Healthcare security
Healthcare news
Milestone Systems, a global pioneer in video technology, is at the forefront of the video security industry, emphasizing responsible technology innovation across its operations. The company will host this free, one-day event on May 7 in Toronto. Geared to IT pioneers and security professionals, the day will feature engaging presentations from Milestone's technology partners across key industries such as education, healthcare, city surveillance, and hospitality. Attendees will gain insights into the latest developments in AI technologies, cloud video strategies, and Milestone's newest product offerings. Reshaping the future of security A keynote session from renowned AI expert Steve Brown promises to be a highlight of the event A keynote session from renowned AI expert Steve Brown promises to be a highlight of the event. Brown, a former executive at Google Deepmind and Intel, and an advisor to Fortune 100 pioneers on how to innovate with AI, will share his insights on how artificial intelligence is transforming video technologies and reshaping the future of security and business operations. "We are excited to bring together security professionals from across Canada to explore the cutting-edge video technologies that are shaping the future of our industry," said Peter Lintzeris, Director of Sales, Canada, at Milestone Systems. "The Toronto XPerience Day offers a unique opportunity to learn from experts, network with peers, and discover how Milestone's open platform solutions can help organizations optimize safety and efficiency." Video management innovations The event will be held at Steam Whistle Brewing in the heart of downtown Toronto. Following the day's presentations, attendees are invited to network with fellow security professionals and speak one-on-one with Milestone experts during a relaxed social hour. "Milestone is committed to empowering our partners with the knowledge and tools they need to succeed in today's fast-paced security landscape," said Lintzeris. "We look forward to an engaging and informative event, and to continuing to support the Canadian security community with our open platform video management innovations."
Just like fighting against the spread of disease in a clinical environment, healthcare providers must mobilize, coordinate with interconnected partners, and apply sufficient budgetary resources to combat an ever-changing cyberattack landscape. A new set of safeguards is necessary to protect the confidentiality, integrity, and availability of critical healthcare business operations and data. Ponemon Institute report Not “if,” but “when” healthcare facilities expect a cyberattack - It’s no longer a question of if a healthcare facility–will suffer a cyberattack—it’s when. Plus, the extensive facilities are no longer the only targets. Not surprisingly, the healthcare industry, which maintains some of the most sensitive data and has stretched budgetary resources, is the biggest target for cyberattacks and has a high associated response cost, according to the latest report by the Ponemon Institute. The Ponemon Institute studies the costs of global cybercrime and data breaches year over year. The Ponemon Institute studies the costs of global cybercrime and data breaches year over year The Ponemon Institute report, made in collaboration with IBM, states the average total cost of a data breach reached an all-time high of USD 4.45 million in 2023. The increase represents a 2.3% increase from the 2022 cost of USD 4.35 million. Since 2020, the average cost has risen 15.3% from USD 3.86 million in the 2020 report. The report recommends that the healthcare industry invest in incident response planning, testing, employee training, threat detection, and response technologies. Safeguard critical information The statistics on cyberattacks are sobering. According to CISA (Cybersecurity and Infrastructure Security Agency), the United States operational lead for federal cybersecurity, cybercrime is happening exponentially. Furthermore, it is sometimes occurring at the hands of sophisticated government-backed criminals. Cybersecurity can no longer be left solely to the IT department. Instead, it is an organization-wide and industry-as-a-whole duty. Common phishing strategies Initial attack vector–16% of the time worldwide–is an internal phishing attack along with stolen credentials Every healthcare facility workforce member, including contractors and volunteers, with access to digital information, electronic health records, or network resources, including the internet, must share the duty to safeguard critical information—because it takes just a single unmitigated incident to put a healthcare facility at risk. According to The Joint Commission, a US nonprofit that accredits healthcare organizations and programs, just one person can jeopardize an organization’s security efforts if they fall prey to common phishing strategies. The initial attack vector–16% of the time worldwide–is an internal phishing attack along with stolen credentials, according to the Ponemon Institute. Current cyber risks in healthcare The current risk landscape in healthcare includes significant regulatory compliance risks and sophisticated, often government-supported cybercriminal networks. The healthcare industry and its caretakers have access to much more comprehensive patient information due to the push towards interoperability and interconnected healthcare organizations. However, the regulatory landscape demands heightened security and more accessible patient information. It’s important to note this expansive sharing of healthcare data poses a significant risk to patient privacy and security and a wide variety of regulatory obligations. HIPAA regulations 21st Century Cures Act and its implementing regulations require healthcare and certain technology The well-established HIPAA regulations, increasingly new and broad state privacy regulations, and even the European Union’s sweeping General Data Protection Regulation (“GDPR”) all carry the colossal potential for fines and regulatory oversight. The 21st Century Cures Act and its implementing regulations require healthcare and certain technology providers to offer much less burdensome access and sharing of electronic patient data and prohibit “information blocking” with massive risks for regulatory fines and exclusions for noncompliance. Availability and assignment of sufficient budgetary resources for such compliance-related safeguards are becoming increasingly complex. Cybercrime Cybercrime is the other severe risk. Every connected device faces the potential of a cyberattack targeting healthcare data and systems. While some hospital data breaches appear in the news, most don’t reach the public’s attention. In 2020 alone, one in three healthcare organizations around the globe reported a ransomware attack, according to the American Association of Medical Colleges (AAMC). Why is that? Because healthcare data is ten times more valuable to cybercriminals than credit card information. In addition, sophisticated criminals know about the healthcare industry’s struggle to keep up with the risks they pose. Medical identity theft Healthcare data is precious and increasingly sold on the “dark web,” according to healthcare privacy attorney Sheila Stine, JD, CIPP/US, who helps healthcare clients prepare for and respond to data breaches and teaches about identity theft. Stine says, “The dark web is the ‘web below the web’ or a part of the internet only available using special tools. It is the bad guy’s sophisticated marketplace. Medical data sets have great value to cybercriminals for medical identity theft." Cybercriminals can sell medical data sets via the dark web in exchange for access to emergency care" "Cybercriminals can sell medical data sets via the dark web in exchange for access to emergency care, access to prescriptions and durable medical equipment and even fraudulent access to commercial health insurance or Medicare/Medicaid. They are smart enough to even know to sit on the data for a year or more after accessing it to avoid detection during the standard one-year period of credit protection that some organizations offer their customers and patients.” Cyberattacks with adequate security Healthcare administrators tend to focus stretched resources on patient services. AAMC senior director of information security, Dr. Stephen Lopez, says, “It can be hard to divert resources to information security if it seems to come at the expense of patient services.” However, healthcare organizations can only defend against ransomware and other cyberattacks with adequate security measures. There should be an appropriate balance between information security defense and patient services. Yet, that balance can be challenging to determine. Cyberattacks have become so prominent numerous articles have been published surrounding hospitals and clinics in numerous states that have been hit by these intrusions, causing emergency rooms to be closed and ambulances diverted to other hospitals. In an article by ABC News, the American Hospital Association's National Advisor for Cybersecurity and Risk, John Riggi says, “These are threat-to-life crimes, which risk not only the safety of the patients within the hospital, but also risk the safety of the entire community that depends on the availability of that emergency department to be there,” Malware attack Immediately after this incident, all USB drives were disabled, along with a host of other protocols In personal history as a director of safety and security for a major healthcare organization, seen the extent of damage that can occur from a seemingly careless act. At a healthcare system in the Midwest, an organization was hit with a malware attack when a healthcare worker found a USB drive in the parking lot. Colleague in a suburban clinic thought she could identify who it belonged to by seeing what files were on it. Once she inserted the drive into a computer, ransomware infected the clinic system against her