Perimeter security
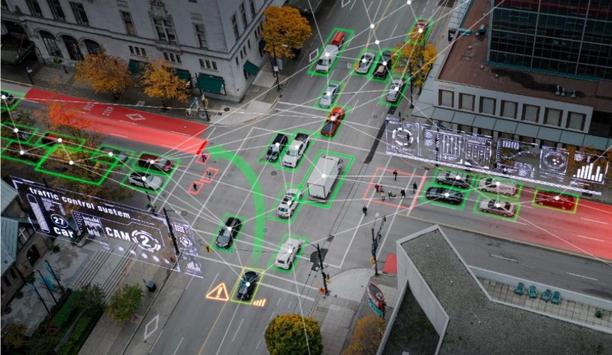
The integration of cutting-edge technology, spurred on by innovation, is propelling efficiency and productivity to new heights. In turn, this opens up prospects for manufacturers across security, smart building, fire safety, and mobility sectors through the rising development of IoT and AI trends. To capitalize on the opportunities created by technological advancements, Messe Frankfurt and CCPIT-Shanghai are partnering on a new security, safety, and fire protection fair – Intersec Shangha...
When it comes to protecting the environment, the security industry has historically been perched on the sidelines. For instance, the amount of electricity that physical security systems use is minimal when compared to the total energy usage in a typical building. However, as awareness of environmental issues has surged, and as some of the "low-hanging fruit" has been harvested, attention has come back to opportunities for additional, if small, savings. The lifecycles of security products are als...
Quanergy Solutions, Inc., continues to gain momentum since reformulating its business operations to focus exclusively on physical security and business intelligence applications. Quanergy’s groundbreaking 3D LiDAR (Light Detection and Ranging) solutions provide users with real-time data to detect potential threats and abnormalities for immediate remediation with unparalleled levels of precision and range in virtually any environment or operating conditions. Accelerate Quanergy&rsquo...
Gunnebo Entrance Control has announced its acquisition of DG Concept and Diadem, a French entrance control, design, installation, and service specialist, marking a significant step in reinforcing its commitment to providing innovative solutions and exceptional service to global clients. DG Concept and Diadem is a family-owned business servicing the French market, with a team committed to delivering high-quality service solutions tailored to the unique needs of its clients. Service expansion G...
ZBeta, a pioneer in delivering comprehensive physical security consulting services, announced the launch of its engagement model designed to transform the landscape of security strategy development and implementation. This comprehensive approach extends beyond traditional consultancy services, providing clients with a sustained advisory, advanced technology and system design, and ongoing operational support. Integrity of security architectures Rooted in a philosophy that seeks to overcome the...
Aqua Security, the pioneer in cloud-native security, and Orca Security, the pioneer in agentless cloud security, announced a new partnership to deliver best-in-class cloud-native security through a deep integration between their platforms. Joint customers will benefit from the powerful combination of multi-cloud visibility and security provided by the Orca platform combined with multi-and hybrid cloud runtime protection for cloud-native workloads offered by the Aqua platform. Right cloud-...
News
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announced the launch of “Powering Innovation 2024: A Genetec Empower 360 Roadshow.” The Middle East tour will spotlight the company’s product roadmap, featuring the latest innovations and strategic vision for the future. In partnership with Axis Communications, HID Global, and Ipsotek, the event will commence in Doha on May 2nd, followed by pivotal stops in key markets such as Abu Dhabi on May 13th and Riyadh on May 16th. Evolving trends and best practices Delving into crucial topics impacting physical security professionals, this roadshow will feature Genetec’s experts exploring biometrics, video analytics, and access control solutions that go beyond the door. Central to the discussions is the exploration of a unified approach to seamlessly integrate these solutions. Central to the talks is the quest for a unified policy to seamlessly integrate these keys The event will cover important themes around the state of regional physical security and the evolving trends and best practices for safeguarding assets and infrastructure. Attendees will gain exclusive insights into the latest Genetec technologies, upcoming product launches, and strategic initiatives shaping the industry landscape. Additionally, they will have the opportunity to engage in live demonstrations of solutions and connect with both industry experts and partners to explore emerging trends and technologies. Future of physical security "At Genetec, we're committed to shaping the future of physical security and public safety through innovation and collaboration," said Firas Jadalla, Regional Director – Middle East, Turkey & Africa, Genetec Inc. "Our goal is to equip our customers with the resources and knowledge they need to effectively navigate the complex world of physical security. The upcoming roadshow is a testament to our dedication to empowering professionals with cutting-edge solutions. In collaboration with our long-standing partners, we hope this event paves the way for a safer, smarter tomorrow." Advanced security capabilities The “Powering Innovation 2024: A Genetec Empower 360 roadshow” will also showcase Security Center SaaS, a massively scalable, open, and unified software as a service (SaaS) solution. The new offering combines access control, video management, forensic search, intrusion monitoring, automation, and many other advanced security capabilities.
The PSA Network, the world’s largest consortium of professional systems integrators, announced the addition of Kantech from Johnson Controls to its technology partner roster. Kantech offers a full suite of reliable, easy-to-install, scalable access control products. "Kantech provides the elite network of security integrators with expanded options for access control technology,” said Matt Barnette, president and CEO of the PSA Network. “Kantech’s innovative solutions are a strategic addition to our portfolio and give our members dependable access control technology for smaller businesses to large-scale clients.” Kantech’s flagship solution Founded in 1986, Kantech provides integrated access control technologies that are easy to install right out of the box, scalable, and reliable for small to medium-sized businesses to enterprise-scale deployments. Kantech’s flagship solution, EntraPass security management software, and KT door controllers, allow for simpler configurations and provide robust reporting to enhance the user experience for both the installer and the operator. Kantech provides integrated access control technologies that are easy to install right out of the box “We are tremendously excited to announce our new partnership with the PSA Network,” said Jason Edler, North American director of sales for Kantech. “This collaboration brings together Kantech's industry-pioneering access control solutions with PSA's extensive experience and nationwide reach in the security industry. We believe this partnership will be a game-changer for the security market, offering greater choice and value to security professionals across North America.” VMS digital video management system Nothing is more vital to the health of an organization than making sure that its people, material assets, and operations are safe and secure. Kantech’s solutions address the full scope of risks that might arise, including risks that other security systems such as burglar alarms and intrusion detection simply are not designed to handle. By preventing people from entering places where they do not belong, Kantech’s hardware and software protects against theft as well as liability and disruption to operations. For additional convenience and security, Kantech solutions can seamlessly work with the exacqVision VMS digital video management system to provide a cohesive access control and video solution. Kantech also offers out-of-the-box integration with DSC intrusion panels, all managed from a unified software package. PSA offers solutions from pioneering security and audio-visual manufacturers.
ISC West 2024, held in Las Vegas, marked a significant milestone for PureTech Systems as it announced reseller agreements with two major companies in the security industry, i-PRO and Magos. This strategic move not only expands PureTech Systems’ portfolio but also reinforces its commitment to provide the most comprehensive, easy-to-integrate, and reliable AI-boosted, geospatial video analytics and sensor fusion software solution for perimeter protection. With these initiatives, PureTech Systems aims to deliver a comprehensive turn-key solution equipping organizations with the tools they need for effective perimeter security and threat detection. Expanding horizons with i-PRO The addition of i-PRO cameras in PureTech’s arsenal brings together PureTech's geospatial AI-boosted video analytics and i-PRO's cutting-edge cameras. This collaboration is poised to offer unparalleled situational awareness, enhancing overall security measures and operational efficiency. During the event, PureTech illustrated the power of this combined technology, offering attendees a direct glimpse into the enhancements it promises for surveillance and perimeter security. Forging ahead with Magos Reseller agreement with Magos introduces an exciting addition to PureTech’s product lineup Similarly, the reseller agreement with Magos introduces an exciting addition to PureTech’s product lineup. Magos is known for its cost-effective, low-power, high-performance radars, which, when coupled with PureTech’s patented video analytics, promises to enhance security posture and operational performance. The synergy between Magos’s radar systems and PureTech’s AI-boosted geospatial video analytics was demonstrated through various recorded demonstrations at PureTech’s booth drawing attention from industry professionals and potential clients alike. A successful showcase The atmosphere at ISC West was charged with a growing number of innovative and forward-thinking professionals united by a shared goal of securing the future. The success of ISC West 2024 for PureTech Systems was not just in expanding industry affiliations, but also in the optimistic reception from the market and the potential for future growth opportunities these collaborations could unfold. Industry experts and attendees praised the strategic direction PureTech is taking, highlighting the company’s initiative to continue to deliver technological advancements to the security sector. Announcement of the reseller agreements with i-PRO and Magos not only enhances PureTech's market ISC West also provided an excellent platform for networking, with PureTech Systems capitalizing on the opportunity to connect with other industry pioneers, current and potential clients. The event facilitated rich discussions on emerging trends, current challenges, and innovations in security technology, further positioning PureTech at the forefront of the industry. ISC West 2024 proved to be a success for PureTech Systems. The announcement of the reseller agreements with i-PRO and Magos not only enhances PureTech's market offering but also sets the stage for a new era of delivering turn-key, integrated security solutions. As PureTech Systems continues to navigate the evolving landscape of security technology, its participation in ISC West has undoubtedly bolstered its position as a pioneer committed to excellence and innovation in the industry. Looking Ahead As they look forward to the next big events, PureTech Systems will be exhibiting at the Border Security Expo at booth #1001 in El Paso, TX in May, and later at the GSX in booth #1954 in Orlando, FL in September. These events will provide additional opportunities for PureTech to showcase its geospatial AI-boosted video analytics and integrated security solutions.
