Digital Video Recorders
Delta, a global pioneer in power management and a provider of IoT-based smart green solutions announced its participation in the upcoming Advanced Factories 2024 with a showcase under the theme "Connecting Devices, Shaping Solutions." VTScada and the IIoT The exhibit will include the VTScada energy management solution and the IIoT Solution for Industry 4.0. VTScada is a cutting-edge SCADA software that has been supporting the world’s largest mission-critical applications for over three d...
Hikvision, a world-renowned manufacturer and supplier of security products and solutions that deliver the ideal combination of high performance and extreme value, announces the upcoming launch of its new NVR 5.0 Series, the next generation in network video recording technology. Building upon the success of Hikvision NVR innovation, the new NVR 5.0 Series revolutionizes traditional security systems by seamlessly integrating artificial intelligence (AI) and the Internet of Things (AIoT) capabilit...
Multinational companies are tapping the pioneering annual airport industry-dedicated event, set to take place in Dubai, to enter into meaningful networking as the regional airports hunt to acquire the latest technology and innovative services to meet the expectations of the fast-growing air travel market. Airport Show 2024 The 23rd edition of the dedicated B2B platform for the airports industry in the Middle East, North Africa, and South Asia (MENASA) region will be held from May 14&...
Entrust, a global pioneer in trusted payments, identities, and data security announced a single-vendor enhanced authentication solution that integrates identity verification (IDV) and identity and access management (IAM) to fight deepfakes, phishing, account takeover (ATO) attacks and other threats. Identity authentication By enhancing the Entrust Identity as a Service (IDaaS) platform with Onfido’s AI-powered document and biometric verification, customers will be able to deploy ne...
The industrial sector is in need of digital transformation toward greater sustainability and resilience. Value creation and actions for the planet must be brought into balance. Companies need to do more with fewer resources. At Hannover Messe, Siemens will show how proven, cutting-edge technology and strong partnerships enable industries to become both more sustainable and more competitive. Visitors at Booth D53 in Hall 9 will experience showcases featuring core technologies for digital and sust...
Berg Insight, the pioneering IoT market research provider, released a new market study covering the video telematics market. The integration of cameras to enable various video-based solutions in commercial vehicle environments is a massive trend in the fleet telematics sector. Berg Insight’s definition of video telematics includes a broad range of camera-based solutions deployed in commercial vehicle fleets either as standalone applications or as an added feature set to conventional...
News
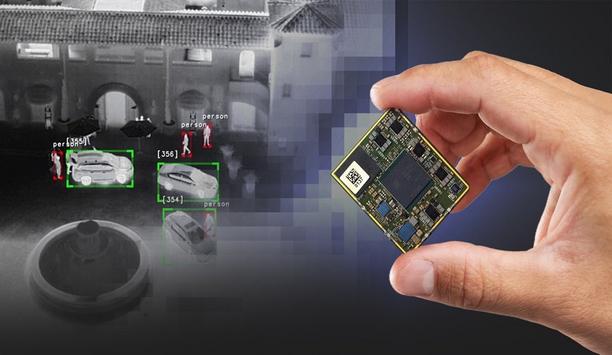
Teledyne FLIR, part of Teledyne Technologies Incorporated announced Teledyne FLIR AVP, an advanced video processor designed to power Teledyne FLIR’s Prism™ AI and computational imaging at the edge. The AVP incorporates the latest Qualcomm QCS8550, the most advanced mobile processor chip from the pioneer in mobile, automotive, and robotics system-on-chip (SoC) technology. AI performance The AVP provides best-in-class artificial intelligence (AI) performance within a small, lightweight, and low-power module for thermal and visible camera integration into unmanned aerial vehicles, robots, small gimbals, handheld devices, and fixed-mounted security systems. AVP runs the Teledyne FLIR Prism AI and ISP software libraries and interfaces with the Boson® and Neutrino® thermal infrared imaging camera modules and a wide range of popular visible cameras. Prism AI and ISP software Prism AI is a powerful perception software designed to detect, classify, and track targets or objects Trained on the world’s largest thermal image data lake of more than 5 million annotations, Prism AI is a powerful perception software designed to detect, classify, and track targets or objects for automotive autonomy, automotive automatic emergency braking, airborne camera payloads, counter-drone systems, ground intelligence, surveillance and reconnaissance (ISR), and perimeter security. Prism ISP is a comprehensive set of image processing algorithms that include super-resolution, image fusion, atmospheric turbulence removal, electronic stabilization, local contrast enhancement, and noise reduction. SWaP-optimized processor “The new AVP is the most powerful and SWaP-optimized processor on the market today, running AI workloads up to five times faster than competitive offerings,” said Dan Walker, vice president of product management, Teledyne FLIR. “The combination of powerful edge computing and our Prism digital solutions ushers in a new era of electro-optical system capabilities while simplifying development and reducing integration risk.” Simplify and streamline development The AVP is designed to empower integrators to build powerful, edge-intelligent products. It is supported by several tools to simplify and streamline development including a Qualcomm RB5 development kit. Software and board-support packages are also available to enable developers to design and fabricate custom interface boards that meet each product’s specific form, fit, function, and input-output (IO) requirements.
Resideo Technologies, Inc., a manufacturer and distributor of technology-driven products and solutions, and Snap One Holdings Corp., a provider of smart-living products, services, and software to professional integrators announced a definitive agreement under which Resideo has agreed to acquire Snap One for $10.75 per share in cash, for a transaction value of approximately $1.4 billion, inclusive of net debt. Upon closing, Snap One will integrate into Resideo's ADI Global Distribution business. Smart living ADI and Snap One will provide integrators with both third-party products and proprietary offerings The transaction will combine ADI's strong position in security products distribution and Snap One's complementary capabilities in the smart living market and innovative Control4 technology platforms, which is expected to drive increased value for integrators and financial returns. Together, ADI and Snap One will provide integrators with an increased selection of both third-party products and proprietary offerings through an extensive physical branch footprint augmented by industry-pioneering digital capabilities. Cost savings “The acquisition of Snap One is an exciting step in Resideo’s continued transformation through portfolio optimization, operational enhancements, and structural cost savings actions,” commented Jay Geldmacher, Resideo’s President and Chief Executive Officer. “ADI and Snap One are highly complementary businesses and together will meaningfully enhance our strategic and operational capabilities as a significant player in attractive growth categories." Residential and commercial applications "We are excited about the enhanced value proposition through increased product breadth, local availability, support services, and broad market expertise, as well as the future opportunities this creates for integrators serving residential and commercial markets." "In addition, the investment by Clayton, Dubilier & Rice is a testament to the strategic and financial merits of this transaction and provides financial flexibility as we continue to transform and optimize our portfolio. We look forward to the ADI and Snap One teams working together to drive value for all stakeholders through executing on the substantial business and financial synergies we see in combining the two businesses." High-quality services and support “Snap One has grown from a startup built by entrepreneurial integrators to an industry pioneer in smart technology, delivering seamless experiences to consumers and high-quality services and support to our integrators,” said John Heyman, Chief Executive Officer of Snap One. “This is the right next step to capture new opportunities to bring our solutions to market. The future of smart living is here. Demand for connected technology products continues to grow, and Resideo is the right owner to drive our expansion. We believe this transaction will deliver compelling value to our stakeholders and will create opportunities for our people and integrator partners.” Strategic acquisition This cross-category expansion will allow the combined organization to materially deepen relationships "We are excited to support Resideo on this highly strategic acquisition and in their ongoing transformation," commented Nathan Sleeper, CD&R's Chief Executive Officer. "I look forward to joining Resideo's Board of