knowledge. Thankfully, the team discovered the malware, which only infected the regional clinic. The ransomware asked for over $200,000.00. However, the organization rebuilt the system and had to re-enter the data for the clinical day manually. Immediately after this incident, all USB drives were disabled, along with a host of other protocols. Every day, this type of incident happens countless times across the healthcare industry and beyond. It’s not worth the cost and effort when workers can train on the appropriate response. How Milestone can help In such an unpredictable and highly regulated landscape, healthcare organizations must leverage their people's power and the strength of their security solutions to defend against cyberattacks. The Joint Commission found that 'healthcare organizations must guard against a wide variety of attacks and teach staff to expect the unpredictable as hackers continuously adapt their strategies.' Attack vectors vary widely from phishing attempts to network penetrations and device attacks. Consequently, video management software (VMS) and connected devices are vulnerable to criminals seeking data access and system control. Pro security platform products XProtect® VMS by Milestone is designed and alone tested to meet the highest security standards Milestone Systems recommends continuous updating of the VMS as one method to secure systems and data against a cyberattack. XProtect® VMS by Milestone is designed and independently tested to meet the highest security standards, and a security response team supports it. In addition, Milestone offers a choice of software maintenance packages and professional services to help pro security platform products. Also, consider the following methods to strengthen the security network against cyberattacks: Add strong camera passphrases or long 10+ character passwords following industry-recommended standards of a combination of upper case, lower case, numerals, and symbols. Whenever possible, isolate security networks from other PC and workstation networks. Secure the network to ensure only installed cameras can communicate. Deploy individual logins with role-based permissions appropriate to the operator’s role which, expire or are validated periodically. Prohibit sharing and writing down passwords. Individual role-based passwords may help determine the root cause of an incident or attack. Fully document suspected incidents and maintain those according to formal incident response and record retention policies. Conduct periodic systemwide risk assessments. As they become known: Fully document known or reasonably suspected risks. Determine how to mitigate such risks within expected completion timeframes. Evaluate acceptance of residual risk by authorized management personnel. Conduct thorough vendor due diligence. For instance, only purchase cameras and VMS from reputable, sound security companies and avoid organizations with known cybersecurity vulnerabilities. Disable USB ports and device cameras that are unnecessary for routine work. Carefully design BYOD or “bring your own device” policies to limit authorized use of personal devices. Deploy firewall security for internet connection. Insure organizations against various types of cyber liability. Teams should frequently backup critical data and then “backup the backup” in a different physical location. Periodically train and retrain workforce members on privacy, security, and escalation of incident requirements. Document reasonable sanctions against workforce members who violate organizational policy, contractual, or legal requirements. Security measures and risks Additionally, healthcare organizations can bolster their security measures through “hardening” — continuously identifying and countering evolving security risks. To harden video technology, enact several actionable steps: Identify the components that need protection on a written log or other documentation; Harden the surveillance system’s servers, computers, device networks, and cameras on a routine basis; Document, maintain, and periodically update security settings for each system; Deploy security software patches and updates reasonably promptly; and Train the team to help identify future threats and implement countermeasures. Smaller healthcare organizations can also leverage many available resources for small businesses offered by governmental agency resources, such as the National Institute of Standards and Technology (NIST) small business cyber security resource page. These are just some initial recommended steps toward a successful defensive security posture. There are still multiple opportunities for cybercriminals to attack both internally and externally. However, healthcare organizations can better protect their vulnerable security infrastructure by automating and strengthening processes in partnership with Milestone Systems. Defend against “walk-in attacks” While many cyberattacks often launch from a distance, some incidents physically take place in the facility While many cyberattacks often launch from a distance, some incidents physically take place in the facility. For example, “walk-in attacks” occur when a criminal enters a facility with or without authority and may look for easy targets, such as unsecured laptops to steal, open ethernet ports to hack, unsecured portals, sites “open to the internet,” or weak passwords on Wi-Fi networks. Most facilities and networks have safeguards to defend against such apparent threats. However, employees must still maintain vigilance and watch for people who don’t belong. For instance, healthcare facility policy and training should prohibit “piggybacking” or allowing someone to follow an authorized person through a locked door without using their credentials. Using best practices, the security team should train the workforce to watch for those not appropriately picture-badged in restricted areas. Integrations for the XProtect platform Milestone Systems works with a community of technology providers with integrations for the XProtect platform to alert facility security members of unauthorized people in restricted areas. For example: Video analytics determine activity and behaviors captured by cameras, triggering automated processes and notifying operators of problems, such as unauthorized personnel crossing a virtual perimeter into a restricted area. Access control allows or restricts entry at doors based on credentials. In addition, with integration into the XProtect platform, nearby cameras can be used for video verification when needed. Infrared sensors detect human activity in restricted areas. Alerts can be sent to security operators for immediate action when necessary. Range of security protocols Milestone Systems also has developed a range of security protocols and integrations for the platform, for example: Security through network separation XProtect uses a tiered system architecture to separate the camera network and the core server/client network, so there is no direct routing between the two. The architecture increases the system’s resilience and lowers a potential attack’s impact on the system. Secure camera connection Certificate-based HTTPS communication provides secure access for management client and smart client users and bidirectional communication encryption between all the system’s components, which prevents eavesdropping and tampering. Leveraging certificate-based HTTPS communications ensures secure, trusted access for facility administrators while preventing decryption eavesdropping and tampering. Secure video storage XProtect corporate can encrypt and password-protect media data, meaning recorded data is protected even if someone accesses the data files on the storage system or network share. XProtect corporate also supports a digital signature on the recorded media data, proving the video is the original. Strict server-side authentication and authorization XProtect uses consistent server-side user authentication and authorization for all clients and integration interfaces. This authentication applies to all users and system services accessing the system via the Milestone Integration Platform SDK or Milestone Open Network Bridge. Used together with strict user rights and roles, it provides complete control of access to the system. Built on Windows security infrastructure XProtect supports Windows active directory (AD) with both native Windows NTLM and Kerberos authentication, alongside OpenID Connect and OAuth2, for maximum security. Secure remote user access XProtect uses a dedicated mobile server as a system gateway to shield and protect the core VMS servers when users connect remotely. The mobile server, mobile client, and web client communication support HTTPS to prevent eavesdropping and tampering, providing secure authentication and bidirectional encryption, which includes user credentials, configuration, and media data. Protection of evidence material To protect exported forensic material, XProtect uses encryption, digital signing, and password protection of the media databases. XProtect’s smart client player ensures that exported evidence is original and unaltered by verifying signatures and preventing evidence from re-exporting to control the media once it leaves the VMS. Milestone Systems supports healthcare facilities and their data by continually updating the platform. As a result, organizations can focus on patient-centric care. Working towards what’s next How healthcare facilities face the challenges of tomorrow depends on the planning and choices they make. With an adaptable, scalable, and open platform such as XProtect VMS, healthcare facilities can be ready for what comes next and quickly pivot to improve their business outcomes. When a large healthcare organization uses the XProtect open platform, the workforce can mitigate risks, maximize existing resources, and stretch budgets further. Count on Milestone Systems as a collaborative partner, supporting endeavors to prepare for the current risks and future challenges faced in healthcare.
