of a construction project, today’s design teams are sooner adopting modern access control systems to address this age-old challenge, but why? Modern access control Where systems were once rudimentary, modern access control has evolved into a revolutionary factor of building design, unlocking various benefits for its many users in the process. The Internet of Things (IoT) has enhanced building security as we know it, and as technology continues to advance, more options enter the market. Following more than a decade of innovation and integration, the access control market is projected to grow year on year, from £7.8 billion in 2023 to £11.8 billion by 2028. Modern user requirements have led to several operational and technological advancements Modern user requirements have led to several operational and technological advancements during this period, and decision makers and design teams alike can now choose from a versatile selection of options. Some door hardware products now utilize smart locks, cloud control and even biometrics for example, and most recently, there’s been a substantial change to the way access control systems operate, with focus moving towards end users and ease of use. Modern access control has evolved into a revolutionary factor of building design Smart door hardware From an operational perspective, interconnected access control systems gift users with an intuitive network that improves building security through the use of real-time status updates, while also providing them with the ability to grant instant access approval and denial at the touch of a button. Often, users can operate their building’s various access points through their mobile phone, which has led to improved flexibility and efficiency in most environments - whether at home or in a public access property. The security benefits also become clear when compared to the alternative of physical keys. If a traditional key is lost or stolen, the security of a building becomes at risk until it is found or replaced. Intuitive access control systems are designed to build upon the traditional lock and key methods. By seamlessly integrating smart door hardware into both new and retrofit projects, users can manage access points and improve security across the building - without stifling ease of access, stunting future scalability or unsettling the aesthetics. Users can operate their building’s various access points through their mobile phone Access control system The PSIA standard is one of the widely recognized and respected standards for access control products As many adopt Wi-Fi infrastructures, NFC technology and cloud services into their buildings, decision makers must also consider the need for better standards. While the introduction of IoT may advance security, performance and functionality, it can also introduce new risks which must be mitigated by adhering to both localised and international standards, such as ISO 27001 for example. The Physical Security Interoperability Alliance (PSIA) standard is one of the widely recognized and respected standards for access control products and provides comprehensive requirements for systems by focusing on interoperability, scalability, and functionality. While the introduction of IoT may advance security, it can also introduce new risks Providing comprehensive requirements This standard ensures that access control products from different manufacturers can seamlessly integrate and communicate with each other, allowing for greater flexibility and choice when designing a complete access control system. After all, a one size fits all access control solution simply doesn’t exist and decision makers would be remiss in not selecting a product that aligns with their building’s needs while meeting the required standards.
In the early stages of childhood education, kindergarten imparts foundational principles that shape future behavior. Today, you can think about cloud computing in a similar manner: it has become a fundamental element in the architecture of modern technology. The cloud now plays a critical role in digital interaction, security, and infrastructure development. Far from being just another tool, the cloud is a cornerstone, providing essential support for the intricate network that supports today's digital ecosystem. Vomplex digital systems Much as kindergarten lessons lay the groundwork for cognitive development, the cloud offers base capabilities that are vital for constructing and operating complex digital systems. Recent advancements in cloud-based security — particularly in access control and video surveillance — emphasize the importance of cloud computing. It has been instrumental in unifying fragmented security systems, similar to how basic social principles taught in kindergarten help diverse children come together as a unit. The role of cloud computing in our technological world is multifaceted and continuously growing The role of cloud computing in our technological world is multifaceted and continuously growing. It has evolved into a space where innovation is cultivated and security commitments are maintained with vigilance. The fusion of artificial intelligence and analytics into cloud services signifies a concerted effort toward a future that is more cohesive, intelligent, and secure. Significant technological progress As we delve deeper into this topic, it will become evident that cloud computing, like the pivotal lessons of kindergarten, is indispensable. It quietly enables significant technological progress, mirroring the foundational principles taught in our formative years in both its essential nature and its growing influence. Play Fair: Technological Developments in Cloud-Based Security The past year has been a period of significant innovation in cloud-based access control and video surveillance. Cloud computing has evolved into a robust platform that fosters the creation of integrated security systems. These systems consolidate access control and video surveillance into a unified experience, demonstrating the cloud's potential to seamlessly combine disparate systems. Substantial industry progression The advent of edge computing has boosted bandwidth efficiency and accelerated data processing The incorporation of artificial intelligence and analytics into cloud services marks a substantial industry progression. This development provides businesses with advanced tools for in-depth analysis and intelligent decision-making, enabling them to not only gather comprehensive insights but also strengthen their security measures. The cloud has eased the transition to new technologies and emphasized a commitment to cybersecurity, with encryption protecting data integrity in transit and at rest. Simultaneously, the advent of edge computing has boosted bandwidth efficiency and accelerated data processing, highlighting a consistent drive to refine and adapt. The trend of integrating cloud security systems with other business platforms help create unified ecosystems, reflecting a broader narrative of security professionals’ pursuit of progress and enhancement. Potential future disruptions Wash Your Hands: Pandemic-Induced Transformation in Cloud Services As we all know, the COVID-19 pandemic necessitated a swift transition to remote operations, with cloud computing forming the backbone. i The urgent need for cloud solutions was apparent as businesses adopted remote collaboration tools, work-from-home policies, and virtual workspaces. This transition increased the demand for cloud services and prompted more adaptable and cost-effective pricing models. Recognizing the critical role of cloud services, organizations enhanced their investment to safeguard operations against potential future disruptions. The pandemic fundamentally altered the perception and valuation of cloud computing, emphasizing its critical role in sustaining business operations. Scaleable digital infrastructures The growing demand for SaaS has led integrators to create scaleable digital infrastructures Share Everything: Systems Integrators and the Adoption of Cloud Systems integrators have done much to realize the cloud’s potential. The growing demand for Software as a Service (SaaS) has led integrators to create scaleable digital infrastructures tailored to specific business needs.. The use of the cloud for data backup has improved efficiency and increased organizations’ ability to cope with disruptions. Although there has been a gradual shift among integrators toward cloud solutions, effectively marketing and supporting SaaS business models remains a challenge. But the possibility of continuous revenue streams through managed services is promoting broader adoption of cloud technologies. Cloud-based security solutions Live, Learn, Think: Enterprise-Level Cloud Adoption There is an increasing trend among large enterprises to adopt cloud-based security solutions. The shift toward VSaaS indicates a move towards subscription models that offer financial and scalability advantages. This transition is more than a mere operational change. Rather, it represents a commitment to the expansive potential for growth and innovation that the cloud offers. But let’s face it: the ‘cloud’ journey is accompanied by challenges, particularly concerning data security. Providers must deliver robust data protection measures to ensure the success of cloud-based security services, which depends not just on technological progress but also on fostering trust with clients. Addressing cybersecurity concerns The hybrid model offers a balanced solution for businesses looking to merge these two environments Baby Steps: Hybrid Cloud and On-Premises Infrastructure The hybrid model, which combines cloud with on-premises infrastructure, continues to be a strategic choice for many organizations. While the cloud provides flexibility and ease of access, on-premises solutions offer control over data security and comply with regulatory demands. The hybrid model offers a balanced solution for businesses looking to merge these two environments. Be Trustworthy: Cybersecurity Measures and Communication Transparent communication is key in addressing cybersecurity concerns with customers and partners. Companies that are transparent about their security protocols, including encryption and regular updates, build trust. Certifications such as SOC 2 Type II affirm a dedication to security, and proactive educational resources ensure that users are well-informed about best practices. Decision-making processes Cloud computing has become the cornerstone of modern security strategies Look: The Future Outlook for Cloud-Based Security Solutions Looking forward 5-10 years, cloud-based security solutions are expected to become even more central to organizational decision-making processes. The cloud is poised to become the hub for predictive decision-making, using AI algorithms and extensive data to proactively manage security risks. This vision of an intelligent, integrated approach to security, with the cloud enabling swift, collaborative responses to threats, is almost at hand. Cloud computing has become the cornerstone of modern security strategies, moving beyond its initial role as a digital transformation tool. As we look to the future, the cloud is set to redefine security paradigms and anchor a new era of intelligent, predictive security operations.