Directors and supporting the business as it executes this transaction and the significant opportunity we see available over the coming years." Benefits of the transaction A Strong Position Across Multiple Attractive Categories: The acquisition will combine Snap One's capabilities for smart living integrators with ADI's complementary position in adjacent security product distribution. This cross-category expansion will allow the combined organization to materially deepen relationships with integrators to better serve their customers and expand their businesses. Expansion of Proprietary Offering: The combination is expected to meaningfully accelerate ADI's existing exclusive brands strategy, leveraging Snap One's award-winning proprietary product portfolio and product development expertise while providing broader availability through ADI's network of commercial and residential integrators and omnichannel capabilities. The combined company intends to leverage increased opportunities around innovation to drive value for integrators through a pipeline for proprietary products. Snap One generated 66% of sales from proprietary products in 2023 and these offerings typically carry significantly higher gross margins than third-party products. Enhanced Integrator Value Proposition: ADI's and Snap One's professional integrators will benefit from significant synergy on go-to-market with Snap One's e-commerce expertise and integrator support platforms and ADI's 195 stocking locations and extensive digital capabilities. The combination is expected to create a true omni-channel experience for integrators, simplifying the buying experience and enhancing product availability. Additional opportunity exists to enhance value within the Control4 integrator base through increasing service levels, rapid product fulfillment, and expanding exclusive offerings. Attractive Financial Profile: Transaction financing has been structured to allow Resideo to preserve financial flexibility for future strategic initiatives The transaction is expected to be accretive to Resideo's non-GAAP EPS in the first full year of ownership, with favorable revenue growth and margin profile to ADI and Resideo as a whole. Transaction financing has been structured to allow Resideo to preserve financial flexibility for future strategic initiatives. Transaction details The transaction is valued at approximately $1.4 billion, including the forecasted net debt of Snap One at the closing of approximately $460 million. This represents a 7.4x multiple on Snap One's Adjusted EBITDA for the twelve months ended December 29, 2023, as further adjusted by including Resideo's projected annual run-rate synergies of $75 million. Customary closing conditions The transaction is expected to be completed in the second half of 2024 and is subject to customary closing conditions, including receipt of applicable antitrust and other regulatory approvals. The transaction has been unanimously approved by the Boards of Directors of Resideo and Snap One. Private investment funds managed by Hellman & Friedman LLC, holding approximately 72% of the outstanding common shares of Snap One, have executed a written consent to approve the merger, thereby providing the required stockholder approval for the transaction. Convertible preferred equity investment Terms of the CD&R investment include a 7% coupon, payable in cash or payment-in-kind at Resideo's option Resideo intends to use proceeds from committed debt financing, cash on hand, and a $500 million perpetual convertible preferred equity investment from Clayton, Dubilier & Rice LLC ("CD&R") to fund the transaction. Terms of the CD&R investment include a 7% coupon, payable in cash or payment-in-kind at Resideo's option, and a conversion price of $26.92. CD&R brings a long track record of value creation through its investments and significant experience in the specialty distribution market. Effective upon the closing, CD&R will have the right to designate two members to the Board of Directors of Resideo. Transaction conference call information Resideo will host a conference call at 8:00 a.m. Eastern Time on April 15, 2024, to discuss the transaction. Interested parties may join the call where related materials will be posted before the call, or by phone at 646-968-2525 or 888-596-4144 with the conference ID: 7959274. Resideo preliminary first quarter 2024 financial results For the first quarter ended March 30, 2024, Resideo's preliminary expectations are for revenue of approximately $1,485 million, compared with the outlook of $1,460 million to $1,510 million and Adjusted EBITDA above the midpoint of the outlook of $120 million to $140 million provided in the fourth quarter and full-year 2023 results press release dated February 13, 2024. Resideo intends to release first quarter 2024 financial results after the close of the New York Stock Exchange on Thursday, May 2, 2024, and host a webcast conference call at 5 p.m. ET. Advisors Evercore and Raymond James & Associates, Inc. are acting as financial advisors and Willkie Farr & Gallagher LLP is acting as legal counsel to Resideo. Bank of America and Morgan Stanley have provided committed financing for the transaction and are also acting as advisors to Resideo. Moelis & Company LLC and J.P. Morgan Securities LLC are serving as financial advisors to Snap One and have each provided a fair opinion to Snap One's board of directors. Simpson Thacher & Bartlett LLP is serving as Snap One's legal counsel.
Detection Technology, a global leader in X-ray detector solutions, announces the global availability of a comprehensive range of TFT (thin-film transistor) flat panel detectors. The portfolio includes IGZO (indium gallium zinc oxide) and a-Si (amorphous silicon) technology-based solutions optimized for medical and industrial applications. TFT flat panel detector solutions "We are pleased to start worldwide sales of our TFT flat panel detector solutions as the timing is just right. IGZO is replacing CMOS and a-Si technologies in dental CBCT (cone beam computed tomography) applications for large fields of view, fast frame rates, and excellent low-dose performance,” says Tuomas Holma, Director of Product Management of the Medical Business Unit at Detection Technology. "In turn, in surgical applications, IGZO will replace image intensifiers and offer improved low-dose performance compared to a-Si. We now launch two IGZO detectors for surgical and will expand our portfolio soon to dental applications." CT and line scan solutions "The industrial market is rapidly changing. New requirements are coming in from the automotive industry, especially for the inspection of large castings, electronics, and batteries," says Tomi Fält, Director of Product Management of the Industrial Business Unit at Detection Technology. "We have been pioneers in providing CT and line scan solutions for industrial customers and are now even better positioned to serve them with the addition of TFT flat panel detectors." a-Si detectors "We kick off global sales with a range of dynamic a-Si detectors that provide high resolution, large field of view, fast frame rates, and excellent radiation hardness for inline DR and CT applications." "We are also launching a static a-Si panel for component counting. We are ambitious, and our TFT detector portfolio for industrial is also about to expand." Solutions portfolio At present, the portfolio includes the following sellable items: X-Panel 2323z FDM, a dynamic IGZO X-ray flat panel detector, optimized for mobile C-arms, image intensifier (II) replacement, and cone beam computed tomography (CBCT) X-Panel 3030z FDM, a dynamic IGZO X-ray flat panel detector, optimized for mobile C-arms, medical CBCT, and digital subtraction angiography (DSA) X-Panel 4343a FQI, an a-Si X-ray flat panel detector, optimized for industrial CBCT and non-destructive testing (NDT) X-Panel 2530a FQI-XM, an a-Si X-ray flat panel detector, optimized for battery inspection, in-line digital radiography (DR), and computed tomography (CT) X-Panel 4343a FQI-H, an a-Si X-ray flat panel detector, optimized for high-energy NDT (applications utilizing linear accelerators) X-Panel 4343a FSI, an a-Si X-ray flat panel detector, optimized for component counting. “Our state-of-the-art TFT flat panel offering is rapidly evolving. We have numerous different solutions and their variants in the pipeline, and our portfolio will be further expanded for global sales towards the end of this year.” Availability The TFT flat panels are available for purchase worldwide. Detection Technology will showcase the key features of its X-Panel portfolio at the upcoming exhibitions. The company will be exhibiting medical solutions at the CMEF show in Shanghai, China on 11-14 April, and solutions optimized for versatile industrial applications at the WCNDT show in Incheon, Korea on 27-31 May.