VIPRE Security Group, a global pioneer and award-winning cybersecurity, privacy, and data protection company, released its Q1 2024 Email Threat Trends report, based on an analysis of 1.8 billion emails. The findings reveal the evolving landscape of email-based threats and emerging tactics malicious actors are employing. The US, UK, Ireland, and Japan top the spam sources list. The report identifies the US as the top source of spam emails globally, followed by the U.K., Ireland, and Japan. The US, UK, and Canada are the top three countries most subjected to email-based attacks. Attackers aim at the manufacturing sector The manufacturing, government, and IT sectors are the most victimized by malicious actors. In Q1 2024, the manufacturing sector suffered 43% of email-based attacks, with the government (15%) and IT (11%) trailing well behind. This is a change from Q1 2023, when attackers targeted the financial (25%), healthcare (22%), and education (15%) sectors most often. Scams surpassing phishing These emails contain malicious attachments in .html or .pdf formats, featuring phishing QR codes This research warns that ‘scams’ within the spam category are growing in popularity among cybercriminals, overtaking phishing emails in the first quarter of 2024. There’s been a notable increase in phishing emails masquerading as communications from Human Resources, falsely claiming to relate to employee benefits, compensation, or insurance within a company. These emails contain malicious attachments in .html or .pdf formats, featuring phishing QR codes that redirect recipients to phishing sites upon scanning. New phishing trends and techniques In email phishing campaigns, 75% of emails leverage links, 24% favor attachments, and 1% use QR codes. Attackers are employing links in phishing emails for URL redirection (54%), compromised websites (22%), and newly created domains (15%). Emerging tactics employed by cybercriminals to execute phishing attacks include the use of .ics calendar invite and .rtf attachment file formats to trick recipients into opening malicious content. Malspam links and top malware family Malware is increasingly being hidden in cloud storage platforms such as Google Drive Encouraged by the success of password-oriented phishing emails that use links, cybercriminals are opting for malicious links in malspam emails instead of attachments. Malware is increasingly being hidden in cloud storage platforms such as Google Drive. The use of malware-based emails employing attachments has increased to 22% in Q1 2024, from only 3% in Q1 2023. Due to the void left by the dismantled Qakbot malware, Pikabot has emerged as the top malware family, with IceID a distant second. Exploiting software vulnerabilities Criminals are exploiting a web application vulnerability, most notably Reflected Cross-Site Scripting (XSS), focusing on the tag attribute “href”, to circumvent detection by using a variety of tactics such as images as the entire email content, encoding URLs, and directing the victim through multiple URLs. Malicious actors are also finding success with thread hijacking of NTLM Malicious actors are also finding success with thread hijacking of NTLM (NT LAN Manager), a security protocol used by Microsoft Windows operating systems for authentication. By hijacking the authentication thread, attackers extract NTLM challenge-response hashes from legitimate SMB (Server Message Block) sessions, to enable them to impersonate authenticated users and gain unauthorized access. Exploiting human vulnerabilities "Criminals are using email with success to scam, infiltrate networks, and unleash malicious payloads," warns Usman Choudhary, Chief Product and Technology Officer, VIPRE Security Group. "We're witnessing bad actors relentlessly exploiting human vulnerabilities and software flaws, circumventing email gateways and security measures with alarming precision. Robust email and endpoint defenses, coupled with a vigilant human frontline, remain our strongest defense against these unyielding attacks." VIPRE leverages its unique understanding of email security to equip organizations with the information they need to protect themselves. This report is based on proprietary intelligence gleaned from round-the-clock vigilance of the cybersecurity landscape.
Johnson Controls, the global pioneer for smart, healthy, and sustainable buildings, demonstrated complete building security solutions at ISC West 2024 in Las Vegas. The company showcased its comprehensive product innovation, system integration, and service expertise, ultimately enabling customers to protect their people, facilities, and assets. “Johnson Controls is pioneering new innovations that are transforming traditionally reactive physical security processes into connected data-driven solutions,” said Faisal Pandit, vice president and general manager of Global Security Products at Johnson Controls. “This year’s ISC West attendees were able to see how our products are at the forefront of transforming the security industry.” Complete building solutions Johnson Controls highlighted keys for clients across various drives including education At the show, Johnson Controls highlighted solutions for customers across various industries including education, healthcare, government, data centers, and industrial facilities. “We are among a select group of companies that can deliver complete building solutions for security professionals, from product engineering and innovation to full system integration and exceptional service,” said Julie Brandt, president of Building Solutions North America at Johnson Controls. “Johnson Controls is the driving force behind the future of secure and sustainable buildings, catering to the evolving needs of our customers." Key trends in the industry Johnson Controls pioneers also discussed key trends they are seeing in the industry such as: Shift to AI, specifically an investment across the industry in technologies with AI capabilities for advanced threat detection and response. Move to service models and an increased focus on seamless user experiences, for example, mobile-friendly solutions and streamlined, flexible operations. Customers are seeking support for managing security operations that address staffing shortages with automation, improved training, and growth programs. Renewed focus on digitization and sustainability. Businesses are realizing how security products can help meet sustainability goals, prioritize budgets for optimal operational efficiency, create healthy and productive environments that attract employees and keep occupants and assets safe. A change in user base from operations to enterprise/security management. Data is now viewed through multiple levels, showcasing the need for and importance of software modernization. An intersection of access control and video so customers can develop a strategy for a more cohesive and comprehensive security approach.