Security beat
Security professionals are recognizing the intelligence value of leveraging publicly and commercially available information. This information can now be accessed more effectively from typically hard-to-reach regions. Also, the technological capabilities have matured in our age of artificial intelligence, machine learning, and data science. Intelligence has historically been based on classified data. However, today’s unclassified data, including open-source intelligence (OSINT), is increasingly being used to provide context and queuing for other types of intelligence. Advanced identity intelligence Babel Street is a technology company providing advanced identity intelligence and risk operations using an AI-enabled data-to-knowledge platform to unlock insights from a flood of data. The company provides advanced data analytics and intelligence for the world’s most trusted government and commercial organizations. Experts have predicted that by 2025 over 463 exabytes of data will be generated each day globally The sheer volume of data is growing exponentially. Experts have predicted that by 2025 over 463 exabytes of data will be generated each day globally. Not only are we seeing exponential growth in the volume of data, but there is also disparity in the veracity and the variety of data. This is being compounded by the ‘app economy’ in which data is created in a new format for every app added around the globe. Human language technology “The problem is that the data ‘junk’ and the ‘crown jewels’ are in the same bucket, and government and commercial entities need better and faster ways to extract intelligence from these torrents of data,” says Farid Moussa, VP, Strategy & Public Sector, Babel Street. Prior to joining Babel Street, Farid retired from the National Security Agency (NSA). He has guided video, image, speech, and text analytics (VISTA) and developed an appreciation for human language technology. An elusive source of data is the Dark Web, where every user, by design, is attempting to obfuscate their identity, and bad actors are hiding much better. “This presents a cat and mouse game – the cat must be smarter than the mouse, but the mouse is continually getting smarter,” says Moussa. Intelligence tools for data analysis SIGINT and HUMINT – while both vital – are also the most expensive forms of intelligence There are several intelligence tools for analyzing data. One of them is signals intelligence (SIGINT), which refers to electronic transmissions collected by ships, planes, ground sites, or satellites. Another is human intelligence (HUMINT), which is collected in a human-to-human fashion. Open-source intelligence (OSINT) is obtained by searching on topics or entities of interest that are publicly available on the Internet at large. Today, these various categories are often done in ‘silos of excellence.’ However, the best practice is using all forms together in a holistic fashion. SIGINT and HUMINT – while both vital – are also the most expensive forms of intelligence, while OSINT, which is growing in importance, is most cost-effective. All are vital forms of intelligence; OSINT is complementary and crucial to holistic intelligence practices. Holistic intelligence practices When it comes to physical security of people and places, OSINT has become a critical source of actionable information. Security directors leverage Publicly Available Information (PAI) to safeguard against threats to individuals, property, travel routes, and event sites. By monitoring PAI, security teams can detect and respond to potential dangers, including during and after events where thorough preparation is vital. Online information can contain warning signs of impending threats. It informs security professionals in uncovering digital traces, confirming intentions, and addressing risks across language barriers, ensuring proactive risk management for the protection of people and property. Role of Natural Language Processing (NLP) The Internet and social media were mostly English language by default, but that has changed exponentially Natural Language Processing (NLP) is a crucial capability that has evolved to recognize the richness and variety of words and names in multiple languages and scripts, and their use across cultures. Using machine learning and linguistics algorithms, the technology simultaneously considers numerous types of name variations. At one time, the Internet and social media were mostly English language by default, but that has changed exponentially. Babel Street’s world-class entity matching technology measures over 100 features to calculate the similarity of entities across multiple languages. Despite advances in data management and the cloud, there are still multiple challenges and complexities with integration of these data elements. Challenges include spelling variances/phonetics, language translation issues, criminal evasion, human error upon input, typos, etc. Accessing data from a scattered landscape While there have been advancements in cloud technologies, agencies utilizing open-source data are typically working within a highly scattered data landscape and must use a wide array of tools to get at the relevant pieces. This fragmentation makes it difficult to run analytics and apply AI and machine learning at scale in order to derive actionable insights. Unstructured and relationship data are visualised through advanced link analysis As with many disciplines, artificial intelligence (AI) is changing the game when it comes to intelligence. NLP and AI algorithms are employed to enhance datasets for greater quality, usability, and completeness. Unstructured and relationship data are visualized through advanced link analysis, geographic heat maps, influential entity carousels, topic clouds, and patterns by time and day. Geographic heat maps The advanced algorithms accurately score and prioritize critical entities within the relationship network while providing the citations from which an AI/ML-based decision was made. “With the democratization of AI, the world is becoming flat,” says Moussa. “Just like the most prosperous countries, even the poorest countries have the most advanced capabilities to do damage. Third-world economies often present a scenario where the financial gain of nefarious schemes and low-to-no regulation combine to incentivize bad actors.” The Challenges of Name Matching Identity has been an ongoing challenge for intelligence analysis due to the vast complexity of linguistics, spelling and cultural variances, human error, as well as human evasion. Technology and data science approaches are maturing, however machine translation can still struggle with meaning. The best-of-breed natural language processing capabilities run against the data while it still is in its native language. This minimizes the occurrence of analytic errors caused by inaccurate machine translations. This minimizes the occurrence of analytic errors caused by inaccurate machine translations It’s tempting to think that name matching is like doing a keyword search. The complexity of language makes it more challenging. New names are constantly created, with multiple spellings and no set of rules to encompass how names are formed. They are variable across languages, scripts, cultures, and ethnicities. Culturally specific nicknames and aliases add to the complexity. Replacing human involvement The investigation of the Boston Marathon Bombing in 2013 spotlighted an example of the significance of intelligence analysis. Even though the FBI had issued a detain alert for Tamerlan Tsarnaev back in 2011, Tsarnaev managed to travel to Russia in January 2012; and in July 2012, he returned to Boston. He was not detained on either occasion because there were too many names on the lists, and Tsarnaev’s last name had been spelled differently from the way it was on travel documents, thus enabling him to get through security. With the Internet, social media, and the dark web, there’s been an exponential increase in public communications in various languages, adding significantly to the amount of analysis required to keep societies safe. Name matching, using AI, analyses multiple contextual data points across languages to arrive at matches. Name matching, using AI, analyzes multiple contextual data points across languages to arrive at matches A common misconception is that this technology will replace human intelligence. “It’s more accurate to recognize its role as a force-multiplier, allowing humans to focus on the on the harder problems and/or vetting the results of AI,” says Moussa. “The technology can efficiently analyze massive volumes of data and distill it into actionable information in a timely manner. It augments human capabilities, enabling analysis at speed and scale beyond human capacity, without replacing human involvement.” Commercial Technology to the rescue “When it comes to threat and identity intelligence, we face a risk-confidence gap, underscored by the challenge of integrating traditional tactics with the modern digital landscape,” adds Moussa. “We cannot ‘hire’ our way out of this problem. Instead, it is imperative that we adopt technology to scale our efforts and free humans to solve the harder problems that machines cannot solve yet.” The public sector loves to build things, but there are time-to-value and return-on-investment considerations to the ‘build or buy’ decision. When commercial technology can be leveraged by government, it frees resources up to work on problems that the commercial world hasn’t yet figured out, says Moussa. “The public and private sectors need to come together – one team, one nation, working together with mutual trust and collaboration,” he says.