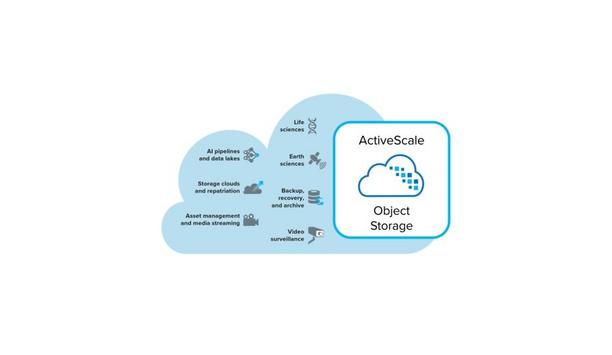
Quantum® Corporation, the pioneer in end-to-end data management solutions designed for the AI era announces ActiveScale® Z200 all-flash object storage to help customers accelerate mission-critical AI pipelines and massive data workflows. This new solution extends Quantum’s all-flash leadership beyond Quantum Myriad™ and StorNext™ file system solutions to address S3-native use cases that require rapid data ingest, high-performance analysis, fast data retrieval, and long-term data preservation for compliance, AI models, and unstructured data management. ActiveScale Z200 Customers gain more agility and speed to build massive data lakes and storage clouds The ActiveScale Z200 appliance expands the award-winning ActiveScale portfolio to include an all-flash option that delivers powerful new levels of throughput and transactional performance at any scale, from terabytes to exabytes. With the ActiveScale Z200, customers gain more agility and speed to build massive data lakes and storage clouds, ingest and prep raw data sets, optimize and run AI pipelines and other data-intensive workflows, and cost-effectively preserve and protect massive data sets. Performance and cost efficiency “AI and other data-intensive business initiatives are driving the need for a simpler, easy-to-access infrastructure that provides both performance and cost efficiency at scale,” says Bruno Hald, vice president of secondary storage for Quantum. “With the introduction of the ActiveScale Z200, we are meeting the need for a fully integrated enterprise object storage solution that merges high-performance scale-out flash and scale-out tape libraries to build data lakes and storage clouds of outstanding scalability, simplicity, performance, and cost efficiency, without compromising data availability and long-term durability." Object storage platform ActiveScale is a simple, reliable scale-out object storage platform built for always-available access and massive scale "With the ActiveScale Z200, our customers can extract even greater value from their digital assets quickly and efficiently.” Quantum ActiveScale is a simple, reliable scale-out object storage platform built for always-available access and massive scale, efficiently storing and protecting billions of objects with pioneering durability. Fueling AI pipelines and data-intensive workflows The all-flash ActiveScale Z200 delivers up to five times greater throughput (gigabytes per second) and up to nine times more transactions (objects per second) over traditional hard drive object storage solutions, dramatically expanding the applicability of ActiveScale to performance-oriented workloads including high-throughput data ingest, AI data preparation, training and inferencing, NoSQL databases, and content streaming. The ActiveScale Z200 enables high-performance analysis of object data sets at any scale to help customers achieve faster insight, discovery, and innovation. The ideal archive storage tier The ActiveScale Z200’s high throughput makes it particularly well-suited for ingesting data ActiveScale is the industry’s only object storage platform architected for both active and cold data, making it uniquely suited for building massive data lakes, storage clouds, and long-term archives at up to 80% lower cost than alternative solutions. The ActiveScale Z200’s high throughput makes it particularly well suited for ingesting data into these large data stores, and with its unique ability to process and densely store metadata in flash for hundreds of billions of objects in the cold storage tier, the Z200 reduces overall footprint and cost. Fast and easy access With fast and easy access through standard S3 Glacier interfaces, objects are easily restored in bulk within minutes for additional analysis, model recalibration, and re-monetization. “The age of AI is upon us. Within our customer base, the desire to extract more value from their massive data assets is real and growing,” says Brent Angle, chief technology officer for Cinesys.io, a leading broadcast and media systems integrator. Data preservation and management "Rapid analysis of content, on the scale of hundreds of petabytes, plus cost-effective management and preservation of this data is essential to meet their objectives." "The ActiveScale Z200 all-flash solution will help our customers optimize their data infrastructure to innovate faster with confidence.” The ActiveScale Z200 all-flash object storage solution is available immediately. The solution is also available as software only and as-a-service.
Global security manufacturer, Gallagher Security, is eagerly preparing to showcase the next evolution of multiple solutions at booth #27099 at ISC West in Las Vegas from April 9-12. Next-gen controller 7000 The Gallagher team will be providing live product demonstrations, answering questions, and sharing details about Gallagher’s future direction with an exciting sneak peek at a new digital wallet solution coming with the next release of Command Center. In particular, the team will be exhibiting the award-winning, Underwriters Laboratory (UL)-certified Controller 7000 (C7000), the first step toward the future of Gallagher’s solutions ecosystem. Cybersecurity C7000 has been built with cybersecurity at its core: the hardware technology integrates security features Capable of managing all localized access control, intrusion alarms, perimeter security, business automation, and logic needs for organizations, the Controller 7000 offers streamlined upgrades and next-generation components that execute decisions faster and support 2 million cardholders. More importantly, the C7000 has been built with cybersecurity at its core: the hardware technology integrates security features at the silicon level while powerful iMX8 System-on chip and an NXP Edgelock secure element provide a Trusted Execution Environment (TEE) and software authenticity on each device. Multiple layers of cybersecurity “People understand that cybersecurity is important, but many businesses don’t realize the immensity of the financial and reputational risks a cyber-physical attack poses until it’s too late,” says Scott Elliott, Executive Vice President of the Americas. “That’s what makes me so excited about the C7000: with multiple layers of cybersecurity baked in, we’re removing some of the complexity of cyber risk management and empowering our customers to protect their people, data, and assets long into the future, and we’re doing it through a device that delivers a faster, smoother access experience.” Security Made Better (SMB) Security Made Better (SMB), a cloud-based solution delivering integrated security in an accessible app format In addition to the C7000, the Gallagher Security booth will also spotlight the latest evolution of Security Made Better (SMB), a cloud-based solution delivering integrated security in an accessible app format. Designed with the same powerful hardware as Gallagher’s enterprise solution, but simplified so anyone can use it, this new era of SMB offers End Users and installers additional functionality and increased value with over 20 new features designed to enhance users’ security experience. Breaking the access and intrusion barriers “Our goal with SMB is to deliver a premium security product without operational complexity,” explains Lisa Tubb, Senior Product Manager for SMB. “We see it as breaking down the barriers of access control and intrusion detection for businesses with elevated security needs, but who don’t need all the bells and whistles of an enterprise system, like childcare facilities, retail stores, restaurants, and other businesses such as law or medical offices.” Command Center v9.10 Command Center v9.10 includes a new digital wallet solution that further expands credential capabilities Visitors to Gallagher’s booth will also be treated to a sneak peek of the next release of Command Center, version 9.10 due in May 2024. With a special focus on mobility, Command Center v9.10 includes a new digital wallet solution that further expands credential capabilities and provides an intuitive and easy access experience. This new digital wallet solution will make its debut at Gallagher’s booth, giving ISC West attendees the chance to be the first to see the new solution in action. Demonstration at the booth “There's never been a more exciting time to visit the Gallagher booth,” says Scott Elliott. “We’ve got a lot we’re looking forward to sharing at ISC West and hope you’ll stop by for a demonstration of what makes Gallagher’s solutions truly unique in the market.” The team will be on-site at booth #27099 throughout the week and invite ISC West attendees to stop by for a chat and a first-hand look at the future of Gallagher Security.
Major UK-based Intruder Detection manufacturer - Texecom is pleased to announce a key addition to their UK sales team with the appointment of a new Head of Commercial Partnerships. Barry Clayton With over 25 years of extensive experience in the security industry, Barry Clayton has joined Texecom in the newly formed role which will see him lead the key customer and technology partnership function to increase support for these stakeholders. Before joining Texecom, Barry held roles in retail internal investigations and physical security, managing multi-million-pound electronic security projects across various sectors, most recently with a national systems integration group. Expertise and skills Commenting on his appointment, Barry Clayton said, “As a British manufacturer with a global footprint, joining Texecom at this stage of our growth journey is a fantastic opportunity." He adds, "I am excited to apply my expertise and skills to demonstrate the benefits of the Texecom suite of solutions within key market sectors utilizing my vast experience, not only from an end-user of security systems perspective but also my experience as a solutions integrator and working for a pioneering security manufacturer." David Mountfield's comment Barry Clayton will report directly to Chief Revenue Officer, David Mountfield, who ssaid “I’m delighted to welcome Barry to the team, his experience speaks for itself. Coupled with our professionally graded solutions and an exciting product roadmap, I am looking forward to working with Barry to support our key customers moving forward.” Barry has already begun meeting with key customers, end-users, and distribution partners and will continue to do so at The Security Event next month where he will be on stand 5/F10 showcasing Texecom’s all-new SmartCom Pro communicator, Digital Services, and intruder detection solutions.