DSSL Group, the security systems company, has rolled out a new field service management system from BigChange. The cloud-based system incorporates vehicle tracking, a mobile workforce app, intelligent job scheduling, and an online customer booking portal. The system has already helped the Essex-based company offset more than 200 tonnes of CO2 and achieve net zero running for its fleet of vehicles, as well as reducing paper use by around 20,000 sheets a year. Disparate and outdated systems Predominantly specializing in Local Authority CCTV systems and access control systems for Housing Associations, DSSL operates a mixed fleet of more than forty vans and five cherry pickers from its regional operation centers in Essex, Leeds, and London. Completing around 100 planned jobs a day with an additional 15-30 out-of-hours callouts, DSSL implemented BigChange to replace a number of disparate and outdated systems. Implementing BigChange, DSSL has very reduced its back-office authority resources Since implementing BigChange, DSSL has significantly reduced its back-office administration resources. Automated workflows and integration of management systems have meant that two, full-time staff members have been redeployed within the business equating to a saving of around £60,000 per annum. DSSL is also realizing improvements in cashflow due to more timely and accurate invoicing and improved management reporting. Separate tracking system “Prior to BigChange we had a job sheet system that was server-based, we used Google Calendar, a separate tracking system and multiple spreadsheets to manage daily activities such as job raising and invoicing,” commented Aaron Stephens, Managing Director of DSSL Group. “Engineers couldn’t create jobs when responding to call outs, which meant we needed a dedicated member of staff to raise these retrospectively and chase engineers for the required information to close the job for invoicing. We also had another member of the admin team whose job it was to print completed job sheets and get them marked up for invoicing.” Cloud-based system DSSL selected the BigChange job management system, which incorporates a mobile workforce app DSSL selected the BigChange job management system, which incorporates a mobile workforce app, customer relationship management (CRM), job scheduling, live tracking, financial management, and business intelligence tools in one system, after just one face-to-face demo. “We knew how our business operated and the workflows that were required to get jobs done and invoiced,” he continued. “However, we also knew this was long-winded. We knew we wanted a cloud-based system and it very quickly became apparent that the BigChange methods and processes were aligned with what we needed to achieve, and the functionality and vision was there to save us resources from day one, boost customer service and support us as we continue to grow.” Real-time sharing DSSL customers are also noting the changes in the business with real-time sharing of information DSSL customers are also noting the changes in the business with real-time sharing of information between the field and the office, and more detailed and comprehensive reporting. Southern Housing, one of the largest Housing Associations in the UK with more than 45,000 homes across London, the South East, and the Midlands, uses DSSL access control solutions and commented, “We are delighted with DSSL and their performance as they continue to deliver against our targets and KPI’s. Best of all is their ability to communicate and put in place processes and procedures to keep customer satisfaction at 98% and complaints to a very low level.” Additional training requirements Some additional features within the BigChange system, such as vehicle checks, driver behavior alerts, and improved field reporting, are also helping DSSL look after their workforce promoting safer and greener driving and identifying additional training requirements. DSSL Group is a family-run security solutions integrator whose services include bespoke designs for security installations, tailored planned maintenance, and reactive repair for all types of security systems across the UK. Founded in 1998 by Dave Stephens, DSSL Group was formed in 2009 and is now run by Dave’s eldest son Aaron Stephens as Group Managing Director with his two brothers alongside him on the board. The business continues to grow, having recently upgraded over 20 town center CCTV systems and attended over 30,000 jobs in the past year, and is committed to sustainable operations.
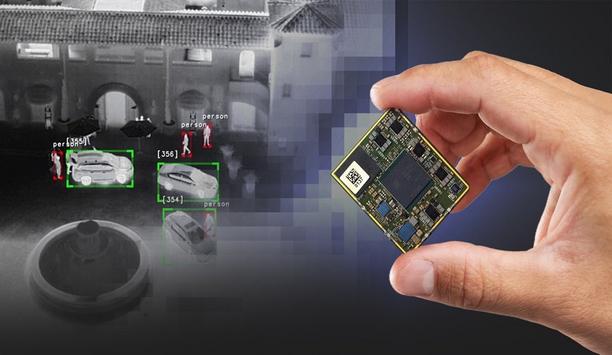
Teledyne FLIR, part of Teledyne Technologies Incorporated announced Teledyne FLIR AVP, an advanced video processor designed to power Teledyne FLIR’s Prism™ AI and computational imaging at the edge. The AVP incorporates the latest Qualcomm QCS8550, the most advanced mobile processor chip from the pioneer in mobile, automotive, and robotics system-on-chip (SoC) technology. AI performance The AVP provides best-in-class artificial intelligence (AI) performance within a small, lightweight, and low-power module for thermal and visible camera integration into unmanned aerial vehicles, robots, small gimbals, handheld devices, and fixed-mounted security systems. AVP runs the Teledyne FLIR Prism AI and ISP software libraries and interfaces with the Boson® and Neutrino® thermal infrared imaging camera modules and a wide range of popular visible cameras. Prism AI and ISP software Prism AI is a powerful perception software designed to detect, classify, and track targets or objects Trained on the world’s largest thermal image data lake of more than 5 million annotations, Prism AI is a powerful perception software designed to detect, classify, and track targets or objects for automotive autonomy, automotive automatic emergency braking, airborne camera payloads, counter-drone systems, ground intelligence, surveillance and reconnaissance (ISR), and perimeter security. Prism ISP is a comprehensive set of image processing algorithms that include super-resolution, image fusion, atmospheric turbulence removal, electronic stabilization, local contrast enhancement, and noise reduction. SWaP-optimized processor “The new AVP is the most powerful and SWaP-optimized processor on the market today, running AI workloads up to five times faster than competitive offerings,” said Dan Walker, vice president of product management, Teledyne FLIR. “The combination of powerful edge computing and our Prism digital solutions ushers in a new era of electro-optical system capabilities while simplifying development and reducing integration risk.” Simplify and streamline development The AVP is designed to empower integrators to build powerful, edge-intelligent products. It is supported by several tools to simplify and streamline development including a Qualcomm RB5 development kit. Software and board-support packages are also available to enable developers to design and fabricate custom interface boards that meet each product’s specific form, fit, function, and input-output (IO) requirements.
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announces its plans for The Security Event, taking place at the NEC arena in Birmingham, from 30 April to 2 May 2024. Visitors will have the opportunity to visit Genetec at booth #5/H45 for an exclusive unveiling of Security Center SaaS, its new enterprise-grade, physical security as a service solution. It combines access control, video management, forensic search, intrusion monitoring, automation, and many other advanced security capabilities. This new offering, built with cybersecurity and privacy at its core, is a massively scalable, open and unified software-as-a-service (SaaS) solution. The Genetec team will be on-site to present the solution to visitors. Innovation at The Security Event The company will also be conducting live demonstrations of Security Center 5.12 “The physical security sector has been eagerly anticipating an enterprise-grade solution that can be implemented in the cloud or in a hybrid deployment. Security Center SaaS not only addresses this market gap but also redefines the possibilities for cloud-based physical security. We're thrilled to unveil this innovation at The Security Event, marking its debut in the UK market,” comments, Paul Dodds, Country Manager at Genetec Inc UK & Ireland. The company will also be conducting live demonstrations of Security Center 5.12 and other cutting-edge technological solutions designed to enhance security and operational efficiency. Agenda of experts from Genetec Additionally, Genetec will actively engage in the event's speaker program. Please find below the agenda of experts from Genetec, who will lead and present key topics sessions. Wednesday 1 May: 11:00 – 11:30, Kris Houle, Product Line Commercial Lead - Security Center SaaS, Genetec and Felix Camire, Product Marketing Specialist, Genetec - ‘Cloud technology and adaptation for UK businesses’ Thursday 2 May: 13:00 – 13:30, Jon Hill, Account Executive, Genetec - ‘Public sector safety with unified solutions.’