Healthcare articles
Choosing the appropriate fingerprint technology for a given application is dependent on factors including the required level of security and matching accuracy, the desired capabilities and features, and the usability to achieve adoption and productivity goals. A successful evaluation process will help ensure that this mature and proven user authentication method performs as expected. Fingerprint biometric advantages The speed, simplicity, accuracy, and cost-effectiveness of the fingerprint method have made it among the most widely used for biometric authentication across industry sectors ranging from banking and finance, retail, and healthcare, to government and law enforcement. It performs biometric technology’s “something you are” function while offering unique characteristics that make it particularly valuable for many applications. Unique identifier The fingerprint biometric has the permanency of being reasonably stable and consistent over time Among these characteristics is the pervasiveness and special nature of the fingerprint -- almost everyone has one, and each is a unique identifier. The fingerprint biometric has the permanency of being reasonably stable and consistent over time. It is also easy to acquire, measure, and process. High adoption rate Another key attribute of a fingerprint biometric is its ability to be protected against threats ranging from abuse and misuse to theft, imitation, and substitution. When it is used with recognition techniques the resulting solution performs with a combination of accuracy, speed, scalability, and ease of use. Fingerprint biometric solutions also have the highest adoption rate among biometric authentication solutions according to an industry report published by Payments Journal. Three interrelated components There are three basic components in any fingerprint biometric system as shown in Figure 1: capture (using a sensor that can capture even the most difficult finger types); liveness detection (using the Presentation Attack Detection – or PAD – technique); and matching (including preventing rejection of a legitimate user). Biometric algorithm The sensor captures and pre-processes the fingerprint data. It must be able to successfully capture fingerprint images for a range of skin types and print conditions under diverse temperatures, humidity, light, surface oil, dust, dirt, and other environmental conditions. A biometric algorithm then extracts minutiae data about the fingerprint ridges (endings, bifurcations, islands, etc.) and their orientation and position. PAD technique Implementing a presentation attack detection (PAD) technique at this stage activates the fingerprint biometric system’s second key element: liveness detection. This verifies the fingerprint’s authenticity and that it belongs to a living person. The system’s third element – matching – occurs after the PAD-verified fingerprint dataset has been securely stored as a record, known as a template, inside an enclave with cryptographic protection. Check for liveness The corresponding template of the legitimate user is then retrieved from secure storage When the fingerprint is presented for matching, it is rechecked for liveness. The corresponding template of the legitimate user is then retrieved from secure storage and the process of matching the fingerprint with this template is executed. This must be completed accurately and without rejecting a legitimate user. Types of fingerprint sensing technologies There are four prevailing categories of sensing technologies used with fingerprint readers: optical, capacitive, thin-film transistor (TFT), and multispectral imaging (MSI). Optical and capacitive method Optical is the most mature sensor technology and offers the benefits of a compact size, good capture Optical is the most mature sensor technology, and offers the benefits of a compact size, good capture and matching performance, a small enough size to fit in most desktop environments or shared workstations, and a high level of accuracy at a cost-effective price point across all use cases. The capacitive method, on the other hand, is less prone to fake finger attempts while also offering a thin and compact size for space-limited applications, the power efficiency to support battery-operated devices, and the ability to handle both indoor and outdoor lighting conditions. TFT technology The third technology goes a step further in capture accuracy. TFT technology can accurately recognize the smallest fingerprint features with ultra-high resolution and is used either as a larger-size matrix capacitive proximity detector (capacitive fingerprint sensor) or a larger-area matrix light detector (optical fingerprint sensor). It is ideal for in-the-field mobile identification applications that require a cost-effective, ultra-slim, and lightweight solution with low power consumption. MSI technology MSI technology differs from all three approaches, projecting multiple colors of light into the finger from different angles to collect both surface and subsurface biometrics data. It captures the most difficult fingerprints of diverse demographics, in a wide range of challenging environments. HID has used this patented technology in fingerprint readers that are compliant with ISO 30107-3 PAD Level 2 for advanced anti-spoofing against fraud. The technology also improves matching and offers sophisticated endpoint security that prohibits cyber criminals from gaining unauthorized access to networks by turning fingerprint readers into secure endpoints. Best practices for technology selection Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership. There are three top considerations: security, suitability, and usability. Each is important and the best approach is to strike a balance between all three. Following are the questions to ask during the selection process: Security: What is the regulatory environment? Financial and government services, healthcare, and law enforcement are some examples of highly regulated sectors with elevated security compliance requirements. Are there mandates in place for advanced capturing and biometric authentication specifications? How important is it to ensure anti-spoofing through liveness detection? Will endpoint security be required so that, if the fingerprint device is hacked, no network, system, or data behind the firewall will be impacted? Suitability: Where will the biometric technology be implemented? There will be additional considerations if it is to be embedded in portable, battery-operated devices that require low power consumption. Where will the technology be used? Will it need to fit into small spaces or be used in challenging indoor or outdoor conditions and environments? Will durability be important? Some deployments will face unpredictable weather and difficult lighting conditions for image capture. Will the technology be used for mission-critical border control or a more common – and less demanding -- commercial use? Usability Is it critical that the technology easily and consistently perform capture and matching? Will there be high volumes of fingerprint captures and matches? Is “friction frustration” a concern? If so, the solution must perform matching quickly and accurately to sustain high levels of user productivity. Will the fingerprint device be used by one person exclusively, or multiple people in a shared workstation setting? How diverse is the user population? Some readers are designed to handle all types of fingerprints and diversified demographics. Different applications Fingerprint biometrics is a proven solution to address real-world challenges, each with its requirements The answers to these questions will help determine the best choice of fingerprint technology. Different applications apply fingerprint biometrics to very different use cases but in all cases. It is a proven solution to address real-world challenges, each with its requirements. For instance, in a healthcare clinician’s terminal area or a similar shared environment with limited space, a durable, low-profile capacitive sensor may be the right answer. For an organization in a highly regulated, mission-critical environment like a bank or border control agency, advanced technologies such as MSI readers may be needed to avoid the serious repercussions of a spoofed identity or the rejection of a legitimate one. Requirements for a biometric solution These are just a few of the requirements to consider when choosing a fingerprint solution. In banking and finance, alone, fingerprint biometrics is used for applications ranging from transacting at the ATM to customer onboarding (eKYC), compliance (AML/KYC), and fraud prevention. The retail sector adds even more, including age verification, loss prevention, point of sale (POS) security, self-service checkout, and secure time and attendance. Law enforcement organizations have their unique requirements, using fingerprint biometrics for background checks, criminal booking, crime investigation, inmate management, mobile identification, and more. For government agencies, typical applications include benefits distribution, border security, citizen ID, employ authentication (SSO/MFA), and voter registration. Each application requires a thorough assessment of the best fingerprint technology for the job. The right touch The right solution will deliver the optimal balance of security, suitability, and usability Fingerprint biometric solutions empower a wide range of use cases with the simple touch of a finger. The right solution will deliver the optimal balance of security, suitability, and usability based on an analysis of criteria including specific application requirements, the characteristics and size of the user population, and challenges posed by environmental conditions. Accuracy, efficiency, and security The world faces increasingly dangerous fraud, account takeover, and impersonation threats. As industries and enterprises work to improve and evolve their identity and access strategies to combat these threats, fingerprint biometrics continue to prove their value through solutions that meet the key selection criteria while delivering the highest levels of accuracy, efficiency, and security.