Expert commentary
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realize, however, that some of these traditional security measures are becoming antiquated and no longer cutting. The now and future of overnight security is in remote guarding. Pioneered by companies like Los Angeles-based Elite Interactive Solutions, which was founded back in 2007, remote guarding is revolutionizing the overnight security business. Minimizing criminal activity Remote guarding is fast becoming the most popular choice among commercial end-user property owners Remote guarding utilizes a combination of cutting-edge technology, “digital guards,” highly trained security agents, and local law enforcement if and when necessary to minimize the potential of criminal activity. For those adequately enlightened to its overwhelmingly impressive crime prevention capabilities, remote guarding is fast becoming the most popular choice among commercial end-user property owners to secure and protect their investments. What Is Remote Guarding? Remote guarding is a revolutionary concept and increasing trend in security systems that utilize a combination of methods to effectively analyze potential threats to property. Cameras and/or other monitoring devices running highly advanced algorithmic software are installed in strategic areas or vulnerable places onsite and remotely located security agents are immediately notified of any activity within a designated perimeter of the property. A blend of AI, cybersecurity, and video analytics When properly deployed by an expert provider, the technology stack includes a proprietary blend of video analytics, artificial intelligence, cybersecurity, and more. Done right, “noise” is effectively filtered out, allowing agents to act on legitimate alerts and achieve zero false alarms communicated to first responders. Today, there are a lot of terms and descriptions tossed around about remote guarding, remote video, virtual guarding, etc., but those attributes must be present to represent the true definition of the offering and its many virtues. Realtime situational awareness Many systems have a two-way speaker that allows the security agent to give a verbal warning When specially trained security agents are alerted to trespassers, possible intruders, or other suspicious activity, they analyze the situation in real time and determine the necessary level of action. Many systems have a two-way speaker that allows the security agent to give a verbal warning, known as a voice-down, to the individual(s) that they are being watched. Most perpetrators, often believing the response is emanating directly from security personnel on the property itself rather than from a remote command center, flee immediately. However, if the threat persists, the security agent enlists local law enforcement to get on the scene. Customized remote guarding When properly deployed, remote guarding systems are also customized to specific properties. A team of consultants visits the client’s property to evaluate its vulnerabilities and where to best place cameras and/or other monitoring devices for system efficacy. Traditional Security Shortfalls According to Keith Bushey, a retired commander for the Los Angeles Police Department, there is much frustration between law enforcement officers and potential victims of crime due to the historically unreliable performance of traditional burglar alarm systems and central monitoring stations. He states about 90% of security-related calls are false alarms, a problem that has been well-documented through the years. Onsite challenges When a legitimate emergency does occur, the perpetrators have often already done their damage When a legitimate emergency does occur, the perpetrators have often already done their damage and/or escaped by the time law enforcement arrives. Onsite security guards are not the remedy either as they bring their own set of issues and challenges. Unexpected costs Traditional security systems can also have unexpected costs. The cost is not only in the security guards’ paycheck or the cost of the equipment itself. The cost comes when an actual incident occurs. In worst-case scenarios, the security guard(s) are injured, the business suffers inventory loss, and/or damage is sustained to the property. The medical and other costs for the security guard(s), the loss of inventory, property damage, deployment of law enforcement resources, and possible fallout of legal expenses all add up. Even in the best-case scenario, false alarm expenses incur if law enforcement is dispatched. These, among many others, are some of the primary issues that remote guarding resoundingly answers as a superior alternative. A Bounty of Benefits Remote guarding systems have been proven to cut costs and be more effective than traditional security systems. Even though the monthly monitoring costs of remote guarding are significantly higher than traditional intrusion detection system monitoring, the much higher effectiveness in crime reduction, elimination of false alarms, and augmenting or replacement of manned guards result in a substantially higher return on investment (ROI) to the end user. Easy tracking of threats The security cameras already have their image captured on record, making them easier to track down For example, case studies have demonstrated reduced security costs for clients by 60%, on average. These reductions have come from the costs of security staff, inventory, or property loss, plus saving money on insurance premiums and deductibles. The nature of remote guarding reduces the risk and costs of false alarms, with professional security agents able to determine an actual threat before law enforcement is called. In a rare instance when a perpetrator escapes before law enforcement arrives or can detain the individual(s), the security cameras already have their image captured on record, making them easier to track down and identify. Reduction of false alarms The significant reduction in false alarms is greatly appreciated by law enforcement, as it allows them to focus on real emergencies or crises. Better relationships are also developed between clients and law enforcement, as remote guarding systems are highly reliable in providing accurate and real-time information to officers as they approach the scene. In short, it assists law enforcement in doing their job more effectively, as well as more safely thanks to having eyewitness information before engaging in an active crime scene. Partnership When you combine the decreased cost with the increased efficiency and success rate, it is easy to see why many commercial end-user property owners across the country are making the shift to remote guarding. It’s also an outstanding opportunity for professional security dealers and integrators to partner with a remote guarding services provider to bring a superior solution to their end customers and pick up a recurring monthly revenue stream in the process.
Daniel May of Consort reviews the integration of access control systems in healthcare settings, outlining the benefits and key considerations decision-makers must make throughout product specifications. From patient safety and traversal to the protection of sensitive data and pharmaceuticals, healthcare environments are faced with several operational challenges. And where security remains at the forefront of decision-making, modern access control systems may often hold the answers. Physical security systems Hospitals in particular have developed into multi-faceted spaces that house hundreds to thousands of patients, staff, and visitors at any one time. In England for example, research has found in the three months leading to June 2023, an average of 44,626 people visited major hospital A&E departments each day, with over 16 million attendances typically recorded over the course of a year-not to mention an additional nine million logged at other minor units. For any building, this level of sustained footfall can request severe security difficulties For any building, this level of sustained footfall can invite severe security tests. With that, the need to deploy effective physical security systems in healthcare is clear. And so, as access control continues to become more readily adopted and new products enter the market, decision-makers are reminded to consider the requirements of their building, ensuring they select the solutions most suited to their settings and budget. Security controlled Patient safety will always remain the top priority in healthcare settings, and where matters of health and social care come into question, a diverse set of professional regulatory bodies are tasked with setting and maintaining high standards. When it comes to healthcare premises specifically, patient security and perimeter security often come hand in hand and are amongst the most pressing of challenges that decision-makers must face. To help address operational planning and potential design concerns in the NHS, the Health Building Note (HBN), provides general design guidance for healthcare buildings under HBN 00-01-citing the use of access control measures as a way of maintaining security and protecting the safety of patients, staff, and visitors. Use of access control Hospital buildings control varied levels of access for a number of security purposes Hospital buildings, for example, must control varied levels of access for a number of operational and security purposes. Routine scenarios exist where vulnerable patients are under monitoring and thus refrained from exiting the premises for their own safety, while at the same time, permitted staff must be able to reach their patients and medicines when required. For this, the use of access control is key. Equally, access credentials can also help management teams keep track of those who may be entering or exiting rooms with equipment and pharmaceutical supplies, deterring any unwanted visitors and opportunists in the process. Incorporation of access control systems On a similar note, regulations have set a minimum standard for how personal data should be stored and managed in healthcare environments, giving decision-makers an added responsibility to regulate staff-controlled areas with patient medical records. While instances of personal data breaches are rare, healthcare facilities and professionals are at legal risk should confidential data be found misused or missing. As such, the incorporation of access control systems has become essential in keeping data storage areas secure, with intuitive online systems capable of permitting access to staff with the correct credentials while simultaneously tracking who has requested clearance at digital entry points. HBN guidance Healthcare experts are better fitted to control the sheer volume of people entering and exiting To function effectively, healthcare facilities must always be perceived as safe places by the people who reside within them, and as HBN guidance implies, a unified physical security system can help address key safety and security concerns while enhancing patient and staff experience. Opportunely, access control systems are more accessible and adaptable than ever and combine several technologies such as mechanical locks and automatic doors with electronic access credentials in the form of smartphone apps, badge readers, and biometric scanners. By integrating these systems into the building’s existing infrastructure, healthcare professionals are better equipped to control the sheer volume of people entering and exiting the premises without impairing the general flow of movement and coordination around the facility. Better by design Despite the clear benefits offered to healthcare facilities, there are a number of considerations to be mindful of when choosing an access control solution. Poorly implemented systems can have an adverse effect on security and functionality - quickly costing healthcare organizations time and budget to rectify and replace the inadequate products that don’t meet the building’s requirements. For that reason, decision-makers and design teams are reminded that there is no single solution that fits all healthcare buildings. As such, it’s crucial for decision-makers to understand the systems that are being put in place throughout each of the touchpoints in their facility. Clear collaboration is required during periods of specification, where together, teams can ensure the selected product works on all angles, from meeting fire safety and sustainability standards to aesthetics and scalability. Modern access control products Scalability is a key area that decision-makers must review when selecting access control systemsFrequently overlooked, scalability is a key area that decision-makers must review when selecting access control systems. Such is their diverse nature; healthcare facilities can often change and develop as years go by, and by selecting a system that facilitates growth, such as a cloud-based solution-security and efficiency is long-established. While modern access control products are known for seamless integration, there are some systems that may restrict the ability to use different vendors throughout the remainder of the building’s infrastructure. This, in effect, causes a monopolization of products throughout the estate, which can have an adverse effect on growth by increasing costs and reducing the levels of service associated with the security system already in place. Improve security and safety A scalable and reliable access control system will continue to improve security and safety by adapting to a building’s new requirements-and all while having minimal impact on its operational network. And so, while technology will no doubt continue to influence and transform the access control market, healthcare facilities and their professionals must continue to remain educated on their own systems, ensuring they have the best options in place to keep their patients, staff, and visitors safe and secure for years to come.