Expert commentary
Amidst the challenges of a prevailing economic downturn, the retail sector finds itself grappling with an unparalleled rise in incidents of shoplifting, theft, and burglaries. The disconcerting scenes witnessed on London’s Oxford Street in August 2023, where crowds gathered, looting as many stores as possible, sent shockwaves across the nation’s retailers. This alarming surge in retail crime has put retailers on high alert, as they contend with a rising tide of security concerns. Shoplifting concerns Recent data from the Union of Shop Distributive and Allied Workers (USDAW), has raised alarming concerns: shoplifting rates have surged by an unprecedented 24%. In the first half of 2023 alone, there were approximately 8 million reported shoplifting incidents. With the ongoing burden of the cost of living crisis and the approaching festive season, it is expected that these figures will keep surging. Implementing robust security measures Theft and prevention strategies cost retailers approximately £2 billion in 2021/2022 While more help from the Government to support retail workers and the businesses shoplifters target is certainly needed, the implementation of robust security measures will significantly contribute to deterring these crimes from occurring in the first place. British retailers spend millions on tools to deter and catch shoplifters inside stores, from CCTV and security guards to electronic tagging and alarms. The Grocer reported that theft and prevention strategies cost retailers approximately £2 billion in 2021/2022. Despite these initial costs, other threats are at play beyond the shop floor. Break-ins by criminal gangs For many large town center stores and supermarkets, and units in retail parks, the rear doors and delivery areas are commonly targeted by criminal gangs. It’s not uncommon for thefts to occur from pallets or cages that have been unloaded from lorries and sit waiting to be moved into the building. After-hours break-ins are a risk for all store owners too, particularly over the festive season when a lot of high-value stock has been delivered to shops and supermarkets. Addressing anti-social behaviour The additional fencing was deemed an essential measure to safeguard the community Anti-social behavior also poses a challenge for retailers. In 2022, an Aldi based in Derby invested in security fencing to protect staff and deter loitering groups. The additional fencing was deemed an essential measure to safeguard the community, as dangerous items were frequently found outside the store, including weapons and hypodermic needles. So how do physical security solutions such as fencing and gates help better protect retail establishments such as supermarkets and edge-of-town retail park shops? Fencing and gates: a critical component of retail security 1. Risk assessment and target hardening A thorough risk assessment will identify potential weak spots that require protection. ‘Target hardening’ involves implementing physical security measures that become more robust as they approach the target. This helps deter intruders while ensuring ease of access for customers and staff. 2. Effective perimeter security Opt for difficult-to-climb security fencing that provides a robust obstacle against thieves, vandals, and intruders Selecting fencing solutions according to the potential threats, site characteristics, and topography is crucial. It is important to specify fencing that strikes a balance and maintains a welcoming appearance while safeguarding external areas of the store or warehouse from potential harm and unauthorized access. Solid fencing which provides concealment can help to conceal expensive goods and remove them as a target for opportunistic theft. Opt for difficult-to-climb security fencing that provides a robust obstacle against thieves, vandals, and intruders. I recommend selecting a sufficiently tall and robust fence such as an acoustic barrier. Its noise-reducing properties are often beneficial for these types of sites too. 3. Controlling vehicular speeds and access To enhance security, consider controlling vehicular speeds and access. One effective approach is the installation of bollards at the ends of traditional high streets. This practice is already commonplace as a means of safeguarding against hostile vehicle attacks, but it can also play a pivotal role in preventing quick getaways of vehicles involved in potential heists. Additionally, employing road blockers and sliding gates at the rear entrances of delivery areas would serve to fortify security further. These measures can help in delaying vehicles, allowing for necessary checks to be conducted. 4. Balancing security with aesthetics The presence of high-security fencing can also make a site more of a target for vandals and burglars Another challenge is avoiding creating an imposing presence, especially important for areas situated near residential communities. The presence of high-security fencing can also make a site more of a target for vandals and burglars. To minimize this risk consider specifying timber fencing and traffic barriers to secure car parks, providing both security and a welcoming atmosphere for shoppers. Taking an integrated approach Combine secure perimeter fencing with effective lighting in places with shaded areas and at doors, gates, and shop windows, alongside Perimeter Intrusion Detection Systems (PIDS), and strategically placed CCTV. These measures will hinder unauthorized entry and escape, increasing the likelihood of detection and apprehension. Prioritising employee wellbeing Installing robust security fencing, complemented by CCTV, good lighting, and guarding, creates a safe environment Installing robust security fencing, complemented by CCTV, good lighting, and guarding, creates a safe environment for employees. This not only safeguards their well-being but also provides peace of mind that they are protected effectively in the case of a burglary or crime. When selecting security products for retail sites, it is advisable to opt for items that have undergone rigorous testing and carry relevant certifications for their security level. Each component should meet industry-specific standards for its intended purpose and originate from manufacturers accredited under ISO 9001:2015. This ensures a high standard of quality and reliability in safeguarding the premises. High-quality security fencing As the cost-of-living crisis continues, crime rates increase, and the festive season approaches, the time to act and implement on-site security is now. By investing in comprehensive security measures, retailers can protect their assets, employees, and customers, ensuring a safer and more secure shopping environment for all. High-quality security fencing is also a sound investment, that requires little or no maintenance once installed. The best fencing solutions are extremely weather-resistant, and won’t suffer from rust or corrosion. With all sectors preparing to ride the rapids of recession in the coming year, improving on-site security while selecting cost-effective measures, is one surefire way to protect your people, your property, and your profits from harm.