The autumn equinox, which marks the start of autumn, occurs this weekend on Saturday, September 23. With darker evenings ahead, the experts at ADT have shared five ways to maximize your home's security. Author's quote Michele Bennett, General Manager at ADT UK&I comments: “Opportunistic thieves use darkness to their advantage, so it’s no surprise that the number of burglaries committed increases when the darker nights draw in." He adds, "Our 2022 burglary report found that burglaries are most common at night, with 58% of burglaries occurring between 6 p.m. and 6 a.m. Taking steps to optimize your home’s security before the clocks go back this year will provide reassurance that your property is as secure as possible.” Five ways to secure your property: Get a monitored alarm installed: A visible alarm system is a strong deterrent to potential burglars, as criminals are less likely to target a home that is protected. In the event of a break-in, a monitored alarm will alert you, your keyholders and depending on the package you take out, the police, ensuring a swift response to an alarm activation. Light up the dark: Well-lit exteriors make your home less appealing to potential intruders. Install motion-activated lights around any entry points, particularly porches and gardens, which alert you to movement on your property. This will also prevent burglars from operating under the cloak of darkness and increase the chance of a passerby spotting suspicious activity. Trim your garden landscape: Thieves look for escape routes and hiding spots when deciding which homes to break into, making gardens with high, overgrown hedges more likely to be targeted. This is especially true in the darker evenings, so be sure to give your garden a thorough tidy-up to make your property less likely to be targeted. It’s also advisable to ensure any tools are locked away in sheds and garages that could assist a burglar such as ladders, or a garden spade to force entry. Be smart with your lights: Using smart plugs allows you to turn on a few well-appointed lights and radios or televisions from any location from your phone. Used in conjunction with an outdoor camera or video doorbell, you can have lamps plugged into smart plugs come on when motion is detected. Programming lights to come on at different times throughout the night will help to deter burglars by making your property look occupied. Purchase a smart doorbell or outdoor camera: Smart doorbells are an effective way to deter burglars as they provide evidence in the event of a break-in, package theft, or other suspicious activity around your home. They also notify you when someone is at your door reducing the chance of you being caught out by a late evening or early morning robbery. Further encroachment Smart doorbells also act as a deterrent to unscrupulous door-to-door sellers and con artists, as video footage is recorded. In the event of a late-night door knock, you can see and speak to whoever is at your front door, without having to open the door. ADT’s new outdoor camera also has two-way audio and a high-pitch deterrent siren so you can warn off anyone from your property to deter any further encroachment.
Daniel May of Consort reviews the integration of access control systems in healthcare settings, outlining the benefits and key considerations decision-makers must make throughout product specifications. From patient safety and traversal to the protection of sensitive data and pharmaceuticals, healthcare environments are faced with several operational challenges. And where security remains at the forefront of decision-making, modern access control systems may often hold the answers. Physical security systems Hospitals in particular have developed into multi-faceted spaces that house hundreds to thousands of patients, staff, and visitors at any one time. In England for example, research has found in the three months leading to June 2023, an average of 44,626 people visited major hospital A&E departments each day, with over 16 million attendances typically recorded over the course of a year-not to mention an additional nine million logged at other minor units. For any building, this level of sustained footfall can request severe security difficulties For any building, this level of sustained footfall can invite severe security tests. With that, the need to deploy effective physical security systems in healthcare is clear. And so, as access control continues to become more readily adopted and new products enter the market, decision-makers are reminded to consider the requirements of their building, ensuring they select the solutions most suited to their settings and budget. Security controlled Patient safety will always remain the top priority in healthcare settings, and where matters of health and social care come into question, a diverse set of professional regulatory bodies are tasked with setting and maintaining high standards. When it comes to healthcare premises specifically, patient security and perimeter security often come hand in hand and are amongst the most pressing of challenges that decision-makers must face. To help address operational planning and potential design concerns in the NHS, the Health Building Note (HBN), provides general design guidance for healthcare buildings under HBN 00-01-citing the use of access control measures as a way of maintaining security and protecting the safety of patients, staff, and visitors. Use of access control Hospital buildings control varied levels of access for a number of security purposes Hospital buildings, for example, must control varied levels of access for a number of operational and security purposes. Routine scenarios exist where vulnerable patients are under monitoring and thus refrained from exiting the premises for their own safety, while at the same time, permitted staff must be able to reach their patients and medicines when required. For this, the use of access control is key. Equally, access credentials can also help management teams keep track of those who may be entering or exiting rooms with equipment and pharmaceutical supplies, deterring any unwanted visitors and opportunists in the process. Incorporation of access control systems On a similar note, regulations have set a minimum standard for how personal data should be stored and managed in healthcare environments, giving decision-makers an added responsibility to regulate staff-controlled areas with patient medical records. While instances of personal data breaches are rare, healthcare facilities and professionals are at legal risk should confidential data be found misused or missing. As such, the incorporation of access control systems has become essential in keeping data storage areas secure, with intuitive online systems capable of permitting access to staff with the correct credentials while simultaneously tracking who has requested clearance at digital entry points. HBN guidance Healthcare experts are better fitted to control the sheer volume of people entering and exiting To function effectively, healthcare facilities must always be perceived as safe places by the people who reside within them, and as HBN guidance implies, a unified physical security system can help address key safety and security concerns while enhancing patient and staff experience. Opportunely, access control systems are more accessible and adaptable than ever and combine several technologies such as mechanical locks and automatic doors with electronic access credentials in the form of smartphone apps, badge readers, and biometric scanners. By integrating these systems into the building’s existing infrastructure, healthcare professionals are better equipped to