Already a strong player, particularly in New Zealand and Australia, Gallagher is still climbing in the U.S. market, which it sees as a big opportunity to invest in the company. Active in the United States for 10 years, Gallagher undertook a more aggressive growth strategy about five years ago. There are 52 employees in Gallagher’s U.S. security business, and about half the workforce has been hired in the last couple of years. They have grown from three sales territories to 16, operated by a full sales and engineering staff. Culture of innovation sets As it happens, Gallagher’s U.S. headquarters is located a short drive from my home office in the wider vicinity of Atlanta. I missed seeing them at GSX in Dallas, so we scheduled an in-person visit to catch up on their company. Gallagher’s strong culture of innovation sets them apart, as does their “people-first” commitment, says Scott Elliott, Gallagher’s Executive Vice-President, The Americas. “We have intentionally recruited for a diversity of thought that drives the business,” says Elliott. “We are a people business.” Melissa Vidakovic, Director of Marketing, Americas; and Scott Elliott, Executive VP, Americas, at Gallagher Security's office in Canton, GA. Unified approach An advantage Gallagher has in the market is total ownership of their supply chain; it manufactures each of the hundreds of products used across their solutions, from plastic components to readers to controllers to their own software systems. Among other advantages, the unified approach enables tighter control from a hardening and cybersecurity perspective, enabling them to minimize any threat vectors or vulnerabilities. The strategy also avoids dependence on third-party suppliers, which was a huge advantage during recent supply chain disruptions. While competitors struggled with availability issues related to third-party manufacturers, Gallagher’s supply was uninterrupted. Gallagher’s commitment Gallagher uses the same norms as the nation and subjects its effects to inner and outer penetration As a manufacturer serving a broad spectrum of markets, it’s Gallagher’s commitment to the high end of the market (e.g., high-security applications), where the company incorporates core tenets such as authentication and encryption. Gallagher uses some of the same standards as the government and subjects its products to internal and external penetration testing. These core strengths are also integral to Gallagher’s complete product line. “If it’s good enough for a high-level customer, it’s good enough for Mr. Business Owner,” says Elliott. The New Zealand company was founded in 1938 and was the first company to commercialize the electric fence, which it still uses for its agriculture business sector, separate from the security business. Gallagher entered the access control business 35 years ago in 1988 when a product used to restrict access to fuel pumps evolved into broader access control. Gallagher platform In the intervening years, the product has grown into a unified platform that incorporates access control, intrusion detection, and perimeter detection in a single ecosystem. “The platform is all-encompassing,” says Elliott. “No other platform does all three.” Augmenting access control, intrusion, and perimeter protection, there are other applications available in the Gallagher platform, such as workforce management, health and safety functions, and a spectrum of features useful to a wider stakeholder community. Fatigue management applications For example, Gallagher can implement routine randomized checks to proactively mitigate potential risks such as drug or alcohol abuse, thus ensuring workers are fit to work, to operate various machinery and that they do not pose a threat to fellow employees or the company. “Fatigue management” applications can monitor the use of equipment to avoid repetitive injuries or manage how long an employee works at a job site, requiring a worker to swipe or tap a card to a reader mounted on a machine to monitor and limit the time they operate that machine. Mobile mustering provides location and identification of evacuees in case of an emergency. Impact of digital transformation Gallagher’s “Better Ways of Working” concept zeroes in on the impact of digital transformation Gallagher is also embracing the “digital transformation” of the industry. Security companies must adapt to a more agile workforce and shifting processes, says Elliott. Gallagher’s “Better Ways of Working” concept zeroes in on the impact of digital transformation on their workforce. They also seek to address the changing workforce, where Gen-Z’ers work side-by-side with tenured, experienced workers, and where creating trust is the best approach to closing the generational gap. Gallagher also seeks to educate the market on trends such as artificial intelligence (AI), machine learning, cloud adoption, various service delivery models, and other issues. Industry consolidation Gallagher has more than 1,200 employees; operates in 140 countries, from South America to Canada, Europe to the Asia-Pacific and Australia; and serves almost 16,000 customers. Gallagher is part of New Zealand’s growing technology export sector, which is growing 30% faster than the overall economy and is now the second-largest export sector in New Zealand. In an age of industry consolidation and a market dominated by corporate conglomerates, Gallagher is a privately held organization seeking to be agile and innovative, and to deliver customer value more quickly. Gallagher re-invests about 15% of its profits into research and development. “Our customer service is the primary reason people buy from us,” says Elliott. Security integrators Security integrators quickly appreciate the breadth and strength of the product line Gallagher positions itself as an alternative in a market in the midst of disruption. Brand awareness continues to be a challenge in the United States, and the sales team often hears the question: “Who is Gallagher?” Once the introduction is made, security integrators quickly appreciate the breadth and strength of the product line, says Elliott. “We allow our customers to select among best-of-breed platforms, and [using open systems,] we are not limited by the technology we offer,” says Elliott. “Our value proposition to the integrator channel is our focus on the relationship,” says Elliott. Supporting end users through an authorized, certified channel, Gallagher also emphasizes value, cost-competitiveness, and cybersecurity. “Our partner relationships are built around cultural alignment,” says Elliott. Product innovation perspective What’s ahead for Gallagher and for the industry as a whole? Hard to say, notes Elliott, given the unfolding of unpredictable geopolitical and financial trends. However, from a product innovation perspective, Gallagher will continue to evolve, balancing a dependence on “cash cow” legacy product lines with investment in leapfrog innovations such as frictionless access control, cloud platforms, and mobile systems. In general, Elliott predicts AI will yield an opportunity to analyze a person’s pattern of behavior and intent, thus enabling a security system to adapt down the road. “With the ability to predict with some degree of certainty what might happen, these capabilities will evolve,” says Elliott.