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realize, however, that some of these traditional security measures are becoming antiquated and no longer cutting. The now and future of overnight security is in remote guarding. Pioneered by companies like Los Angeles-based Elite Interactive Solutions, which was founded back in 2007, remote guarding is revolutionizing the overnight security business. Minimizing criminal activity Remote guarding is fast becoming the most popular choice among commercial end-user property owners Remote guarding utilizes a combination of cutting-edge technology, “digital guards,” highly trained security agents, and local law enforcement if and when necessary to minimize the potential of criminal activity. For those adequately enlightened to its overwhelmingly impressive crime prevention capabilities, remote guarding is fast becoming the most popular choice among commercial end-user property owners to secure and protect their investments. What Is Remote Guarding? Remote guarding is a revolutionary concept and increasing trend in security systems that utilize a combination of methods to effectively analyze potential threats to property. Cameras and/or other monitoring devices running highly advanced algorithmic software are installed in strategic areas or vulnerable places onsite and remotely located security agents are immediately notified of any activity within a designated perimeter of the property. A blend of AI, cybersecurity, and video analytics When properly deployed by an expert provider, the technology stack includes a proprietary blend of video analytics, artificial intelligence, cybersecurity, and more. Done right, “noise” is effectively filtered out, allowing agents to act on legitimate alerts and achieve zero false alarms communicated to first responders. Today, there are a lot of terms and descriptions tossed around about remote guarding, remote video, virtual guarding, etc., but those attributes must be present to represent the true definition of the offering and its many virtues. Realtime situational awareness Many systems have a two-way speaker that allows the security agent to give a verbal warning When specially trained security agents are alerted to trespassers, possible intruders, or other suspicious activity, they analyze the situation in real time and determine the necessary level of action. Many systems have a two-way speaker that allows the security agent to give a verbal warning, known as a voice-down, to the individual(s) that they are being watched. Most perpetrators, often believing the response is emanating directly from security personnel on the property itself rather than from a remote command center, flee immediately. However, if the threat persists, the security agent enlists local law enforcement to get on the scene. Customized remote guarding When properly deployed, remote guarding systems are also customized to specific properties. A team of consultants visits the client’s property to evaluate its vulnerabilities and where to best place cameras and/or other monitoring devices for system efficacy. Traditional Security Shortfalls According to Keith Bushey, a retired commander for the Los Angeles Police Department, there is much frustration between law enforcement officers and potential victims of crime due to the historically unreliable performance of traditional burglar alarm systems and central monitoring stations. He states about 90% of security-related calls are false alarms, a problem that has been well-documented through the years. Onsite challenges When a legitimate emergency does occur, the perpetrators have often already done their damage When a legitimate emergency does occur, the perpetrators have often already done their damage and/or escaped by the time law enforcement arrives. Onsite security guards are not the remedy either as they bring their own set of issues and challenges. Unexpected costs Traditional security systems can also have unexpected costs. The cost is not only in the security guards’ paycheck or the cost of the equipment itself. The cost comes when an actual incident occurs. In worst-case scenarios, the security guard(s) are injured, the business suffers inventory loss, and/or damage is sustained to the property. The medical and other costs for the security guard(s), the loss of inventory, property damage, deployment of law enforcement resources, and possible fallout of legal expenses all add up. Even in the best-case scenario, false alarm expenses incur if law enforcement is dispatched. These, among many others, are some of the primary issues that remote guarding resoundingly answers as a superior alternative. A Bounty of Benefits Remote guarding systems have been proven to cut costs and be more effective than traditional security systems. Even though the monthly monitoring costs of remote guarding are significantly higher than traditional intrusion detection system monitoring, the much higher effectiveness in crime reduction, elimination of false alarms, and augmenting or replacement of manned guards result in a substantially higher return on investment (ROI) to the end user. Easy tracking of threats The security cameras already have their image captured on record, making them easier to track down For example, case studies have demonstrated reduced security costs for clients by 60%, on average. These reductions have come from the costs of security staff, inventory, or property loss, plus saving money on insurance premiums and deductibles. The nature of remote guarding reduces the risk and costs of false alarms, with professional security agents able to determine an actual threat before law enforcement is called. In a rare instance when a perpetrator escapes before law enforcement arrives or can detain the individual(s), the security cameras already have their image captured on record, making them easier to track down and identify. Reduction of false alarms The significant reduction in false alarms is greatly appreciated by law enforcement, as it allows them to focus on real emergencies or crises. Better relationships are also developed between clients and law enforcement, as remote guarding systems are highly reliable in providing accurate and real-time information to officers as they approach the scene. In short, it assists law enforcement in doing their job more effectively, as well as more safely thanks to having eyewitness information before engaging in an active crime scene. Partnership When you combine the decreased cost with the increased efficiency and success rate, it is easy to see why many commercial end-user property owners across the country are making the shift to remote guarding. It’s also an outstanding opportunity for professional security dealers and integrators to partner with a remote guarding services provider to bring a superior solution to their end customers and pick up a recurring monthly revenue stream in the process.
The autumn equinox, which marks the start of autumn, occurs this weekend on Saturday, September 23. With darker evenings ahead, the experts at ADT have shared five ways to maximize your home's security. Author's quote Michele Bennett, General Manager at ADT UK&I comments: “Opportunistic thieves use darkness to their advantage, so it’s no surprise that the number of burglaries committed increases when the darker nights draw in." He adds, "Our 2022 burglary report found that burglaries are most common at night, with 58% of burglaries occurring between 6 p.m. and 6 a.m. Taking steps to optimize your home’s security before the clocks go back this year will provide reassurance that your property is as secure as possible.” Five ways to secure your property: Get a monitored alarm installed: A visible alarm system is a strong deterrent to potential burglars, as criminals are less likely to target a home that is protected. In the event of a break-in, a monitored alarm will alert you, your keyholders and depending on the package you take out, the police, ensuring a swift response to an alarm activation. Light up the dark: Well-lit exteriors make your home less appealing to potential intruders. Install motion-activated lights around any entry points, particularly porches and gardens, which alert you to movement on your property. This will also prevent burglars from operating under the cloak of darkness and increase the chance of a passerby spotting suspicious activity. Trim your garden landscape: Thieves look for escape routes and hiding spots when deciding which homes to break into, making gardens with high, overgrown hedges more likely to be targeted. This is especially true in the darker evenings, so be sure to give your garden a thorough tidy-up to make your property less likely to be targeted. It’s also advisable to ensure any tools are locked away in sheds and garages that could assist a burglar such as ladders, or a garden spade to force entry. Be smart with your lights: Using smart plugs allows you to turn on a few well-appointed lights and radios or televisions from any location from your phone. Used in conjunction with an outdoor camera or video doorbell, you can have lamps plugged into smart plugs come on when motion is detected. Programming lights to come on at different times throughout the night will help to deter burglars by making your property look occupied. Purchase a smart doorbell or outdoor camera: Smart doorbells are an effective way to deter burglars as they provide evidence in the event of a break-in, package theft, or other suspicious activity around your home. They also notify you when someone is at your door reducing the chance of you being caught out by a late evening or early morning robbery. Further encroachment Smart doorbells also act as a deterrent to unscrupulous door-to-door sellers and con artists, as video footage is recorded. In the event of a late-night door knock, you can see and speak to whoever is at your front door, without having to open the door. ADT’s new outdoor camera also has two-way audio and a high-pitch deterrent siren so you can warn off anyone from your property to deter any further encroachment.
Security beat
ISC West 2024 mirrored a vibrant industry on the precipice of accelerated change. Factors such as the cloud, artificial intelligence (AI), edge computing, and biometrics are shaping the future of the security marketplace, and they were front-and-center at the industry’s biggest U.S. show in Las Vegas. Foot traffic was steady and impressive, including more than 29,000 security industry professionals viewing 750 exhibitors. A torrent of eager attendees crowded the lobby on the first day and could not wait for the doors to open. When they were admitted, the wealth of technological innovation and business opportunity did not disappoint. Focus on cloud systems Cloud systems were high-profile at ISC West. Camera manufacturer Axis, for example, introduced their Axis Cloud Connect at a press conference. Meanwhile, Genetec officially launched their Security Center SaaS platform, which aims at eliminating points of friction to enable integrators to easily embrace cloud systems from quoting and ordering to provisioning and installing. Camera manufacturer Axis, for example, introduced their Axis Cloud Connect at a press conference Cloud provider Eagle Eye Networks promoted their new “Eagle Eye 911 Camera Sharing” technology under which both non-Eagle Eye Cloud VMS customers (via Eagle Eye 911 Public Safety Camera Sharing) and Eagle Eye customers can opt to share their video feeds for use by 911 operators in case of emergency. If users opt-in, 911 operators can have access to live video as an emergency unfolds. Eagle Eye Networks provides the feature by integrating with RapidSOS call center software. Camera locations are based on geolocation coordinates, and customers can choose if they want to participate and which cameras they want to share. Biometrics in the mainstream Biometrics were well represented at ISC West, including Alcatraz AI, which introduced an outdoor version of their biometric face recognition product. The Rock X works well despite harsh lighting. Alcatraz’s products do not have to be integrated, they communicate just like a card reader using OSDP or Wiegand protocol. “At the show, customers are excited about moving to a frictionless environment and getting rid of existing credentialing,” said Tina D’Agostin, CEO and co-founder of Alcatraz. “We are making access control frictionless, secure and private. The experience can be as passive as possible – people can just walk in.” Multiple types of authentication, and the ability to detect tailgating and stream video SAFR from Real Networks also featured biometric face recognition, emphasizing feature sets, convenience, and price/performance. They offer multiple types of authentication, and the ability to detect tailgating and stream video. A new device is a small mullion mount that is “approaching the price of a card reader, factoring in the need to purchase cards,” said Brad Donaldson, Vice President and General Manager. SAFR focuses on convenience: You don’t have to take out your phone to pass through a door. Enrollment is easy by incorporating existing databases, and costs are lower than competitors, said