Global transportation networks are becoming increasingly interconnected, with digital systems playing a crucial role in ensuring the smooth operation of ports and supply chains. However, this reliance on technology can also create vulnerabilities, as demonstrated by the recent ransomware attack on Nagoya Port. As Japan's busiest shipping hub, the port's operations were brought to a standstill for two days, highlighting the potential for significant disruption to national economies and supply chains. Transportation sector The attack began with the port's legacy computer system, which handles shipping containers, being knocked offline. This forced the port to halt the handling of shipping containers that arrived at the terminal, effectively disrupting the flow of goods. The incident was a stark reminder of the risks associated with the convergence of information technology (IT) and operational technology (OT) in ports and other critical infrastructures. This is not an isolated incident, but part of a broader trend of escalating cyber threats targeting critical infrastructure. The transportation sector must respond by bolstering its defenses, enhancing its cyber resilience, and proactively countering these threats. The safety and efficiency of our transportation infrastructure, and by extension our global economy, depend on it. Rising threat to port security and supply chains XIoT, from sensors on shipping containers to automatic cranes, are vital to trendy port functions OT, once isolated from networked systems, is now increasingly interconnected. This integration has expanded the attack surface for threat actors. A single breach in a port's OT systems can cause significant disruption, halting the movement of containers and impacting the flow of goods. This is not a hypothetical scenario, but a reality that has been demonstrated in recent cyberattacks on major ports. Adding another layer of complexity is the extended Internet of Things (XIoT), an umbrella term for all cyber-physical systems. XIoT devices, from sensors on shipping containers to automated cranes, are now integral to modern port operations. These devices are delivering safer, more efficient automated vehicles, facilitating geo-fencing for improved logistics, and providing vehicle health data for predictive maintenance. XIoT ecosystem However, the XIoT ecosystem also presents new cybersecurity risks. Each connected device is a potential entry point for cybercriminals, and the interconnected nature of these devices means that an attack on one, which can move laterally and can have a ripple effect throughout the system. The threat landscape is evolving, with cybercriminals becoming more sophisticated and their attacks more damaging with a business continuity focus. The growing interconnectivity between OT and XIoT in port operations and supply chains is also presenting these threat actors with a greater attack surface. Many older OT systems were never designed to be connected in this way and are unlikely to be equipped to deal with modern cyber threats. Furthermore, the increasing digitization of ports and supply chains has led to a surge in the volume of data being generated and processed. This data, if not properly secured, can be a goldmine for cybercriminals. The potential for data breaches adds another dimension to the cybersecurity challenges facing the transportation sector. Role of Cyber Resilience in Protecting Service Availability Cyber resilience refers to organization's ability to prepare for, respond to, and recover from threats As the threats to port security and supply chains become increasingly complex, the concept of cyber resilience takes on a new level of importance. Cyber resilience refers to an organization's ability to prepare for, respond to, and recover from cyber threats. It goes beyond traditional cybersecurity measures, focusing not just on preventing attacks, but also on minimizing the impact of attacks that do occur and ensuring a quick recovery. In the context of port operations and supply chains, cyber resilience is crucial. The interconnected nature of these systems means that a cyberattack can have far-reaching effects, disrupting operations not just at the targeted port, but also at other ports and throughout the supply chain. A resilient system is one that can withstand such an attack and quickly restore normal operations. Port operations and supply chains The growing reliance on OT and the XIoT in port operations and supply chains presents unique challenges for cyber resilience. OT systems control physical processes and are often critical to safety and service availability. A breach in an OT system can have immediate and potentially catastrophic physical consequences. Similarly, XIoT devices are often embedded in critical infrastructure and can be difficult to patch or update, making them vulnerable to attacks. Building cyber resilience in these systems requires a multi-faceted approach. It involves implementing robust security measures, such as strong access controls and network segmentation, to prevent attacks. It also involves continuous monitoring and detection to identify and respond to threats as they occur. But perhaps most importantly, it involves planning and preparation for the inevitable breaches that will occur, ensuring that when they do, the impact is minimized, and normal operations can be quickly restored. Building resilience across port security and supply chains In the face of cyber threats, the transport sector must adopt a complete method of cybersecurity In the face of escalating cyber threats, the transportation sector must adopt a comprehensive approach to cybersecurity. This involves not just implementing robust security measures, but also fostering a culture of cybersecurity awareness and compliance throughout the organization. A key component of a comprehensive cybersecurity strategy is strong access controls. This involves ensuring that only authorized individuals have access to sensitive data and systems. It also involves implementing multi-factor authentication and regularly reviewing and updating access permissions. Strong access controls can prevent unauthorized access to systems and data, reducing the risk of both internal and external threats. Network segmentation Network segmentation is another crucial measure. By dividing a network into separate segments, organizations can limit the spread of a cyberattack within their network. This can prevent an attack on one part of the network from affecting the entire system. Network segmentation also makes it easier to monitor and control the flow of data within the network, further enhancing security. Regular vulnerability assessments and patch management are also essential. Vulnerability assessments involve identifying and evaluating potential security weaknesses in the system, while patch management involves regularly updating and patching software to fix these vulnerabilities. These measures can help organizations stay ahead of cybercriminals and reduce the risk of exploitation. EU’s NIS2 Directive EU’s NIS2 Directive came into effect, and member states have until October 2024 to put it into law The transportation sector must also be prepared for greater legislative responsibility in the near future. The EU’s NIS2 Directive recently came into effect, and member states have until October 2024 to put it into law. The Directive aims to increase the overall level of cyber preparedness by mandating capabilities such as Computer Security Incident Response Teams (CSIRTs). Transport is among the sectors labeled as essential by the bill, meaning it will face a high level of scrutiny. Getting to grips with the complexities of XIoT and OT integration will be essential for organizations to achieve compliance and avoid fines. Global transportation infrastructure Finally, organizations must prepare for the inevitable breaches that will occur. This involves developing an incident response plan that outlines the steps to be taken in the event of a breach. It also involves regularly testing and updating this plan to ensure its effectiveness. A well-prepared organization can respond quickly and effectively to a breach, minimizing its impact and ensuring a quick recovery. In conclusion, mastering transportation cybersecurity requires a comprehensive, proactive approach. It involves implementing robust technical measures, fostering a culture of cybersecurity awareness, and preparing for the inevitable breaches that will occur. By taking these steps, organizations can enhance their cyber resilience, protect their critical operations, and ensure the security of our global transportation infrastructure.