control the sheer volume of people entering and exiting the premises without impairing the general flow of movement and coordination around the facility. Better by design Despite the clear benefits offered to healthcare facilities, there are a number of considerations to be mindful of when choosing an access control solution. Poorly implemented systems can have an adverse effect on security and functionality - quickly costing healthcare organizations time and budget to rectify and replace the inadequate products that don’t meet the building’s requirements. For that reason, decision-makers and design teams are reminded that there is no single solution that fits all healthcare buildings. As such, it’s crucial for decision-makers to understand the systems that are being put in place throughout each of the touchpoints in their facility. Clear collaboration is required during periods of specification, where together, teams can ensure the selected product works on all angles, from meeting fire safety and sustainability standards to aesthetics and scalability. Modern access control products Scalability is a key area that decision-makers must review when selecting access control systemsFrequently overlooked, scalability is a key area that decision-makers must review when selecting access control systems. Such is their diverse nature; healthcare facilities can often change and develop as years go by, and by selecting a system that facilitates growth, such as a cloud-based solution-security and efficiency is long-established. While modern access control products are known for seamless integration, there are some systems that may restrict the ability to use different vendors throughout the remainder of the building’s infrastructure. This, in effect, causes a monopolization of products throughout the estate, which can have an adverse effect on growth by increasing costs and reducing the levels of service associated with the security system already in place. Improve security and safety A scalable and reliable access control system will continue to improve security and safety by adapting to a building’s new requirements-and all while having minimal impact on its operational network. And so, while technology will no doubt continue to influence and transform the access control market, healthcare facilities and their professionals must continue to remain educated on their own systems, ensuring they have the best options in place to keep their patients, staff, and visitors safe and secure for years to come.
Healthcare case studies
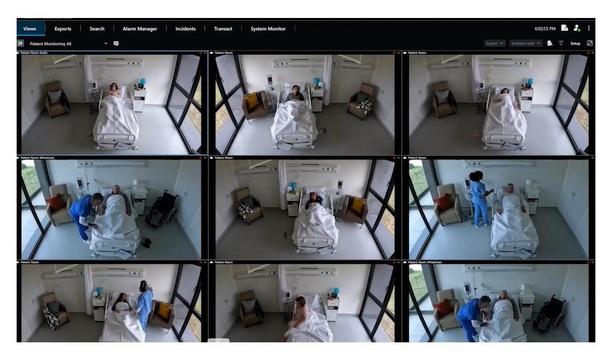
With 1,300 cameras recording 24/7 and more than 1,000 investigations to process per year, Massachusetts General Hospital’s security team was not able to keep up with the vast amounts of recorded video. Now, BriefCam Syndex Pro for fast video review, search and analysis, embedded within a Milestone XProtect video management software (VMS) platform is making efficient and effective video investigation possible. Unique challenges to security Massachusetts General Hospital’s (MGH) Police, Security and Outside Services Department provides some security services to many other Partners hospitals and facilities. Following its recent digital conversion, unified on the Milestone XProtect VMS platform, MGH’s security team was able to expand camera coverage by adding new Axis network cameras directly to the existing IP network. The hospital environment presents unique challenges to security, Michelman points out “The number of investigations we were doing was taking huge amounts of time in terms of reviewing video, and that was really a waste of time,” said Bonnie Michelman, MGH Executive Director of Police, Security and Outside Services and Consultant for Partners Healthcare. The hospital environment presents unique challenges to security, Michelman points out. MGH’s 17-acre urban campus, comprising 29 contiguous and 14 separate buildings (including underground and freestanding garage facilities), is complex. The security team must also take into account not only the main location, but also dozens of satellite facilities around the Boston area. Enterprise risk management “We can’t cover all of these facilities with security staff,” said Michelman. “We need to augment heavily with very good, state-of-the-art technology that allows us to combine our intelligence, labor, policies and procedures, in order to create a better holistic approach to enterprise risk management.” Charged with creating a safe environment, MGH’s security team at the same time is challenged by the clinical team’s needs for increased efficiency through lowering length of stay and moving patients through the hospital as quickly as possible. The 24-hour Emergency Room, with its anxious, highly volatile population presents challenges of its own. In addition, patient elopement and patient wandering – unauthorized departures from the medical facility, whether intentional or unintentional – pose liability threats that can be very damaging to a hospital. Providing customer satisfaction A unified system was required to balance the video surveillance needs of a busy hospital campus A unified system was required to balance the video surveillance needs of a busy hospital campus with remote satellite locations while upholding the highest level of security possible, maintaining operational flow, and providing customer satisfaction that includes expectations of privacy. Michelman, together with MGH Senior Manager, Systems and Technology Robert Leahy, decided on the Milestone XProtect VMS platform. Camera count was increased from 400 to 1,300, and standardized with Axis network cameras connected directly to the IP network. To deal with the marked increase in video data, MGH’s team chose BriefCam Syndex Pro, a powerful set of tools intended to reduce the time and effort needed to conduct video reviews, post-event video investigation and real-time video monitoring. The BriefCam solution ties in seamlessly with the Milestone video management solution, providing efficient workflow for investigators. Presenting video metadata According to Michelman, BriefCam has already proven invaluable. A two year long ROI examination of video surveillance use at MGH has shown a progressive rise in success rates with the use of video in incident investigations. According to Michelman, BriefCam has already proven invaluable “I see BriefCam as a very important part of our toolbox of excellent practices for protecting what is a very complex environment of tangible and intangible assets,” said Michelman. BriefCam Syndex Pro’s ability to present video metadata in graphic visualization format, such as bar graphs, pie charts and the like, has opened up new realms of possibilities to extend the role of CCTV video beyond security into organizational efficiency and more informed, data-driven decision making. Better investigative focus “In the past, there might have been things that would have been a ‘nice to do,’ but we couldn’t do it because we didn’t have resources to watch many hours of video,” said Michelman. “Now we can manage the content and we can see trends, which in turn can drive redeployment of resources, and by extension, facilitate a better investigative focus and success.” BriefCam Syndex Pro embedded within Milestone XProtect VMS platform is helping MGH in its mission to effectively and efficiently protect and safeguard the hospital community. Michelman said: “We’re happy with these products, but it’s not just about the quality of the technology, it’s about the quality of the partnership. You know, it’s easy to sell a product, but to sustain it, service it, and be there after it is in is really very critical for us.”