Donaldson. The system analyses multiple points on the face, turns it into data and then encrypts it, providing a “unique signature for each person.” Credentials in Apple Wallet and Google Wallet AMAG Technology announced the compatibility of credentials with the Apple Wallet and Google Wallet. The company is also embracing a new strategic direction under President David Sullivan. They launched a new website in January, are developing dynamic resources and a partner page, and they now integrate with 120 tech partners. AMAG Technology Financial Services now enables their channel partners to offer leasing and financing options to customers. The big new booth at ISC West reflected an effort to “market different and look different,” according to the company. The big new booth at ISC West reflected an effort to “market different and look different" The new Symmetry Control Room, a command-and-control system, is a relaunch of an earlier AMAG product with enhanced features. Suitable for large enterprise customers, the software enables a big video wall to display all the various systems and incorporates all the data into a single “pane of glass.” Operators can “draw a lasso” around cameras they want to display on the video wall and can follow action across multiple camera feeds. Navigating megatrends A breakfast meeting for integrators, sponsored by Assa Abloy Opening Solutions, was built around the theme “Navigating Megatrends for Sustainable Growth." The megatrends are artificial intelligence, sustainability and cybersecurity. Related to cybersecurity, there are 350 common vulnerabilities and exposures (CVE) published per week, reflecting the continuing threat to cybersecurity. Physical security has a “data lake” of information from various physical security systems that can be an attractive target for cybersecurity breaches. Data sets can be exploited and/or poisoned. The security industry needs to apply “defense in depth” to the challenges of protecting data. “The threat landscape is always changing, and security technology is an iterative process,” said Antoinette King, i-PRO’s head of cyber convergence, one of the panelists. Natural language systems Natural language systems are a newer approach making an early appearance at ISC West Natural language systems are a newer approach making an early appearance at ISC West. Brivo, for example, has an early prototype of its “natural language search capabilities” that can answer questions such as “Who is in the office?” or “Where is Bob and what has he done?” Brivo also promoted its all-in-one door station device that combines a card reader and a camera (for facial authentication) and serves as a video intercom, thus eliminating the need for multiple devices at the door. Brivo is also emphasizing tailgate prevention, facial authentication, and people counting using AI at the edge. Also promoting natural language systems was Verkada, which unveiled a beta version of its AI Search feature that embraces national language capabilities. With AI Search, users will soon be able to use natural language to search for people or items. For example, a search could be “person climbing over a fence” or “person making phone call” or “person wearing football jersey.” Verkada wants to be thoughtful with the rollout and make sure effective guardrails are implemented to prevent abuse and bias. The release should happen in the coming months. Multi-family applications Allegion is promoting the XE360 hardware lock platform in various formats, including cylindrical lock, mortise lock, deadbolt, and exit trim. At the show, Allegion noted an enthusiasm for multi-family applications. “We have been surprised by the people who want to add electronics and to retrofit existing multi-family facilities to compete with newer facilities,” said Henry “Butch” Holland, Allegion’s Regional Director, Channel Sales East Region. Allegion works with 60 different physical access control software providers, including familiar players such as LenelS2 and Genetec Allegion also offers an “indicator” display on its locks, showing at a glance whether a door is locked or unlocked. The “indicator” might also display “occupied” or “vacant.” Allegion works with 60 different physical access control software providers, including familiar players such as LenelS2 and Genetec. Integrator M&A trends Everon looks for acquisitions in areas where they do not currently have support for national accounts A conversation with Everon at ISC West provided insights into the accelerating trend of mergers and acquisitions among the integrator community. Everon, formerly ADT Commercial, has done six acquisitions of local integrators since they changed their name last year. In targeting companies to acquire, they look for a good company with a good reputation, and they consider how the new company’s competencies complement their own. Some M&A strategy is geographic, as Everon looks for acquisitions in areas where they do not currently have support for national accounts. They also consider density, seeking to add new acquisitions in larger markets where they don’t currently have a big market share. “A lot of investment is coming into security because it is seen by investors as recession-proof,” said Michael Kennedy, VP, Mergers and Acquisitions, for Everon. Kennedy met with 95 businesses last year for possible acquisition, and the company only finalized a handful – reflecting that Everon is selective and careful that corporate cultures are aligned. “With an acquisition, the goal is to keep every customer and every employee,” said Kennedy. Voice of the customer ISC West provides an opportunity for manufacturers to listen to the “voice of the customer;” in person, no less. “We have every kind of problem come to the booth,” commented Heather Torrey, Honeywell’s General Manager, Commercial Security, Americas. “People are passionate, interested and very specific with their questions and comments,” she said. “We are driving a complete system, but we are flexible, helping our customers to meet their needs and not try to fit every foot into the same shoe. Sometimes meeting customer needs involves working with competitors," Torrey commented. “It truly comes back to listening to the customer, not just ‘this is what we have to offer,’” she adds. ISC West provides an opportunity for manufacturers to listen to the “voice of the customer;” in person, no less. Edge applications are everywhere at ISC West, and one company is promoting a new approach to expand functionality at the edge. Camera company i-PRO advocates the use of the “Docker” platform for app development, an option they offer on their cameras. Docker “containers” package deep-learning algorithms to make it easier to embed software into edge devices. Anyone can run Docker apps on i-PRO cameras that use the powerful Ambarella chip. A Docker “swarm” can combine multiple edge devices to work together and share resources. For example, the approach can increase computing power at the edge to increase the capabilities of instant analytics. It’s faster and provides better redundancies. A “distributed computing platform” ensures less latency than communicating analytics to a central server. Unification of capabilities Johnson Controls (JCI) also promotes the trend of combining multiple systems into a single pane of glass. Their “Open Blue” platform, with a security version unveiled at the show, integrates various security systems into one, combining data and monitoring device health. Basically, the system manages all resources holistically. JCI also notes a trend toward “unification of capabilities,” e.g., combining access control and video. “The scope of security is evolving from a focus on protection to a broader focus on operations,” commented Julie M. Brandt, JCI’s President, Building Solutions North America.
As the physical security and cybersecurity worlds converge, many industry professionals are finding themselves moving from one realm to the other. Or, more likely, they are embracing both disciplines as integral to the future of security as a whole. One security professional bringing her cybersecurity expertise to the physical security market is Wendy Hoey, Director of Sales, US Sales Leadership, North America, for Milestone Systems. With more than 23 years of experience in cybersecurity, Wendy Hoey now works with a global company dedicated to empowering people, businesses and societies with data-driven video technology. Author's quote Caught up with Wendy Hoey to discuss how the security market can harness innovation “I'm thrilled to be joining the physical security industry at this transformative time when there's such tremendous potential to update legacy systems with pioneering technologies like AI and the Internet of Things,” says Hoey. “I'm energized by the chance to collaborate with colleagues to help transform physical security, enhance predictive capabilities, and realize a shared vision of seamless protection across the digital and physical realms.” Caught up with Wendy Hoey to discuss how the security market can harness innovation to make the world safer and more secure. “The future is bright, and I'm honored to be part of this community,” says Hoey. Q: What can physical security learn from the world of cybersecurity? Hoey: Physical security can learn a great deal from the world of cybersecurity. With the rise of IoT and IP-connected devices, the lines between physical and digital security are blurring. Like cybersecurity, physical security needs to take a proactive approach to protecting core systems and perimeter access points. Understanding potential vulnerabilities and attacks is key. Physical security pros should continuously educate themselves on emerging technologies and threats and stay up to date on best practices. Adopting a customer-centric mindset is also critical. Rather than just selling technologies, physical security providers should focus on understanding clients' unique risks, objectives, and pain points. By taking cues from cybersecurity, the physical security industry can transform itself, innovate, and provide smarter solutions. Q: How is physical security a unique application for IT? How do physical security (and/or video) systems differ from “other” IT systems? Hoey: Physical security has unique challenges compared to traditional IT systems, but also shares some commonalities. At its core, physical security relies on networked hardware like cameras, access control and detectors that must be online and recording effectively at all times. This is like IT infrastructure in that uptime and availability are critical. With the rise of IoT, cyber and physical security are converging. Physical security systems have vulnerabilities that didn't exist before everything became IP-connected. Staying on top of emerging technologies and threats is crucial. At the end of the day, both physical and cyber security share the goal of minimizing organizational risk, and both disciplines must come together and cooperate to optimize security and safety. Q: How can security integrators ensure their workforce (i.e., installers) have the required IT skills to address the needs of the physical security market? Hoey: As security networks converge more deeply with IT infrastructure, integrators must invest in training to ensure their installers have the required skills. Whether pursuing vendor certifications, in-house training programs, or partnerships with IT services firms, integrators must recognize that security solutions require IT fluency. A willingness to upskill installers and keep pace with technological change will prepare integrators to deliver the solutions end users demand in an increasingly connected physical security ecosystem. Q: What is the role of the manufacturer to ease the application of IT technologies to the physical security market? Hoey: The role of the security manufacturer is to simplify and facilitate the application of IT technologies by serving as a trusted advisor and educator. Manufacturers must provide guidance, case studies, and domain expertise to help partners and end users understand the full capabilities of technologies and how they can be leveraged most effectively. Rather than just promoting a specific product, manufacturers should always take an active role in informing the channel and customers on available possibilities, bringing real partnership through tailored advice and solutions. Q: What challenges remain relating to implementing IT technologies in the physical security industry? How will new technologies (e.g., AI) transform the IT environment for physical security now and in the future? Hoey: When implemented thoughtfully, AI has enormous potential to transform physical security by helping security professionals identify anomalies and patterns in data to enable predictive analytics. With the right solutions, AI can act as a force multiplier by monitoring behaviors and giving security teams advance warnings before incidents occur. As AI and other emerging technologies mature, they will bring the industry in line with the most advanced security tools available. The future looks bright for a truly integrated physical and digital security environment with AI pioneering the charge.