Security beat
Companies at GSX 2023 emphasized new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasizes ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the Mid-Market to the Cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for pure cloud, but there are benefits to be realized from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realize the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘Soft’ Features for Integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organization more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organization more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centers around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasizing performance, protection (cybersecurity), and price, their data centers are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring center where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
A pioneer in the access control sector since 1971, AMAG Technology is looking to the future and the next generation of products that will expand its services to customers. “In our vision, we have advanced approaches that will not only provide our partners with advanced technologies but also ones that are easier to install with tools to expand their services,” says David Sullivan, who was appointed President of the venerable access control company in September 2022. New challenges at AMAG Sullivan brings a new outlook to the AMAG business, a part of Allied Universal, and a new vision to lead the company into the future. We caught up with David Sullivan to discuss his new challenges at AMAG and the journey ahead as the company looks to the future. Q: How does your background inform your approach to leading AMAG? I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry David Sullivan: With the exception of only a few short years, my career has been in access control. I have experience with several systems and have had the privilege to manage several successful access control companies. As a result, I bring a great deal of experience into my role at AMAG. I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry. Q: How would you describe AMAG’s journey over the last several years and how do you see the future? Sullivan: Prior presidents of AMAG always shared their leadership vision and direction with senior leaders located in the United Kingdom. This had an impact on the full direction of the business, sometimes limiting its ultimate success. Before I became a part of AMAG, these senior leaders that were located in the UK retired, placing for the first time the full management responsibilities of the president. This has allowed me to integrate the business into a single team, with single objectives, and a single vision. We expect to begin to reveal this new vision in the coming weeks. We are excited about the future of AMAG and believe we will surprise the industry with our new products and approach in the coming months and years. Q: How important is it that a manufacturer provides both hardware and software solutions? How does AMAG’s approach (in general) differentiate it in the market? We can design the complete solution, providing functionality that others may find more difficult to accomplish Sullivan: Regardless of the manufacturer, we all provide hardware and software. An access control solution is not complete without both. Some of us choose to make our panels, and others do not. Those who are dependent on third-party suppliers are restricted to the developments and direction of that company, and while it might be perceived to be an open technology, it still is proprietary to the hardware manufacturer. AMAG has controlled its manufacturing of panels from day one. The result means that we can design the complete solution, providing functionality that others may find more difficult to accomplish. Q: How does the breadth of AMAG’s product suite provide advantages to customers and/or integrators? Sullivan: AMAG’s product portfolio is unique and provides the end user with an end-to-end identity management solution from one company. Our Control Room PSIM, Symmetry CONNECT Identity Management Solution, Symmetry Access Control, and Symmetry GUEST solutions all integrate to provide the user with a broad set of features and capabilities from a single provider. There is no finger-pointing when we come to support your system. We hold full responsibility for making it work and can quickly provide a resolution to any application difficulties the user may be experiencing. Q: How does AMAG address the divide between on-prem and cloud systems? How do you help customers make the transition and/or plan for the future? We are in the early stages of developing our next generation of access control in which we intend to provide on-prem Sullivan: In our current product portfolio, we have three products that are cloud-based. Our mobile credential platform (Symmetry Mobile), our visitor management solution (Symmetry GUEST), and our physical identity and access management solution (Symmetry CONNECT) are all offerings that operate in the cloud. We are in the early stages of developing our next generation of access control in which we intend to provide on-prem, web client, and cloud-based offerings. One of the primary objectives is to ensure that the large installed base of systems that are out there today will be able to migrate not only to our next generation but as well to the cloud if the client so desires. Q: What is AMAG’s approach to mobile credentialing? Sullivan: As an access control provider, adding Symmetry Mobile credentialing to our portfolio just made sense. We want our customers to have a forward-thinking solution with the opportunity to save money not only on the physical badges but the cost of printing and distributing badges. Mobile credentials can be easily issued and revoked remotely, reducing administrative overhead, and eliminating the need for physical inventory management. Organizations can centrally configure what devices are used and the read range for each type of device and operating system, thus providing flexibility. Symmetry Mobile offers a customized questionnaire that controls access and reduces liabilities. Q: What has surprised you the most in your first year or so leading AMAG? Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company Sullivan: I wouldn’t say I was surprised by this as much as happy to see, but I would say that the quality of our people was a pleasant surprise. As well, the AMAG product offering is broad and has some unique elements. When coupled with the depth of the resources that we have in AMAG, I know that we are second to none. Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company that has so many talented people. Q: Please describe your dealer channel, and how you are seeking to expand it. Sullivan: The AMAG products are sophisticated and typically are installed for higher-end applications. With this sophistication comes a need to be well able to install such a solution. We have a strong group of certified and loyal partners who help us to deliver these enterprise solutions. We desire to provide our existing partners with updated and competitive systems to offer to their end users. Q: What is the security industry’s (and/or AMAG’s) biggest challenge in the next five years? We need to find ways to provide both our channel partners and the customers with solutions that are easily integrated Sullivan: I believe that the advancements that we are seeing in technology provide our industry with the opportunity to truly change how security is provided to our collective customers. As we advance these solutions, we will need to do so responsibly and in a way that helps the channel’s abilities. We need to find ways to train our partners to both install and support these more complex solutions. At the same time, we need to find ways to provide both our channel partners and the customers with solutions that are easily integrated, moving away from proprietary closed systems to open and cohesive solutions. This will ensure that the users get the best, and most complete solutions. Q: What does the industry as a whole misunderstand about AMAG -- time to set the record straight! Sullivan: Well, I am not ready to openly share where we are heading. We are in the process of putting together some advanced approaches to how we will do business with our partners. We are focused on providing tools that will enhance their services to their customers, and with products that are leading edge. I can only state that all should keep their eyes on AMAG, because over the next few years, we are going to surprise some people, and more importantly make our loyal partners quite powerful.