As the physical security and cybersecurity worlds converge, many industry professionals are finding themselves moving from one realm to the other. Or, more likely, they are embracing both disciplines as integral to the future of security as a whole. One security professional bringing her cybersecurity expertise to the physical security market is Wendy Hoey, Director of Sales, US Sales Leadership, North America, for Milestone Systems. With more than 23 years of experience in cybersecurity, Wendy Hoey now works with a global company dedicated to empowering people, businesses and societies with data-driven video technology. Author's quote Caught up with Wendy Hoey to discuss how the security market can harness innovation “I'm thrilled to be joining the physical security industry at this transformative time when there's such tremendous potential to update legacy systems with pioneering technologies like AI and the Internet of Things,” says Hoey. “I'm energized by the chance to collaborate with colleagues to help transform physical security, enhance predictive capabilities, and realize a shared vision of seamless protection across the digital and physical realms.” Caught up with Wendy Hoey to discuss how the security market can harness innovation to make the world safer and more secure. “The future is bright, and I'm honored to be part of this community,” says Hoey. Q: What can physical security learn from the world of cybersecurity? Hoey: Physical security can learn a great deal from the world of cybersecurity. With the rise of IoT and IP-connected devices, the lines between physical and digital security are blurring. Like cybersecurity, physical security needs to take a proactive approach to protecting core systems and perimeter access points. Understanding potential vulnerabilities and attacks is key. Physical security pros should continuously educate themselves on emerging technologies and threats and stay up to date on best practices. Adopting a customer-centric mindset is also critical. Rather than just selling technologies, physical security providers should focus on understanding clients' unique risks, objectives, and pain points. By taking cues from cybersecurity, the physical security industry can transform itself, innovate, and provide smarter solutions. Q: How is physical security a unique application for IT? How do physical security (and/or video) systems differ from “other” IT systems? Hoey: Physical security has unique challenges compared to traditional IT systems, but also shares some commonalities. At its core, physical security relies on networked hardware like cameras, access control and detectors that must be online and recording effectively at all times. This is like IT infrastructure in that uptime and availability are critical. With the rise of IoT, cyber and physical security are converging. Physical security systems have vulnerabilities that didn't exist before everything became IP-connected. Staying on top of emerging technologies and threats is crucial. At the end of the day, both physical and cyber security share the goal of minimizing organizational risk, and both disciplines must come together and cooperate to optimize security and safety. Q: How can security integrators ensure their workforce (i.e., installers) have the required IT skills to address the needs of the physical security market? Hoey: As security networks converge more deeply with IT infrastructure, integrators must invest in training to ensure their installers have the required skills. Whether pursuing vendor certifications, in-house training programs, or partnerships with IT services firms, integrators must recognize that security solutions require IT fluency. A willingness to upskill installers and keep pace with technological change will prepare integrators to deliver the solutions end users demand in an increasingly connected physical security ecosystem. Q: What is the role of the manufacturer to ease the application of IT technologies to the physical security market? Hoey: The role of the security manufacturer is to simplify and facilitate the application of IT technologies by serving as a trusted advisor and educator. Manufacturers must provide guidance, case studies, and domain expertise to help partners and end users understand the full capabilities of technologies and how they can be leveraged most effectively. Rather than just promoting a specific product, manufacturers should always take an active role in informing the channel and customers on available possibilities, bringing real partnership through tailored advice and solutions. Q: What challenges remain relating to implementing IT technologies in the physical security industry? How will new technologies (e.g., AI) transform the IT environment for physical security now and in the future? Hoey: When implemented thoughtfully, AI has enormous potential to transform physical security by helping security professionals identify anomalies and patterns in data to enable predictive analytics. With the right solutions, AI can act as a force multiplier by monitoring behaviors and giving security teams advance warnings before incidents occur. As AI and other emerging technologies mature, they will bring the industry in line with the most advanced security tools available. The future looks bright for a truly integrated physical and digital security environment with AI pioneering the charge.