Companies at GSX 2023 emphasized new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasizes ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the Mid-Market to the Cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for pure cloud, but there are benefits to be realized from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realize the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘Soft’ Features for Integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organization more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organization more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centers around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasizing performance, protection (cybersecurity), and price, their data centers are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring center where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
Case studies
The University of California San Diego (UCSD) Police Department is a full-fledged law enforcement agency responsible for patrolling, investigating, and preventing crime within its jurisdiction. Spanning over 1,200 acres and comprising 900 buildings, UCSD’s campus presents unique challenges for law enforcement. The department’s Communications Division serves as the nerve center, coordinating responses to emergencies, managing communications, and ensuring coordination among officers. Garrett Williams, a seasoned Sergeant at the University of California San Diego (UCSD) Police Department, oversees the Communications Division. With over two decades of experience, Williams understands the critical role technology can play in public safety. The challenge Before partnering with RGB Spectrum, UCSD faced significant obstacles in its dispatch operations Before partnering with RGB Spectrum, UCSD faced significant obstacles in its dispatch operations. Dispatchers juggled multiple computers, including a CAD, radio, and phone computer, each requiring separate keyboards and mice. “I didn’t look to RGB to solve all my problems. However, I understood all that could be accomplished once the team showed us how the technology operated and what was possible,” Garrett Williams, Sergeant, University of California San Diego Police Department. “Three separate mice and operators constantly moving side to side to look from one to the other and then having to move their hands back and forth between control devices - anytime they have to do that, it’s slowing their workflow down; we figured there had to be a better solution,” shared Williams. “And up to 25% of our operators were suffering from repetitive movement and neck Injuries, resulting in downtime and light duty restrictions.” Why UCSD chose XtendPoint KVM-over-IP UCSD wanted a seamless KVM solution that integrated multiple systems over IP under a unified interface. It explored various options before discovering RGB Spectrum’s XtendPoint™ solution, which provides local and remote access to source computers, consolidates separate monitors into multi-view displays, and unifies control for more streamlined operation and enhanced efficiency. With RGB’s XtendPoint KVM system, UCSD grew access to the fire alarm system at each operator’s station UCSD’s key selling point was its ergonomic benefits. It offered a solution to the ergonomic challenges plaguing dispatchers by minimizing the need for multiple keyboards and mice. So did replacing monitor clutter. With the XtendPoint solution, single-signal monitors are consolidated on each console using multiview displays that can handle up to four computer signals each or up to eight signals displayed on just two pieces of glass. A notable feature of this solution is the ability to offer each operator customized display viewing, even in a multi-shift operation. A KVM-over-IP backbone offers additional benefits. Before, only one dispatcher station could see the fire alarm system. With RGB’s XtendPoint KVM system, UCSD expanded access to the fire alarm system at each operator’s station. Now, no matter where dispatchers are seated, they have access to all needed systems. How UCSD uses RGB’s solution The RGB Spectrum solution marked a significant turning point for UCSD’s dispatch operations. Dispatchers experienced a dramatic improvement in efficiency, ergonomics, and situational awareness. Gone are the days of dispatchers juggling multiple control devices. With a unified interface, dispatchers can control all systems from a single keyboard and mouse. A streamlined workflow accelerated response times and reduced errors. Video integration proved invaluable. Dispatchers can now access live video feeds and additional mission-critical systems directly within one system interface, providing them with real-time visual information as required. With a unified interface, dispatchers can control all systems from a single keyboard and mouse Additionally, support for video integration with a video wall provided opportunities for enhanced collaboration and situational awareness. Commented Williams, “The flexibility of the RGB system also allowed UCSD dispatchers to leverage video wall capabilities. They can easily share critical information and task lists with colleagues. A more collaborative environment has facilitated communication and coordination among dispatchers, ensuring that tasks are efficiently managed and prioritized during high-stress situations. We can use the RGB system to throw things up on the wall so other dispatchers can see what’s happening and interact as needed.” “In addition," said Williams, “the resilience of the RGB XtendPoint system is invaluable in maintaining operational continuity. For example, in the event of a problem at a station, technicians can work on the issue while the dispatcher moves to a backup computer or station, allowing dispatchers to continue critical work without interruption. This proactive approach to system maintainability and resilience saves time and resources and ensures that dispatch operations remain fully functional at all times.” The result The impact of XtendPoint KVM-over-IP on UCSD’s dispatch operations has been profound. UCSD witnessed significant improvements in efficiency, ergonomics, and situational awareness. Efficiency soared as dispatchers seamlessly controlled multiple systems from a single interface. Ergonomic issues were mitigated, and dispatcher morale improved, enabling dispatchers to respond more effectively to emergencies. Future plans with RGB Spectrum Williams is enthusiastic about the wraparound monitors RGB has announced Looking ahead, UCSD sees opportunities to leverage RGB Spectrum’s technology further to enhance operations. RGB system’s versatility also enables UCSD to adapt to evolving threats and emergencies. In the event of, say, a building evacuation or siege, for example, UCSD could almost immediately establish a satellite facility. Williams is enthusiastic about the wraparound monitors RGB has announced. “We are looking at RGB’s new, yet to come to market, 43-inch curved monitors that will be the finishing touch for even better ergonomics and a customized workspace.” Another potential interest is a “flyaway” kit, a transportable command-and-control system with integral radio access. This mobile system would enable UCSD to monitor special events, such as festivals, where real-time situational awareness is crucial for ensuring the safety of attendees and staff. Williams notes, “We can have a mobile command post set up near a festival or special event, take one of our dispatch systems and put it there without having to move a lot of equipment or figuring out how to get it on the network.” Implementing RGB Spectrum’s solutions UCSD also aims to extend the reach of its dispatch operations by providing in-the-field personnel with access to real-time information. By equipping mobile units with RGB’s AV-over-IP systems via smartphones, police officers could receive critical updates and better collaborate with dispatchers to respond to incidents. “If you think of the unthinkable, like a school shooting, it would be ideal to share live coverage of what’s happening, detailed building schematics, and info on weapons the assailant might be using. Who doesn’t want to know what’s potentially happening behind closed doors before walking in? It’s situational awareness on a whole new level,” commented Williams. The partnership between the UCSD Police Department and RGB Spectrum has proven successful. By implementing RGB Spectrum’s solutions, UCSD transformed its dispatch operations to achieve unprecedented levels of efficiency, ergonomics, and situational awareness. And it is just a start.