New buzzwords were abundant in the articles that generated the most clicks on our website in 2022. From the metaverse to the Internet of Things, from frictionless access control to artificial intelligence (AI), the topics most popular among our site’s visitors were at the cutting edge of change and innovation in the physical security marketplace. Here is a review of the Top 10 Articles of 2022, based on reader clicks, including links to the original content: Metaverse will promote collaboration and enable more efficiencies for security Metaverse is a familiar buzzword currently, but few people grasp what it means. In the simplest terms, the metaverse is an online “place” where physical, virtual, and augmented realities are shared. The term, Metaverse, suggests a more immersive online environment that combines elements of augmented reality (AR) and virtual reality (VR). For the physical security industry, the looming creation of a complex online environment offers possibilities and challenges. Establishing identity will be a central principle of the metaverse, and various biometrics are at the core of ensuring the identity of someone interacting in the virtual world. Cybersecurity elements are also key. On the benefits side, the security market is already taking advantage of technologies related to the eventual evolution of the metaverse. For example, the industry has deployed AR to provide information about a door lock’s status on a screen, headset, or smart glasses as a patrolling guard walks by. What are the security challenges of the transportation industry? Because transit agencies rely on several IoT devices, they get exposed to higher cybersecurity risks Rapid technological advancement, increasing urbanization, and the growing expectations of commuters and governments are pressuring transit industry players to modernize. Commuters, urban planners, first responders, and other stakeholders want to use transit data to support their decision-making. Transit agencies’ security and operations teams need closer collaboration to stay ahead. However, for many years, most transit agencies have relied on siloed, proprietary systems. Because transit agencies rely on an ever-growing number of Internet of Things (IoT) devices, they also get exposed to higher cybersecurity risks as there are more network access points to manage. The future is here: ADT’s innovation lab evaluating robots and indoor drones New robots and indoor drones for security applications are on the horizon, based on the work of ADT Commercials’ Innovation Lab, which is evaluating the latest technologies’ value to customers and some typical use cases. The ideal use of humanoid robots is to perform jobs that are considered repetitive, dirty, dangerous, and/or mundane. In security, that describes most security guard positions. As the name implies, autonomous indoor drones are focused on flying indoors versus the outdoor environment, which is heavily regulated by the U.S. Federal Aviation Administration (FAA). Flying autonomously indoors not only eliminates FAA oversight but also will enable ADT Commercial to offer another choice to customers to further reduce their dependencies on and costs of human guards. Innovative security: the key to business efficiency, cost savings, and more Organizations have shifted business focus countless times since the onset of the pandemic. While many leaders have been primarily concerned with the immediate health and safety of their customers and employees, 2022 has given rise to a new trend. More than ever, business leaders are seeking security solutions that increase operational efficiency and cost savings as well as improve logistics and business insight. As working environments become more complex, organizations looking to drive higher productivity and profitability margins should consider security upgrades that prioritize integrated analytics and automation. Shoplifting today is more sophisticated, and so are the tools to fight it One tool to fight shoplifting is analytics, which can be used to determine where shrink is occurring Shoplifting is often viewed as petty theft by individuals, but that is not always the case. Overall, shoplifting is becoming more sophisticated and coordinated. Traditional “shoplifting” has two major differences when compared to organized retail crime (ORC). The differences are numbers and motivation. ORC consists of groups working together to monetize theft, very different than an individual taking an item they need. One tool to fight to shoplift is analytics, which can be used to determine where shrink is occurring. Understanding where crimes take place helps retailers make strategic decisions about where to place their loss prevention efforts. Oosto offers 10 reasons to switch to frictionless access control in commercial buildings Access control for buildings is nothing new. It’s only in recent years that the urgency to implement smarter, more efficient, and more convenient forms of access control has increased, in the context of public and private sector digital transformation. Upheavals from the COVID-19 pandemic have forced organizations to re-think, pivot, and invest in new technology solutions that will incorporate Artificial Intelligence (AI) and Machine Learning, to gain speed in their operations, glean actionable insights from their video analytics, and enhance productivity with their teams. Which security trend is here to stay? Technologies and trends in the security marketplace come and go with some regularity. But how can you tell which trends are gaining traction and which amount to “the flavor of the month.” For example, while many physical security departments were hesitant to consider cloud-connected solutions in the past, they now better understand the benefits these solutions bring and how they can help them utilize their resources to achieve business goals while minimizing overall operational complexity. Other technologies mentioned in the article include mobile credentials, AI-based analytics, video management systems, cybersecurity, and a new emphasis on data. What do these technology trends have in common? They are opening new possibilities for greater system efficiency and functionality. In short, they are playing a role in transforming our industry. GSX 2022 reflects changing technologies and evolving role of security The role of the security director increasingly will encompass facets of cybersecurity and physical security GSX 2022 in Atlanta highlighted the changing role of security in the enterprise. The role of the security director increasingly will encompass facets of cybersecurity as well as physical security. Transitioning to an operation that incorporates both disciplines requires a workforce that embraces education and building new skills. Education and the opportunity to build new skills are evident everywhere at GSX, including in the hundreds of education sessions and also in the knowledge shared on the show floor in the exhibit hall. Consolidation changing the face of the security market Consolidation is a dominant trend in the security marketplace. Large companies typically swallow up smaller companies as a means of expanding both their technology portfolios and their geographic reach. Sometimes a big fish is swallowed up by an even bigger fish. Despite the pandemic and resulting economic challenges, the security market has continued to be a desirable environment for both big players and startups, which then provide abundant acquisition targets for larger companies. This article highlighted recent mergers and acquisition news. Six trends at the intersection of video and AI Video has evolved beyond the capabilities of advanced imaging and performance to include another level: Artificial Intelligence. Video imaging technology combines with AI, delivers a wealth of new data, not just for traditional physical security applications, but for a much deeper analysis of past, present, and even future events across the enterprise. This is more than a big development for the physical security industry; it is a monumental paradigm shift that is changing how security system models are envisioned, designed, and deployed. Much of the heightened demand for advanced video analytics is being driven by six prevalent industry trends.
Case studies
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the U.S. Department of Homeland Security SAFETY Act Designation, announced that its proactive gun detection and intelligent situational awareness solution will be deployed at Appomattox County Public Schools (ACPS), Virginia to protect students and faculty against gun-related threats. ACPS Comprising four schools - a primary, elementary, middle, and high school - ACPS educates approximately 2,500 students annually. With a commitment to fostering a safe and nurturing learning environment for all students, the school has implemented several security measures in recent years. These include assigning individual School Resource Officers (SROs) to each school, facilitating comprehensive walkthroughs of all facilities by local and state law enforcement, installing exterior door alarms and student computer monitor software, and enhancing its after-hours surveillance system. ZeroEyes will be the latest addition to this multilayered security approach. School safety “School safety is of the highest priority right now, and to have a technology that could potentially save a life or stop a threat before anything happens made ZeroEyes a no-brainer for us,” said Philip Amos, Supervisor of Security and Technology, Appomattox County Public Schools. ZeroEyes' AI gun detection and intelligent situational awareness software layers onto existing digital security cameras. ZeroEyes Operations Center If a gun is identified, images are instantly shared with ZOC staffed 24/7/365 by specially trained U.S. military If a gun is identified, images are instantly shared with the ZeroEyes Operations Center (ZOC), staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence including visual description, gun type, and last known location to local law enforcement, SROs, and ACPS staff as quickly as 3 to 5 seconds from detection. Swift and accurate security communications "In the instance of a gun-related threat, first responders and school leadership must receive swift and accurate security communications to help them navigate the potentially deadly situation,” said Mike Lahiff, CEO and co-founder of ZeroEyes. “We are proud that ZeroEyes has been chosen to provide this type of situational awareness to Appomattox County Public Schools. Their proactive stance against gun violence is truly commendable."
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the U.S. Department of Homeland Security SAFETY Act Designation, announced that its proactive gun detection and intelligent situational awareness solution has been deployed by Michigan’s Pontiac School District (PSD) to protect students and faculty against gun-related threats. Pontiac School District (PSD) PSD includes nine schools and takes pride in offering its students work-based learning opportunities in industries such as Health Sciences, Business/Finance, and Hospitality/Tourism. The district is also at the forefront of security innovation, adding ZeroEyes to a multi-layered approach that includes a visitor check-in system, smart sensors, and video management software, among others, to provide a safe and secure educational environment. Enhance security and safety “At Pontiac, we've dedicated significant resources to fostering opportunities for students, and we've witnessed the positive impact rippling throughout our community,” said Dr. Kimberly Leverette, Interim Superintendent of Pontiac School District. Dr. Kimberly Leverette adds, “Our mission is to cultivate our schools as safe havens, and with ZeroEyes, we can enhance security and safety both during and after school hours.” AI gun detection and intelligent situational awareness software If a gun is identified, images are instantly shared with the ZOC, staffed 24/7/365 by specially trained U.S. military ZeroEyes' AI gun detection and intelligent situational awareness software layers onto existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Center (ZOC), staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence including visual description, gun type, and last known location to local law enforcement and PSD staff as quickly as 3 to 5 seconds from detection. Gun-related violence “In the past few years, the state of Michigan has experienced great hardship when it comes to gun-related violence,” said Mike Lahiff, CEO of ZeroEyes. He adds, “Pontiac School District continues to show its dedication to safety and eye for innovation with its deployment of ZeroEyes.”