Case studies
Finland’s Osuuskauppa PeeÄssä retail co-operative, a nationwide S-Group co-operative federation member, has deployed March Networks video surveillance systems across its footprint of 73 retail and service establishments. The co-op boasts 121,000 customer owners in Finland’s Northern Savonia region, whose capital and largest city, Kuopio, is 384 kilometers north of Helsinki. The 73 retail and service locations include three Prisma Hypermarkets, 29 S-Market grocery stores, 15 convenience stores, 15 restaurants, six ABC gas stations, three hotels, a SOKOS department store, and a Kodin Terra hardware store. March Networks video surveillance systems The rollout began in September 2019 and currently includes 85 March Networks recorders, a mix of 8000 Series Hybrid NVRs and 9000 Series IP Recorders, and more than 1,500 March Networks cameras. A new hotel and supermarket currently under construction will bring the camera count close to 2,000. “We used to have several different video surveillance systems and 10 different camera models from six manufacturers,” said Kimmo Keränen, IT Manager for PeeÄssä retail co-operative. “Maintenance was almost impossible and the picture quality in some cases was very poor.” Time management challenge Central management was a key feature for PeeÄssä retail while looking for in its new surveillance system “On top of that, there was no synchronized timekeeping, so one system could be five minutes off and another one could be an hour off. That was a real problem because correct timekeeping is everything when you’re looking for evidence.” For this reason, central management was a key feature PeeÄssä retail co-operative was looking for in its new surveillance system. “A majority of the 19 S-Group regional co-ops were already using March Networks systems, so the decision was easy to make,” said Jan Österlund, ICT Manager with SafeIT, a systems integrator and March Networks Certified Solution Provider serving the S-Group and PeeÄssä accounts. Central monitoring and management With more than 1,000 NVRs and tens of thousands of cameras across the larger S-Group co-ops, central management is a huge timesaver. Österlund can push out firmware upgrades and device settings with a few simple mouse clicks using March Networks Command Enterprise Software. The advanced system management software is ideal for managing large distributed video surveillance architecture. Its health monitoring and mass management capabilities make it easy to look after thousands of recorders and cameras from one central location. “We can schedule upgrades by location type and opening hours to minimize any interference with recording during business hours,” explained Osterlund. Recorders and cameras in use The 8000 and 9000 Series recorders are 32-channel or 64-channel devices with either 20 TB or 40 TB of onboard storage, sufficient to capture 30 days of archived video. The majority of the 1,500 cameras are March Networks SE2 Indoor and Outdoor IR Domes, but SE2 IR MicroBullets, SE2 Pendant PTZ Domes, and legacy analog cameras are also used for specific applications. Searchlight software integration Searchlight helps organizations gather business intelligence, which can help retailers with customer service S-Group is transitioning to a new point-of-sale system and has plans to integrate it with March Networks’ Searchlight for Retail software, which will allow the co-ops, including PeeÄssä, to identify suspicious transactions and instantly link to the associated video. Searchlight also helps organizations gather business intelligence, which can help retailers with operations, marketing, and customer service. “We are looking forward to acquiring the Brickstream 3D Gen2 sensors for queue management and people counting, and March Networks ME6 IR Domes for AI-powered analytics,” said Keränen. GDPR Compliance The March Networks system in place at PeeÄssä complies with the European Union’s General Data Protection Regulation (GDPR), which came into effect in 2018 and aims to protect the personal data and privacy of EU citizens. System features like privacy masks, which allow users to block out specific parts of a camera’s field of view, are important for meeting the regulation. “GDPR compliance is one of the reasons why we recommended March Networks,” said Österlund. Video access, training, and monitoring Video is currently monitored by guards in three control rooms, but managers also have access to live and recorded video from their locations. Altogether, approximately 100 PeeÄssä staff have access to the video. “Training everyone to use the system was very easy,” remarked Österlund. “The March Networks system is very user-friendly, so we supplied step-by-step instructions on how to log in, pick a camera, play the video, and export it.” Crime management Video is regularly used to supply evidence for shoplifting and internal fraud investigations Video is regularly used to supply evidence for shoplifting and internal fraud investigations, but the much-improved video quality from the March Networks system was also welcomed by local law enforcement. The Eastern Finland Police Department has mapped the location of PeeÄssä’s publicly facing cameras in the National Police Board’s database of surveillance cameras to help access video for criminal investigation purposes. “Almost every week, we are asked for video from the police department,” said Keränen. Installation, time, and cost savings SafeIT’s experience with the March Networks deployments at other S-Group co-ops helped to streamline the installation at PeeÄssä. “We supplied local integrators with clear guidance on how to set up the cameras and NVRs,” said Österlund. Standardizing on March Networks allows the PeeÄssä co-op to save time and reduce costs for system maintenance. The state-of-the-art video surveillance system is also much easier to use. “We are very satisfied with March Networks,” said Keränen. “It was a big project, but well worth doing.”
As the largest sporting goods company in China, Anta Group has more than 12,000 offline stores in 294 cities across the country, with more than 100,000 employees. Despite its massive scope, Anta can still keep orderly management of its stores, present neat and cohesive displays, and provide excellent shopping experiences to its customers. How do they do it? Let’s check it out. Overview Just like its corporate mission to integrate the sports spirit of "Going beyond oneself" into everyone's daily life, Anta Group also incorporates the sports spirit into its management, operation, and other business aspects. Anta constantly innovates and embraces new technologies, devoting itself to digital intelligence transformation to achieve the intelligent management of its stores and provide customers with a comfortable shopping environment and superb service experience. Digital intelligence operation concept Dahua set up intelligent and hierarchical store management that helps physical shops operate efficiently Dahua developed the new "SERVICE PLUS" digital intelligence operation concept for Anta. With its powerful digital intelligence capability, it significantly helped standardize Anta’s intelligent retail marketing system nationwide, breaking the gap between tens of thousands of physical stores. It set up intelligent and hierarchical store management that helps physical shops operate efficiently and develop rapidly while creating a high-quality shopping experience. Intelligent Transformation: The "Hub" connecting 12,000+ stores Previously, store inspections are done in person. With several stores across the country, this method is undoubtedly costly and time-consuming. With the establishment of a visual store operation management network, all videos of each store are gathered at the headquarters. Multiple management tasks can be completed through remote store inspection and evaluation, providing traceable data results and allowing the headquarters to play a central role in store management. Remote inspection The remote shop inspection enables the headquarters management personnel to quickly grasp the operation status of several stores. When they find problems in the store's sanitation and product placement, they can record the scene in real-time and quickly follow up and deal with the situation in time. This helps ensure a comfortable shopping environment and timely service for customers. Easy store management The Dahua solution enables store managers to check the past on-site operation of the store Moreover, it also allows managers to quickly manage each store without having to travel to the site. The Dahua solution enables store managers to check the past on-site operation of the store, especially in case of an event. The details can be easily traced through video recordings to help customers solve issues promptly. As a result, the Dahua solution has significantly helped Anta Group reduce the management cost of the headquarters by more than 50%. Accurate customer flow statistics Furthermore, collecting accurate customer flow statistics used to be a challenge for their store management. Through the professional customer flow statistics camera, accurate customer flow data are collected. The management personnel can intuitively view the number of incoming customers in each store at each period, which can help them to reasonably arrange staff schedules and ensure that customers get excellent service even during peak hours. Store promotions can also be strategized by comparing customer flow statistics on regular days with relevant store activities. Establish a smart network of 20+ regions To better manage the Anta stores, management is carried out by divisions and hierarchies. In addition to the unified management of the headquarters, different regions need their management authorization. A region may also have a management structure based on superiors and subordinates, which is often troublesome and complicated. Remote store management Different management roles can easily check the situation of the stores, making business management more targeted The Dahua solution reorganizes and integrates the remote store management authority based on the internal organizational structure of the company to build a remote management "network". While ensuring the parallel supervision of multiple stores, it realizes clear authority distribution of more than ten management roles. Different management roles can easily check the situation of the stores under their jurisdiction, making business management more targeted and more efficient. In addition, when managers find any problems through remote shop inspection, they can directly call the corresponding store staff through the front-end device, and immediately correct the fault found to ensure a high-quality shopping environment at all times. Promote and accelerate business expansion For newly opened stores all over the country, Dahua provided a one-stop scenario-based network and standardized services, which were rapidly replicated by the construction of urban model sites. It offers standardized services for single-scenario, multi-scenario, and even cross-domain businesses. Thousands of upgraded stores can fully utilize the existing network of the store and quickly organize various intelligent devices online through wireless access, providing strong technical support for the rapid expansion of the store. Standardized management By implementing digital and intelligent management of the headquarters, regional offices, and stores, Dahua helps Anta Group achieve standardized management and operation of their physical stores, providing customers with an excellent shopping experience. Moving forward, Dahua will continue to implement scenario-based solutions, delve deeper into business chain scenarios, and help enterprises develop through digital intelligence transformation.