Completed in 2023, Thanet Parkway Station, the new high-speed rail hub serving the Thanet area in southeast Kent, has implemented a significant infrastructure enhancement: the installation of high-quality parking barriers to optimize accessibility and safety within its premises. Investment in connectivity Thanet Parkway Station, which opened on 31st July 2023, is a testament to the region's commitment to advancing its transportation infrastructure. With a total investment of £44 million secured through a combination of council financing and various building and growth funds, the station addresses the rising demand for efficient connectivity to London and neighboring towns. Swift and convenient travel Furthermore, its ample car park, boasting space for 293 vehicles, serves as an indispensable "park and ride" facility Featuring two expansive platforms capable of accommodating 12-car trains and strategically situated on the high-speed line through Ashford International, Thanet Parkway Station offers commuters swift journeys to key destinations. Furthermore, its ample car park, boasting space for 293 vehicles, serves as an indispensable "park and ride" facility, alleviating congestion in central Thanet and providing convenient access to the surrounding areas. Enhancing safety and traffic flow To enhance safety and streamline traffic flow within the station's car park and adjoining pedestrian and cycleway, Jacksons Fencing was specified to implement a comprehensive suite of parking barriers and demarcation measures. Warden Swing Barriers were installed along the pedestrian and cycleway to regulate vehicular access. These galvanized steel barriers offer a robust solution while ensuring ease of operation for maintenance and emergency vehicles. Safeguarding pedestrian pathways Along the same path, Jacksons Fencing’s timber knee rail fencing served as an unobtrusive demarcation device. This fencing solution, constructed from kiln-dried, pressure-treated timber and galvanized steel straps, safeguards grass verges and delineates pedestrian pathways. Ensuring peace of mind Strategically positioned to enforce height restrictions within designated parking areas, Jacksons’ MaxHite parking height restriction barriers were installed. Crafted from galvanized steel and finished in a highly visible yellow polyester powder coating, the barriers provide durable protection against unauthorized access, while facilitating smooth traffic management. Each installed product comes with the assurance of Jacksons Fencing’s 25-year guarantee, symbolizing a commitment to quality and sustainability. High-quality, sustainable products Commenting on the project, Peter Jackson, Managing Director of Jacksons Fencing, underscored the transformative impact of the enhanced security measures at Thanet Parkway Station, said "As a local supplier, we’re thrilled to have been involved in this project, and it’s great to see that the developers have invested in high-quality, sustainable products, showcasing this project’s commitment to providing a lasting transport solution for the community." He adds, "Beyond parking, the upgraded access control and increased security measures not only enhance safety, but also foster a profound sense of reassurance and pride in the area for all station users."
Wetlands, the "kidneys of the Earth", are considered one of the three major ecosystems on Earth, along with forests and oceans. Hosting a diverse range of terrestrial and aquatic plant and animal species, wetlands serve as crucial habitats for numerous bird species. Red-crowned cranes Beautiful Wetlands vs Critically Endangered Cranes The Red-crowned Crane is considered as the "God of Wetlands" and is highly sensitive to environmental changes. It is one of 14 bird species in China classified as critically endangered, with only around 2,000 wild Red-crowned Cranes remaining worldwide. Monitoring these rare bird species not only aids in their effective protection but also reflects changes in the wetland ecosystem to some extent. Red-crowned Cranes migrate between the regions of East China and Northeast China In China, during spring and autumn seasons, Red-crowned Cranes migrate between the regions of East China and Northeast China, requiring wetland management personnel to make all necessary preparations in advance every year. Recording and tracking data (e.g. time of arrival/departure, and total number) play a significant role in monitoring both the Red-crowned Cranes and the wetland ecosystem. Hence, monitoring rare bird species is essential not only for their conservation but also for understanding the changes in wetland ecological environments. Vigilant cranes, eager for improved, smarter observation However, Red-crowned Cranes have extremely strong vigilance. Even while foraging or resting, there are often adult birds designated to be on alert, making warning calls and taking flight if any danger is detected. Therefore, it becomes challenging for monitoring personnel to observe them up close, as they need to maintain a distance of several hundred meters using binoculars to avoid disturbing the cranes. Such limitations in observation pose difficulties in monitoring the population distribution and activities of Red-crowned Cranes. To achieve efficient and intelligent monitoring while minimizing human interference, many wetlands have enlisted the assistance of an intelligent "avian expert". Dahua: the guardian of cranes with smart technologies In recent years, avian intelligent recognition systems have been increasingly applied in wetland monitoring. Dahua Technology actively explores the integration of technology and wetland conservation to support the monitoring and protection of bird species across multiple wetlands. Rare bird species like the Red-crowned Crane can be automatically identified and counted By employing high-point video footage combined with avian intelligent recognition algorithms, rare bird species like the Red-crowned Crane can be automatically identified and counted. This allows monitoring personnel to discover and observe various bird species clearly and promptly without disturbing them. Additionally, techniques such as background removal and contour deformation processing help reduce the interference caused by lighting conditions and backgrounds, ensuring that the footage presents the identifying characteristics, location, and time for each bird. With this approach, comprehensive and accurate data recording and result analysis can be achieved without disturbing the Red-crowned Cranes up close. A brighter future for biodiversity using intelligent analysis In addition to population counting, vocalizations play a crucial role in bird research. By utilizing voiceprint recognition, it becomes possible to track and study the population distribution of rare bird species. Many regions have established and improved databases of avian vocalizations, creating a foundation for biodiversity monitoring and analysis. These databases, combined with visual identification, are being cataloged in order to facilitate more comprehensive research and analysis, optimize timely conservation measures, and enhance dynamic and diverse science communication and education. Dahua Technology continues to empower biodiversity conservation through technology. The Dahua AI platform enables continuous algorithm training that helps reduce the development cycle of recognition algorithms for specific species. At present, Dahua has developed over 800 bird recognition algorithms, with more than 500 focused on waterfowl and migratory birds primarily inhabiting wetland environments. This extensive collection of algorithms greatly supports and contributes to biodiversity conservation efforts around the globe.
Biometrics company, Fingerprint Cards AB (Fingerprints™), has upgraded the physical access security of its Gothenburg HQ. S-Key biometric access cards from Freevolt Technologies Limited, which embed Fingerprints’ own T2 sensors, have been implemented across the entire Gothenburg site. The updated authentication system further strengthens Fingerprints’ workplace security and enables role-based access control, while ensuring a convenient and easy-to-use experience. Role-based access control Fingerprints’ Gothenburg HQ has security gates to enter and exit the building, and restricted areas for hardware and software R&D. By replacing access keyfobs with biometrics access cards, site-wide security has been enhanced and role-based access control has been enabled to better control access to sensitive areas of the site. By replacing traditional security methods based on something they know/have with something they are, multi-factor authentication has been enabled while maintaining convenience for employees. Fingerprints’ latest ‘T2’ sensors Solution eliminates the security risk of lost or stolen cards, without adding infrastructure costs Caroline Krüger, CHRO of Fingerprints comments: “The workplace has evolved significantly in recent years. At Fingerprints, we offer hybrid working while still ensuring our workforce has 24/7 access to HQ. Amidst this dynamic working environment, it is essential our team feels the workplace is accessible and safe. This requires a flexible, secure, and convenient access control solution.” Fingerprints has implemented Freevolt’s flagship biometric access card solution, S-Key. The solution eliminates the security risk of lost or stolen cards, without adding infrastructure costs. The card incorporates Fingerprints’ latest ‘T2’ sensors which deliver optimized image quality, processing speed, and power efficiency. Traditional security methods Adam Philpott, CEO of Fingerprints comments: “To meet today’s security challenges we must move away from traditional security methods. And, as a biometrics company, it is important that we lead the way in ensuring robust, frictionless security in our own operations." "There is an opportunity here too; what can we learn, what innovations will we identify by using these systems day to day? I look forward to continuing our strong and innovative collaboration with Freevolt technologies.” Energy harvesting technology Gonzalo de Gisbert, Head of Product & Business Development at Freevolt Technologies, adds: “Fingerprints are pioneers in biometrics, with sensors in billions of products, so they know what makes a good biometric solution. We’re therefore thrilled that Fingerprints has chosen S-Key to strengthen security at their global headquarters, in Gothenburg." "Our pioneering radio frequency energy harvesting technology combined with Fingerprints’ ‘T2’ sensors, known as FPC 1323, enables S-Key to be completely battery-less, lasting for many years. Roll-out was seamless, with everyone set up in less than 1 hour. That’s simple, safe, and secure biometrics, powered by Freevolt.”