TDSi products can be easily synchronised with existing security investments from many third parties The Healthcare market is an area of expertise for security solutions specialist TDSi. Not only does it require the most stringent security, the Healthcare sector often has strict budgets and involves caring for some of the most vulnerable people in society, so any solution needs to be highly reliable and easy to operate and manage. Specific areas such as hospital pharmacies need higher levels of security due to the value of stored products; baby units or wards for elderly patients typically require access control to monitor both entry and exit. There may also be specific security considerations for staff, with lone workers or remote parts of healthcare facilities that could be open at any time, day or night. Despite this, staff, patients and visitors need to be able to move around with a minimum of disruption. TDSi’s range of access control and security solutions are designed to integrate efficiently with each other and also in close collaboration with other manufacturers’ products, such as Texecom’s alarm systems and Milestone’s CCTV solutions. TDSi products can be easily synchronised with existing security investments (from many third parties) or installed from scratch to offer fully bespoke security. By offering a wide choice of access control options along with the ability to record a detailed audit trail with their highly flexible software packages, TDSi is the ideal choice for installers and customers in the Healthcare sector. An excellent example of TDSi’s expertise in this market is a recent installation at London’s Charing Cross and Hammersmith Hospital, which covers an impressive 617 doors across multiple sites and integrates with both security and fire systems for a rapid response in an emergency. John Coleman, Managing Director of expert installation specialist Advanced Detection Systems (ADS), which specified TDSi’s solutions as part of the project commented, “This has been a major and high-profile project for us which required a best-of-breed solution for the access control element. TDSi systems are specifically designed to integrate with other building services and security systems and are particularly well suited to projects where CCTV, fire alarms and access control need to work closely together to protect people and property. In partnership with TDSi, we were able to offer Charing Cross and Hammersmith Hospital, solutions which fully met their needs and give peace of mind that patients and staff can be fully protected from emergencies and potential security breaches, at all times.” TDSi’s EXpert controller features a stand-by battery facility that allows the system to continue operating in the event of power failure The project uses TDSi’s EXpert IP controllers, fully featured networkable access control units, with supervised inputs and relays, making them ideal for monitoring and signaling alarm conditions which could occur at Charing Cross and Hammersmith Hospital. With capacity for up to 48,000 cards, the flexible access controller is ideal for those applications that feature high user volumes through access points - such as a busy hospital and teaching environment. TDSi’s EXpert controller features a stand-by battery facility that allows the system to continue operating in the event of power failure and at these times the system can be controlled without the need for PC communications, so controlled access is maintained. TDSi’s Director of UK Sales, Stuart Griffiths, explains, “The project at Charing Cross and Hammersmith Hospital is an excellent example of how TDSi’s systems can be easily and very successfully integrated with other building services and security solutions to offer a highly intelligent and powerful access control system. A hospital environment protects many vulnerable people and assets, so being able to fully co-ordinate security while making the most of existing asset investments (particularly when budgets are under closer-than-ever scrutiny) is a highly desirable outcome for all stakeholders.”
A distinguished pharmaceutical company, based in Saudi Arabia, has been unwavering in its dedication to establishing a state-of-the-art pharmaceutical manufacturing complex. Their ambitious initiative is geared towards combating chronic and life-threatening diseases, reflecting the company's vision to address unmet needs in the pharmaceutical sector within Saudi Arabia and the broader MENA region. By steadfastly committing to this mission, the company positions itself at the forefront of advancing healthcare solutions, poised to make a significant impact on public health. Mobile attendance capabilities Overview - The client encountered a diverse set of challenges, ranging from outdated hardware in their Access Control and CCTV systems to the intricate integration of advanced access control features and payroll data with SAP. Amidst disruptions to work continuity, these challenges encompassed preserving the functionality of the existing system, consolidating monitoring for emergency response, and introducing mobile attendance capabilities within specific areas. Client faced a diverse set of challenges, ranging from outdated hardware in their Access Control Matrix's all-encompassing solution effectively tackled these multifaceted obstacles, utilizing expertise to seamlessly integrate systems and deliver customized resolutions. This ensured optimal resource utilization and a streamlined workflow for the client. Procuring essential resources Challenges - The challenges confronted by the client were inherently complex, spanning from outdated hardware issues to the intricacies of payroll integration. The client faced difficulties in procuring essential resources for implementing effective solutions, resulting in disruptions to work continuity and impeding the optimal utilization of resources. Challenges faced in Access Control and Attendance Management: Obsolete Hardware Components: The client faced the dilemma of dealing with ageing infrastructure, as the Access Control and CCTV hardware, installed a decade ago, approached obsolescence. Implementation of Advanced Access Control Features: The client articulated the need for advanced access control features, introducing the challenge of seamlessly integrating these capabilities with their existing access control system while ensuring the preservation of the current system's functionality. Integration for Streamlined Monitoring: A pivotal challenge revolved around integrating access control and surveillance systems to enable unified monitoring on a single screen. The client sought features like Alerts and Video Pop-ups to enhance emergency response, monitor door access, and identify Access Rules Violations. Integration of Employee Attendance Data with SAP: Seamlessly integrating employee attendance data with SAP for efficient payroll processing was a requirement. This presented a challenge in ensuring compatibility and accuracy in the synchronization of data. Implementation of Mobile Attendance within Designated Locations: The client aspired for a solution enabling mobile attendance within the geographical confines of their head office and plant locations. This posed a distinctive challenge in providing flexibility without compromising security. Against this intricate backdrop of challenges, Matrix applied its expertise and innovative solutions to deliver a comprehensive and customized resolution. Proactive security measures Payroll processing demonstrated Matrix's commitment to delivering more than just a solution Solution - Embarking on a transformative path, Matrix provided a seamless resolution to address all client concerns. The integration of video surveillance, implementation of proactive security measures, and streamlined payroll processing demonstrated Matrix's commitment to delivering more than just a solution–a customized and