To keep residents and visitors safe, 24 hours a day, gated communities need comprehensive, reliable security solutions. At Copperleaf Golf Estate in Centurion, South Africa, these needs have been met with an advanced security solution from Hikvision, which incorporates AI-powered optical, thermal, and license plate recognition cameras that provide real-time alerts in the event of a perimeter breach or other security incident. The challenge Securing gated golf and residential community Residential gated communities provide significantly improved security compared to 'open' streets. In particular, gated communities can tightly control the vehicle and people’s access, helping protect residents and visitors to a far greater degree than would otherwise be possible. Security challenges Perimeters need to be checked to prevent security breaches and to support real-time responses to prevent theft But gated communities also face specific security challenges. As well as requiring physical walls or fences to prevent unauthorized people from entering, site perimeters need to be checked constantly to prevent security breaches, and to support real-time responses to prevent theft, vandalism, and other negative outcomes. These were the challenges facing Copperleaf Golf Estate, a gated residential community just 15 minutes outside Centurion in Mnandi, Gauteng, South Africa. The community offers a range of lots and houses in a peaceful setting, as well as South Africa's second 'Signature' golf course designed by the legendary South African professional golfer Ernie Els. Perimeter protection solution To protect residents and visitors, Copperleaf needed a perimeter protection solution to prevent unauthorized vehicles or people from entering the site. To achieve this goal, they worked with Independent Technology Security Systems (ITS Systems), an integrated security and building management solutions expert. "To keep everyone safe, Copperleaf needs to keep a close eye on their perimeter wall and other areas of the site, including the golf course. They also need to maintain vigilance even in adverse weather conditions, such as heavy rain and fog, and after dark." Theo Mienie, Managing Director from ITS Systems says, "After conducting a thorough review of the facilities, we concluded that Hikvision's solutions are a good fit for Copperleaf." The solution A comprehensive solution from Hikvision AcuSense Fixed Bullet Network Cameras constantly protect the site's perimeter wall, the Els golf course, residential streets To provide the exceptionally high levels of security residents and golf members expect, ITS Systems has implemented a comprehensive Hikvision security solution for Copperleaf. This incorporates more than 100 AcuSense Fixed Bullet Network Cameras that constantly protect the site's perimeter wall, the Els golf course, residential streets, and security vetting rooms and offices. Security for the 8km perimeter wall is provided by over 50 Hikvision Thermal & Optical Bi-spectrum Network Bullet Cameras with intrusion detection capabilities up to a distance of 700 meters. If the perimeter is breached by a person or vehicle, an alert is sent to the security team automatically, and in real-time. ANPR Cameras, I-Series NVR and iVMS-4200 Hikvision ANPR Cameras have also been installed at the site's three entrance and exit points, providing an overhead view of vehicles coming into and leaving the estate 24 hours a day. These cameras offer license plate recognition technology to ensure that only authorized vehicles are admitted. The Copperleaf Security team checks feed and alert from the cameras using Hikvision's advanced control room infrastructure. This includes the Hikvision I-Series NVR and iVMS-4200 software and monitors, which display video footage and alerts, allowing the security team to take immediate action in the event of a suspected security breach. The benefits Efficient operation and all-around protection for peace of mind With the bullet network cameras' remote patrol capabilities, the security staff can visually check all sites Copperleaf Gold Estate has achieved alarm efficiency and labor cost reduction with the help of AI-embedded thermal cameras and AcuSense bullet network cameras, which can greatly reduce false alarms and provide accurate, real-time threat detection that distinguishes people and vehicles from other targets. Copperleaf has also minimized expenses on physical patrols. With the bullet network cameras' remote patrol capabilities, the security staff can visually check all sites using high-definition cameras based on patrol schedules, reducing requirements for physical patrols and other interventions. Efficient and effective "We no longer spend our time carrying out physical security checks and responding to and investigating false alarms," says Phineas Thosago, General Manager from Copperleaf Golf Estate. "Instead, we can focus 100% of our effort on real threats, which makes us far more efficient and more effective as a team and helps us maximize security for our residents and visitors." Deep-learning video analytics The thermal cameras feature deep-learning video analytics in all weather and light conditions The site is protected 24/7/365, even in adverse weather conditions. The thermal cameras feature deep-learning video analytics in all weather and light conditions, ensuring that Copperleaf Golf Estate is protected 24x7, 365 days a year. "Copperleaf needed cameras that could withstand all kinds of adverse weather conditions," says ITS Systems' Theo Mienie, "The Hikvision cameras provide the reliable, always-on capabilities they need. Copperleaf Golf Estate has now achieved an extremely high level of security for residents and visitors." AI features Combined with the AI capabilities of Hikvision cameras – the advanced features ensure that security threats can be detected accurately and addressed immediately. "We are taking advantage of AI features that automate alerts and help us work faster and better," says Phineas Thosago. "It just shows how quickly the security industry is evolving that these kinds of features have become accessible for small and medium-sized businesses." Copperleaf Golf Estate’s Phineas Thosago says, "We can now detect and respond in real-time in the event of a security incident, which means total peace of mind for our residents and visitors to the golf course."