The institute encountered significant challenges stemming from the absence of CCTV cameras and a video management system. This jeopardized patient and staff safety, impeded equipment protection, compromised data integrity in research, posed regulatory compliance risks, and heightened liability concerns in the absence of visual records for verification. Further, the client faced a significant challenge in efficiently managing attendance for staff working in multiple shifts. With an extensive workforce, manual tracking became cumbersome, leading to operational inefficiencies. To address this issue, the client sought a solution to streamline attendance management while ensuring accuracy and convenience for employees. Challenges Patient and Staff Safety Concerns: The absence of CCTV cameras hindered staff and patient safety. This also led to delays in assistance or emergencies going unnoticed. Equipment Protection: The absence of a video management system made it difficult to monitor and protect expensive research machinery and medical equipment from damage, theft, or misuse. Data Integrity Concerns: Lack of surveillance compromised the integrity of research data, as there were no visual records of experiments or laboratory procedures. Regulatory Compliance Challenges: The institute faced regulatory compliance hurdles, including data security, patient safety, and privacy standards, risking penalties or sanctions due to inadequate surveillance measures. Liability Risks: The absence of surveillance could increase the hospital's liability in case of accidents or incidents, as there would be no visual records to verify events or actions taken. Lack of Efficient Attendance System: The absence of a streamlined system for attendance management created operational challenges, making it difficult to maintain accurate and up-to-date attendance records. Challenges with Diverse Shifts: Managing a workforce with diverse shift patterns posed specific challenges, requiring a tailored solution to address the complexities associated with varying work schedules. The client also needed help in effectively monitoring the attendance of staff members working in multiple shifts, pioneering to operational inefficiencies. Need for Facial Recognition: The client sought a solution that utilized face recognition as a credential for attendance marking, emphasizing the need for a secure and convenient method to track staff attendance. Solution This ensured continuous monitoring of patient and staff activities and adherence to protocols A total of 200 Matrix 5MP Dome Cameras with audio support were strategically installed indoors at the institute, covering patient wards, operation theaters, reception areas, treatment rooms, waiting areas, administrative offices, and laboratories. This ensured continuous monitoring of patient and staff activities and adherence to protocols. Outdoors, 200 Matrix 5MP Bullet Cameras were deployed at entrances, exits, parking lots, outdoor pathways, emergency exits, and long corridors. This enhanced perimeter security, and monitored visitor and vehicle traffic. Centralized video surveillance of all the cameras was achieved with Matrix SATATYA SAMAS - Video Management Software, along with four CAM100 licenses for seamless integration and control of all 400 cameras. The institute opted for a USER3 license which allowed three users to efficiently manage live feeds, review footage, and perform critical tasks from a centralized location. Furthermore, in the realm of time attendance, the absence of an efficient attendance system led to operational challenges, prompting the adoption of a server-based solution with automated reporting capabilities and centralized data storage. Managing a diverse workforce with varying shift patterns was tackled through a tailored workforce management system with scheduling capabilities. Matrix Time-Attendance system was implemented for real-time monitoring and reporting The client faced challenges in monitoring staff attendance, particularly for those in multiple shifts, causing operational inefficiencies. To address this, the Matrix Time-Attendance system was implemented for real-time monitoring and reporting across diverse schedules. A labor-intensive process of manually tracking attendance for varied shifts was streamlined through a comprehensive Attendance Management System, reducing manual efforts and enhancing overall efficiency. Recognizing the importance of secure and convenient attendance tracking, the client implemented a Facial Recognition Attendance System with 25 Nos of Matrix COSEC ARGO FACE, integrating biometric technology for enhanced accuracy and security. This fulfilled the client's need for a secure method of attendance marking, successfully addressing specific challenges and optimizing overall workforce management. Products Offered SATATYA SAMAS PLT: Enterprise Video Management Software SATATYA SAMAS CAM100 (4 Nos.): License for Adding 100 Additional Cameras SATATYA SAMAS USER03 (1No.): 3 Concurrent User License for Smart Client and Mobile Client SATATYA CIBR50MVL12CWP (200 Nos.): 5MP IR Bullet Camera Motorized Varifocal 2.8-12mm Lens With Audio SATATYA CIDR50MVL12CWP (200 Nos.): 5MP IR Dome Camera Motorized Varifocal 2.8-12mm Lens With Audio Matrix VMS Dongle: USB Dongle to Run Matrix SATATYA SAMAS COSEC CENTRA PLT1000 (3 Nos.): Platform-based User License COSEC CENTRA FR 1000 (3 Nos.): Face Recognition User License COSEC CENTRA TAM 1000 (3 Nos.): Time-Attendance User License COSEC ARGO FACEE (25 Nos.): Instant Face-based Door Controller Benefits The Cameras with Motorized Varifocal Lens enabled the ability to remotely adjust focal length and zoom, allowing the capture of detailed images over varying distances in the institute. With the help of user-defined roles and rights, administrator, operator, and viewer rights were given which enhanced security, as only designated officials could access the footage. The E-map monitoring feature in SAMAS allowed the users to navigate between various buildings, floors, and cameras, facilitating easy centralized video surveillance throughout the campus premises. Camera Grouping, Page Sequencing, and Window Sequencing in SAMAS made it very easy to manage such a large number of cameras. The Interactive Smart Client in SAMAS allowed for Quick Investigation. Video Footage could be easily bookmarked, and exported as required. Reduced manual efforts with a comprehensive Attendance Management System leveraging advanced software. Enhanced operational efficiency through automated attendance tracking for diverse shift schedules. Streamlined data collection and reporting, improving overall efficiency in attendance management. Improved accuracy, reliability, and security in attendance tracking with Face Recognition based biometric technology.
Delta Scientific, the pioneering manufacturer of counter-terrorist vehicle control systems used globally, announced that on Monday, April 1st, a DSC501 High-Security Barricade stopped an unauthorized vehicle from entering an FBI field facility in Atlanta, Georgia. According to officials, the orange Buick Encore tried to follow an FBI employee’s car into the facility before being stopped by the Delta DSC501 barrier. The driver was then apprehended by special agents who were in the immediate area. Strength and reliability of Delta “Delta has a long history of thwarting attempts by unauthorized vehicles trying to enter facilities where they could potentially cause serious harm to civilians and structures,” states Greg Hamm, Delta Vice President of Sales and Marketing. “We are extremely proud to celebrate our 50th anniversary this year protecting the world’s most important institutions. The strength and reliability of Delta barriers is unrivaled.” FBI field office On June 27th, 2006, the DSC501 was tested to the most extreme parameters on record The DSC501’s protecting the FBI field office are the strongest in the world. On June 27th, 2006, the DSC501 was tested to the most extreme parameters on record. A 65,120-pound dump truck hit the DSC501 at 50mph and was stopped at the barrier. At the time of the test, this would have roughly equated to a K54 rating with the crash energy equaling 54,000,000 foot-pounds. ASTM M50 testing level How impressive is this? The current highest ASTM M50 testing level requires 12,500,000 foot-pounds of energy when impacting the barrier. This is a factor of over 4x which is extremely impressive considering the magnitude of the current M50 test. Contact Delta Scientific if they want to make sure the facility has the strongest, most reliable barriers on the market. They are celebrating 50 years in business in 2024.


Round table discussion
There is a complex and interdependent relationship between security and productivity. Good security is needed to make productivity possible, but security measures could, in some instances, hinder workplace efficiency. New technologies are enabling security systems to have a more profound and positive impact on productivity by yielding better intelligence to guide the improvement of workplace practices. Multiple systems that work together, rather than separately, improve the productivity of security processes. We asked this week’s Expert Panel Roundtable: How can physical security systems contribute to productivity?
In the United States, they are called license plate recognition (LPR) systems. In Europe, the more common term is automated license number-plate recognition (ANPR). In either case, the systems provide capabilities that can benefit a range of applications from schools to municipalities to parking lots. Newer technologies can even identify vehicle color, type, make, and model. We asked this week’s Expert Panel Roundtable: What's new with license plate recognition (LPR) and/or automated number-plate recognition (ANPR) systems?
Headlines of violence in our schools are a reminder of the need to keep educational institutions safe. In fact, if there is a positive aspect to the constant bombardment of headlines, it is that it keeps our attention perpetually focused on how to improve school security. But what is the role of physical security systems? As the new school year begins, we asked this week’s Expert Panel Roundtable: Are schools safer because of physical security systems? Why or why not?
Products


White papers

Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
Download
Access management in higher education
Download
School Security Checklist
Download
Leveling Up With Campus Safety
Download
Smart Surveillance In The Workplace
Download
How To Ramp Up Perimeter Security With License Plate Reader Technology
Download
Thermal Cameras: Can They Accurately Detect Body Temperatures?
Download
How Plate Reader Technology Increases Your Perimeter Security
Download

Videos
Perimeter security: Manufacturers & Suppliers
- Senstar Perimeter security
- OPTEX Perimeter security
- DSC Perimeter security
- Dahua Technology Perimeter security
- Climax Technology Perimeter security
- Axis Communications Perimeter security
- eneo Perimeter security
- RISCO Group Perimeter security
- Bosch Perimeter security
- Aritech Perimeter security
- SightLogix Perimeter security

Multi-Residential Access Management And Security
Download
Guide For HAAS: New Choice Of SMB Security System
Download
Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
Download
Hikvision: Solar Powered Product Introduction + HCP
Download
Facial Recognition
Download