future-ready security ecosystem for the client. Matrix tailored a solution for Access Control and Attendance Management: Seamless Integration of Existing Access Control and Video Surveillance Systems: Utilising the Matrix COSEC application, Matrix integrated the client's current access control system with the Matrix COSEC ARC DC200P. Concurrently, Matrix linked the existing video surveillance solution with Matrix Server Grade Enterprise Network Video Recorders and Matrix IP Cameras. This strategic approach not only maximized the use of the client's current infrastructure but also resulted in significant cost savings, presenting a seamlessly integrated solution. Implementation of Advanced Access Control for Heightened Security: To address the client's demand for advanced access control features, Matrix integrated the existing system with its access control solution. This integration expanded security measures with features like Man Trap, Time-Based Access, Zone-Based Access Policies, and Fire Alarm Integration. The outcome was a comprehensive security framework, enabling centralized control over employees' movements within secure areas. Unified Monitoring and Proactive Security Measures through Video Surveillance: Matrix's R&D team achieved a unified monitoring system with alerts and video pop-ups for emergency door access and Access rule violations. This seamless integration between access control and video surveillance established a responsive and proactive security infrastructure. The result was a unified monitoring experience on a single screen, enhancing the client's ability to address security concerns in real time. Effortless Payroll Processing with SAP Integration for Enhanced Attendance Management: Matrix's time-attendance solution facilitated the integration of the client's active directory for user master data and seamlessly incorporated processed attendance data with SAP. This integration streamlined the payroll process, ensuring accuracy and efficiency in salary calculations. The client experienced a trouble-free payroll integration, mitigating the risk of errors in the salary processing workflow. Mobile Attendance Solution within Geo Attendance Capabilities: Matrix met the client's requirement for mobile attendance with the COSEC APTA mobile application. This solution enabled the client to establish a geo-fence around their head office and plant locations, allowing employees to mark their attendance via mobile phones within the designated limits. This innovative approach provided flexibility without compromising security, aligning with the client's specific needs. The seamless integration of solutions in this comprehensive security system not only addressed the client's challenges but also elevated them to a pioneering position in advanced security and access control technologies. Application scenario case Demand for integrated solutions Beyond fortifying security, this integrated system offers a streamlined monitoring experience Results - In the constantly evolving realms of security and organizational management, the demand for integrated solutions has become crucial. Client's journey encapsulates the challenges stemming from outdated hardware in their Access Control and CCTV systems, pioneering to the intervention of Matrix's R&D team. Consequently, a comprehensive solution emerged, seamlessly integrating CCTV and Access Control functionalities. Beyond fortifying security, this integrated system offers a streamlined monitoring experience, eliminating the necessity for disparate applications. Furthermore, the inclusion of video pop-ups and email alerts ensures a proactive response to exceptions. In addition to enhancing security features, the solution integrates their centralized Attendance system with SAP, optimising not only security but also administrative processes. This holistic approach underscores Matrix's dedication to delivering innovative and efficient solutions tailored to the client's evolving needs. Products Offered COSEC PANEL200P: Access Control Hub COSEC ARGO FACEI: Face-based Door Controller COSEC ARC DC200P: Two-Door Access Controller COSEC ATOM RD100KI: Reader with Keypad SATATYA NVR06408XCTS: 64 Channel Enterprise grade Network Video Recorder SATATYA MIDR50FL28CWS: 5 MP Professional Series Dome IP Camera SATATYA CIBR50FL28CWS: 5 MP Project Series Bullet IP Camera with Fixed Lens SATATYA CIBR50MV12CWP: 5 MP Project Series Bullet IP Camera with Motorized Lens COSEC CENTRA ACM: User Licence for Access Control Management COSEC CENTRA TAM: User Licence for Time-Attendance Management COSEC CENTRA FR: User Licence for Face Recognition COSEC CENTRA ESS: User Licence for Employee Self-Service SATATYA SAMAS CAM20: Camera Licence
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the US Department of Homeland Security SAFETY Act Designation, announced that its proactive gun detection and intelligent situational awareness solution has been deployed at JPS Health Network in Fort Worth, Texas to mitigate gun-related violence. Located in Tarrant County, the 582-bed hospital includes an acute care facility, outpatient care centers, and psychiatric emergency room. Its Level I Trauma Center receives over 125,000 emergency department visits annually from local and air EMS agencies, as well as others outside the county. HIPAA-compliant AI gun detection If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence “At the hospital, we witness first-hand the impact of gun violence, which is why we strive to safeguard our patients, staff, and visitors,” said Randell Hayen, Chief of the Tarrant County Hospital District Police Department. “Along with our onsite police department, adding ZeroEyes gives us another tool to use to do just that.” ZeroEyes' HIPAA-compliant AI gun detection and intelligent situational awareness software is now layered onto existing digital security cameras at JPS Health Network. If a gun is identified, images are instantly shared with the ZeroEyes Operations Center (ZOC), staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence — including visual description, gun type, and last known location — to the on-site hospital police department as quickly as three to five seconds from detection. Deployment of ZeroEyes The ZeroEyes Research Center has found that nearly 50% of gun violence incidents at healthcare facilities take place within the building-among these incidents, 42% are targeted attacks, while 39% are spontaneous. Although hospitals are entrusted with caring for the victims of gun-related violence, this surge in violent incidents within healthcare facilities has prompted approximately 40 states to enact or strengthen laws regarding violence against healthcare workers. “Hospitals are inherently fast-paced environments where people are already vulnerable, and the size of the JPS facility makes the job of its police force and security teams even more challenging,” said Mike Lahiff, CEO, and co-founder of ZeroEyes. “I personally believe that the hospital’s deployment of ZeroEyes underscores its unwavering commitment to staying ahead of the curve in safety and security while providing exceptional care for its community.”
Healthcare products


Healthcare white papers

Essential Data Security Strategies For Healthcare
Download
The Future Of Healthcare Security Is Connectivity
Download
Verkada Workplace Safety Survey
Download
Securing Care Closer To Patients
Download
Healthcare Surveillance: Finding Efficiencies From OR To ER And Beyond
Download
Intelligent Video Security Solutions
Download
Solve Access Control Challenges in the Healthcare Sector
Download
Using Smart Video Analytics to Improve Operations in Healthcare Facilities
Download
How End-to-End Video Security Solutions Can Help Your Organization With Social Distancing
Download
Thermal Cameras: Can They Accurately Detect Body Temperatures?
Download
The Healthy Market For Video Surveillance At Medical Facilities
Download