When they talk about digitalization, there is one topic that keeps coming up: Smart Office. Intelligent IoT solutions that makes the users’ everyday lives safer, more comfortable, and more efficient. Systems to centrally manage employees' access with no keys and physical cards - face recognition, manage employee time tracking, and secure office printing with the embedded face recognition reader, are now seen as state-of-the-art. Dürr, founded in 1896, is a mechanical and plant engineering firm in the world. As one of the Dürr Group’s biggest sites, the Dürr China site covers a production area of 33,000 m². The modern office complex of Dürr China covers a total building area of 20,000 m². and around 2500 employees work together in there. Improving canteen management In such a huge site with so many people, safety is paramount concern. Dürr wanted to have a simple, easy-to-use, one-stop solution for security management. The upgraded system should be robust enough to keep up with the quick pace of factory operations and to minimize the risk of COVID-19 cross-infection. The system should benefit workers and employees and be fit for the high-quality smart office At the same time, the system should benefit workers and employees and be fit for the high-quality smart office. Dürr hoped it can promote the employee dining experience through improving canteen management, and supporting employee data privacy. In other words, Dürr put forward two requirements for the new solution which can support smart offices and can protect employees’ health. The use of unique biometric characteristics delivers the most reliable and accurate identity authentication and verification of a person. Business access control Biometric systems deliver the only irrefutable proof of presence with true identity, making it easy to protect data privacy and which is an essential part of the smart office. Touchless access controls came to the fore during the COVID-19 pandemic, as people sought to minimize interpersonal and surface contact. Driven by years of innovation, Anviz offers a broad range of biometric technology terminals that benefit business access control & time and attendance management. The FaceDeep 5 adopted the latest deep learning algorithm that could help with secured and seamless access control by enabling touchless access around the building and reporting for no-mask wearing, it's equipped with a Linux-based dual-core CPU and it could support up to 50,000 dynamic face databases and rapidly recognize users within 2 meters (6.5ft) in less than 0.3 seconds. Personnel identity verification All Anviz FaceDeep series terminals can work with CrossChex Standard All Anviz FaceDeep series terminals can work with CrossChex Standard, which is a personnel identity verification, access control, and time attendance management system. To support staff members clock in and out at the turnstile of the industry gate, the FaceDeep 5 works well in various challenging outdoor environments, like under strong light or in the rain. It is possible to identify for full face and half face and it is impossible to trick it by presenting a photograph. In order to optimize dining rules, employees should not clock in many times, which means the same person should not be recorded multiple times, which is conducive to doing a headcount. Anviz customized the function module for Dürr, and make it simple for the canteen administrator. Supporting health guidelines To maintain data privacy, the same function is duplicated on their printers, the printers also could be switched on by faces, and printers will automatically connect to their computer accounts. This also helps energy-saving and protect data privacy. According to Dürr’s request, some doors could be controlled separately on CrossChex as well as setting different permissions on different floors. Anviz touchless solutions support health guidelines for disease control Anviz touchless solutions support health guidelines for disease control, as they minimize surface contact opportunities and human-to-human interaction. As the deep learning algorithm within FaceDeep 5 could detect users wearing masks or not, there is no need for staff members to take off masks. Supporting multiple applications Commenting on the new system, Henry, the IT Manager working in Dürr for 10 years presented, "During mealtime, we could get food more quickly since we just swipe faces and go on instead of taping cards." Moreover, there is no need to check out face-to-face, because the system can record and calculate spending automatically. "Meanwhile, we would not worry their documents are printed by others by mistake for our faces are keys to open the printers," Henry added. The CrossChex interface was so intuitive that only a short training was required for Dürr managers to manage it on their own. The CrossChex interface was so intuitive that only a short training was required The integrated system solution enables administration to be centralized into one efficient and cost-effective system. CrossChex is flexible enough to support multiple applications for managing not only physical access (e.g. buildings) but also logical access (time and attendance, etc.). Smart face recognition hardware "We evaluated different biometric-centric authentication solutions and selected the CrossChex because it offers a complete solution, including both adaptable software and smart face recognition hardware," said Wilfried Diebel, Head of the Dürr IT team. "Face recognition in the Dürr can be used in several places, including entrances to the building, turnstiles, canteens and to securely printed documents by authenticating at enabled printers with their faces." "We are delighted to be working with Dürr on one of the largest office building projects in Eastern Asia," said Felix, the Director of Anviz Access Control and Time Attendance business unit, "Our ongoing program of developing our application will ensure working at Dürr remains a positive and secure experience for those who work there into the future."
Seaport terminal has become one critical infrastructure everywhere around the world. Thousands of trucks entered the seaport each day, therefore, it needs special attention when it comes to monitoring and tracking the incoming trucks in real-time. Especially in the COVID-19 situation, the number of people that can enter the seaport is limited, and increased port congestion. With the increasing demand for IoT, war rooms can help the seaport operator efficiently manage the seaport terminal operation while maintaining the limited number of people entering the seaport. The administrator can also easily review the performance of the seaport operation and take corrective action to increase operational productivity. Easily real-time tracking Using the NViS 1482, which is equipped with an Intel® SoC 8th Gen Intel Atom® processor X series and Celeron® J series, taking a huge leap forward in terms of its graphics capabilities with Intel® UHD Graphics. It may stream up to 11-channel in H.265 codec with the resolution of live view + recording at 2MP (1080p, 1920 × 1080). These specifications give NViS 1482 the ability to drive a maximum resolution of 4KP60 on displays, giving the supervisor to easily tracks the incoming trucks in real-time. Cost-Effective Solution NViS 1482 support build-in 8 PoE (Power-over-Ethernet) port all in one, it friendly supports front-end and back-end as follows: Front end: DivioTec Network Cameras a) Connect up to 6 cameras for 2 gantries, each gantry includes: 2 units 2MP Bullet Network Cameras NBR126PA 1 unit 12MP Fisheye Network Camera NFF273 b) It can directly provide the network transmission and power supply of the front-end network camera. Back end: Milestone Video Management System To send the real-time video result to the war room through a 2.5GbE LAN port To use the LAN(1GbE) port connect the LTE router to remote maintenance To save the video recording in 30 days as a backup The all-in-one design may allow the user to save up the TCO (Total Cost Ownership) of the edge recording that needs to be used while still providing great quality at the same time. Key Features For Application Needs Supports 8th Gen Intel Atom® processor X series and Celeron® J series 1 x SATA supports 2.5” HDD/SSD (M.2 as either option) 1 x SATA supports a 3.5” HDD Multiple displays (HDMI+DVI-I) 1 x 1GbE Intel® Ethernet + 1 x 2.5GbE Ethernet Supports 8-port PoE switch (PSE up to 120W)
Costex Tractor Parts of Miami, Florida is a forty-year-old distributor of replacement parts and engines for Caterpillar and Komatsu heavy equipment. When they were preparing to build a new, 350,000-square-foot headquarters in Miami, Florida, they knew they needed a state-of-the-art security system designed, installed, and configured specifically for the facility. It contracted E.G. Telecommunications & Technologies, security, and telecom installer, to deploy a complete Dahua security solution that was scalable, easy to use, and dependable. Challenges Before construction began, Evaristo Galvez, founder and president of E.G. Telecommunications & Technology (EGT&T), laid out a blueprint for the new security system. Due to the facility's massive square footage, which includes offices, a warehouse, and a parking lot, he decided to use fiber optic cable. “The system is so huge I had to design it with fiber optics – I needed to cover distances of 600-800 feet,” he explained. “In the end, we installed 20,000 feet of fiber.” Scalable security system Costex wanted each division to be able to access only the cameras that covered their respective departments Another effect of such a large building was that while it needed a lot of camera coverage, Costex wanted managers of each division to be able to access only the cameras that covered their respective departments. At the same time, Costex's owner and CEO wanted to be able to access all the cameras from the comfort of his office. Additionally, Costex wanted to implement a system that was scalable as their facility grew, they wanted to be able to easily add more cameras and storage devices and integrate them seamlessly with the existing system. Solution Dahua had worked with EGT&T before and became the first choice for this project because of its high-quality products, economical price, and dependability. Once he designed the system, Galvez turned to Luis Gomez and Greg Larson of Dahua Technology USA for product recommendations. Not only did they provide guidance on which devices would be best for the job, but they also visited Costex with him to do product demos, and they were able to offer bilingual English-Spanish support. IP transmission, PoE switch The Discovery feature lets the switches discover cameras and recorders quickly and automatically In the end, Galvez deployed a full Dahua system including 190 IP cameras, recorders with a total of 256 channels of recording, a Digital Surveillance System (DSS) Server (DHI-DSS4004-S2), an Extended Video Server (EVS) (DHI-EVS5016S-R), and thirteen switches of either 16 ports (DH-LR2218- 16ET-240) or 24 ports (DH-LR2226-24ET-360). These transmission devices are layer 2, managed, PoE switches that have two 1000 base combo ports and two 10/100/1000 base T-ports compatible with fiber or Cat5e/6. Galvez chose these switches due to their fiber capabilities and straightforward integration: they integrate with the web management portal to make system supervision easy, and the Discovery feature lets the switches discover cameras and recorders quickly and automatically. DSS Express Dahua's DSS Express allowed Costex managers the access they needed to manage their specific departments. "We were able to provide nine client stations, each with the capability to access about 20-30 cameras that covered their department and not access cameras of other departments," explained Gomez. "Each manager had access to their cameras in their office on a 50" TV with a client PC attached. At the same time, the Costex CEO was set up in his office so that he could pull footage from any camera." Remote monitoring, storage The DSS platform will let Costex access remote locations from the main location as its footprint gets bigger – Costex plans to expand into two more buildings and is already adding more cameras. With nearly 200 cameras, storage capabilities and reliability are crucial. The total storage requirement will be more than 240 TB. Upon Dahua's recommendation, Galvez added a 16 HDD EVS (DHI-EVS5016S-R) to the system to create redundancy. 32-channel NVRs The 32-channel NVRs, each of which has a built-in storage of 24TB and can accommodate up to 4K resolution "This gave Costex a failover recording system," said Gomez. "If anything happened to any of the NVRs or the mainframe, this lets them keep recording." The 32-channel NVRs (DHI-NVR6A08-32-4KS2), each of which has a built-in storage of 24TB and can accommodate up to 4K resolution, also have full redundancy on their hard drives. Gomez highlighted the significance of this configuration, "If there is any damage to one NVR, you only sacrifice 32 cameras. We made sure that each recorder was receiving inputs from cameras in multiple departments so if an NVR failed, Costex would never lose all the footage from a single department." Results “When a company gives you three years’ warranty for replacement and two more years for repair, that means you can count on them,” Galvez remarked. "I appreciate the support I get from Dahua," Galvez said. "They came with me to the building when I started working on the deal their live demonstration was really important. When spec-ing a project, you can write everything on paper, but people want to see reality. Dahua came with a demo system, and Costex got to see everything." Easy to use "We were excited to be a part of it from the beginning," Larson remembered. "Everything in the building, from the light switches to where the cameras go, was very thoughtfully planned out." "Costex's leadership team was very detailed in knowing everything that was going in that place, and we wanted to create a reliable system that met complex needs while being easy to use." Smart Search feature Using the Smart Search feature of the NVR, Costex caught a construction worker causing damage and shared the incident Costex immediately noticed the benefit of their new Dahua system. During the construction of their new warehouse, a window shattered. Using the Smart Search feature of the NVR, they were able to efficiently pull the incident out of three days' worth of footage and prove that the window had broken on its own, and then claim the warranty on it. They also caught a construction worker causing damage and shared the incident with the construction company. Reliable system "Everything has been working perfectly, and the system is reliable. Dahua gives us great support here: in no more than 24 hours, we can fix anything having to do with the cameras," remarked Galvez. From being able to assign camera access to specific users, to know that their video data is backed up twofold, to being able to easily scale, Costex was happy with their Dahua solution, Galvez reported. Costex was happy with EGT&T as well: they awarded the company with a certificate recognizing their outstanding work. "In appreciation of their valuable contribution in the construction of the Costex Tractor Parts headquarters," it read. "Thank you for helping make our dream a reality."


Products


Round table discussion
In the complex world of physical security systems, standards can enable disparate systems to be combined to function together as a cohesive whole. Standards help to ensure that all the “pieces” fit together to create a clear, unified picture. More broadly speaking, standards also play a role in ensuring best practices are deployed in a range of security-related situations. We asked this week’s Expert Panel Roundtable: Which standards have had the greatest positive impact on physical security?
There is a complex and interdependent relationship between security and productivity. Good security is needed to make productivity possible, but security measures could, in some instances, hinder workplace efficiency. New technologies are enabling security systems to have a more profound and positive impact on productivity by yielding better intelligence to guide the improvement of workplace practices. Multiple systems that work together, rather than separately, improve the productivity of security processes. We asked this week’s Expert Panel Roundtable: How can physical security systems contribute to productivity?
Every day, the physical security industry succeeds in applying technologies that make the world a safer place. Manufacturers, integrators, and end users are eager to share their success stories, and their successes can inspire others to implement the same technology solutions. But, occasionally, technology does not live up to expectations and, in fact, fails to perform as promised. We asked this week’s Expert Panel Roundtable: How has the physical security industry failed to meet customer needs?

Multi-Residential Access Management And Security
Download
Guide For HAAS: New Choice Of SMB Security System
Download
Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
Download
Hikvision: Solar Powered Product Introduction + HCP
Download
Artificial Intelligence
Download