The desire to improve the quality and efficiency of the technologies for post-match press conferences has seen an increasing number of sporting arenas investing in their press facilities. The recently completed new stadium in the city of Tizi Ouzou, Algeria, is a venue that has made this a priority right from the start, with the installation of a CCS 1000 D Digital Discussion System and an Integrus Wireless Language Distribution System from Bosch Building Technologies. UEFA equipment standards The 50,000-seat stadium is the new home of Algeria’s most successful football club, JS Kabylie, and has been built to exacting UEFA standards. This included all the press and broadcast infrastructure and meant that a high-quality press conference solution was demanded from the outset. Partnership with Atempo for audio solutions The company understands exactly what is required to meet the intricacies of UEFA standards New Stadium of Tizi Ouzou called on Turkish Bosch partner Atempo to design the solution for the press conference room, along with the rest of the audio systems for the venue. The company has worked on a variety of stadium projects and understands exactly what is required to meet the intricacies of UEFA standards, while also allowing a venue the flexibility to host non-sporting events. Customized conference technology for flexible deployment CCS 1000 D Digital Discussion System The stadium required a press conference solution that would offer high-quality sound and the flexibility to meet changing needs all with a modern and stylish design. The CCS 1000 D Digital Discussion System met these needs thanks to its compact size, easy set-up, and user-friendly operation, together with advanced features and versatility. Designed especially for quick, plug-and-play installation, it is a dedicated solution for small to medium-sized meeting areas, making it a perfect fit for the press conference room. Integrus Wireless Language Distribution System The solution met all the requirements of the stadium officials for a portable solution The Integrus Wireless Language Distribution System completes the installation, featuring 50 pocket receivers for the press representatives for simultaneous translation into eight languages. The solution met all requirements of the stadium officials for a portable solution that could be used in different configurations according to the needs of stadium officials. Clear and intelligible audio experience “The Bosch conference system presents a solution that fits exactly the requirements in the press areas of stadiums,” states Erhan Yılmaz, Technical Manager at Atempo. Erhan Yılmaz adds, “Bosch's high-quality microphone technology ensures a clear and intelligible audio experience. The Bosch conference system can adapt quickly to different events and needs. With its stylish and modern design, it adds prestige to the press area. Bosch's quality products ensure trouble-free and flawless press conferences.”
On Saturday, the 27th Of January, 2024 an intoxicated man managed to gain access to The Indira Gandhi International Airport’s runway, he was soon after arrested on the tarmac of the runway by the Central Industrial Security Force and then handed to the New Delhi police force. Luckily this man was only drunk, what if he was a determined criminal or even worse a terrorist, think about what damage could have happened in the time between the perimeter being breached and by the time he was arrested. Airport perimeter security deficiencies This starkly illustrates the glaring deficiencies in airport perimeter security, underscoring the urgent need for businesses and proprietors to prioritize this aspect. Perimeter security serves as the first line of defense against unauthorized access, theft, and all threats With such lapses evident in major airports globally, it serves as a compelling reminder of the vulnerability that extends to all. Perimeter security serves as the first line of defense against unauthorized access, theft, and all threats to physical and digital assets. It establishes a boundary, safeguarding critical infrastructure, sensitive information, and personnel. APS Electro-Fence and Flexiguard By deterring intruders and providing early detection, it mitigates risks, enhances safety, and preserves the integrity of protected areas. Advanced Perimeter Systems provides a variety of different perimeter security systems to help prevent events such as this from happening, APS Electro-Fence and Flexiguard would have prevented this from happening.
In Neuss, Düsseldorf, and Meerbusch, ISR (International School on the Rhine) offers an excellent international education from kindergarten to grade 12. The teachers at ISR prepare students for the world's most prestigious universities, placing great emphasis not only on academic excellence but also on positive character development and the teaching of values. Since 2022, ISR has also been using the DeepHub whiteboard for this purpose. Test phase from 2022 "The modernization of classrooms and the additional digitalization of teaching methods are important concerns for us," explains Peter Soliman, Managing Partner of ISR. “Dahua's DeepHub whiteboard offers us versatile functionalities and the perfect solution for our needs.” Mohammed Aloof, Head of IT at ISR, adds, "We have already deployed the DeepHub whiteboards in some classrooms since 2022. The feedback we have received from teachers and our students has been extremely positive. Therefore, we have decided to install a more modern whiteboard in every classroom for even better learning conditions.” Improved visibility and interaction Students can read the text on the screen very well from all angles of the classroom The new whiteboards have significantly improved the visibility of the learning content. Students can read the text on the screen very well from all angles of the classroom. Due to the optimized brightness of the screen, classrooms no longer need to be darkened. "Being able to add handwritten information to documents on the whiteboard adds a lot of value for me," adds Bianca McLeod, a teacher at ISR and head of secondary education. Whiteboard function "The sensitivity here is just right. For example, I can also call up pre-made geometric shapes and use them for lessons. The whiteboard function allows me to save the pages afterward and call them up again at any time. The students can save the learning content by scanning a QR code." "Our teachers can also upload and use extensive materials and teaching aids on DeepHub, which is very practical and accommodates an increasingly paperless and thus environmentally friendly aspiration at ISR." DeepHub This two-way sharing system between DeepHub and the students' tablets is particularly practical Classroom interaction is also further encouraged with the DeepHub. For example, teachers encourage students to participate directly via the whiteboard and answer the quiz displayed on the DeepHub screen. This two-way sharing system between DeepHub and the students' tablets is particularly practical and allows for innovative and interactive teaching. More engaged and proactive "After almost a year of experience with DeepHub, I have noticed a positive change in my teaching," Ms McLeod points out. "The students have become more engaged and even more proactive. We are convinced that further upgrading of the screens will bring even more benefits!" Administration work is simplified The head of the IT department at ISR, Mr. Aloof, is also satisfied, "The Dahua DeepHub makes administration very easy." "A highly modern DeepHub device now replaces the old equipment, projector, speakers, microphone, countless cables, and much more. It makes the management work much easier." Clever all-in-one solution 4K 3840×2160 touch UHD display with a screen diagonal of 65 to 98 inches and a 178° viewing angle The DeepHub whiteboard ensures excellent presentation experiences and creative ideation by allowing participants to fully concentrate on the task at hand without having to worry about technical aspects. In doing so, its 4K 3840×2160 touch UHD display with a screen diagonal of 65 to 98 inches and a 178° viewing angle, combined with anti-glare technology, ensures a clear, more legible display, sharp images, and vivid colors. One-touch projection One-touch projection from up to four terminals via the USB wireless screen sharing dongle or eshare software simplifies collaborative presentations. In training situations and the classroom, knowledge can be conveyed intuitively and with fun in this way. At the same time, as part of a quality control process, other teachers, as well as academic coordinators, have the opportunity to participate in lessons from any location with internet access, even if they are not on-site, due to the interactive features. High-quality, interactive touchscreen The integrated camera (up to 5MP) and up to eight microphones enable powerful video conferencing The touch-active screen supports an optimal writing experience: Smooth writing works virtually in real-time with less than ten ms latency. Responses to touch and support for simultaneous writing vary depending on the application. The integrated camera (up to 5MP) and up to eight microphones enable powerful video conferencing. Due to its high audio and video quality, the Dahua interactive whiteboard is also suitable for seminars, business negotiations, and training. Compatibility Of course, comprehensive compatibility is also taken care of: the pre-installed Android and an optional Windows operating system enable the use of a wide range of productivity tools. This makes perfect sense, as dual operating systems offer a wide range of apps and software. The device is also compatible with popular third-party video conferencing software. Its competitive price and a three-year warranty ensure a high return on investment. In addition, the integrated Android as well as an optional Windows operating system ensure full compatibility with numerous teaching and learning programs. Conclusion "ISR has many Dahua products in use. In the past, our security system, but now state-of-the-art interactive whiteboard technology in all classrooms. We are grateful for the support from a global pioneer in technology and IoT solutions," explains Peter Soliman. He concluded, "I am convinced that the new technology will add great value to ISR's students."
Central Community College in Nebraska has multiple campuses and educational centers to serve approximately 90 different communities. CCC’s outdated lock-and-key system and access control technology weren’t meeting their security needs. On one campus alone there are 26 buildings with access control needs for students, staff, and vendors. The security team had to provide targeted, scheduled access control for about 15 different user groups. The choice We’re completely satisfied with Brivo, as it can scale to whatever and wherever we need" “From experience, we know that great technical support, customer service, and quick turnaround time is important," Ed Long, Physical Plant Director, Central Community, brivo.com. "We’re completely satisfied with Brivo, as it can scale to whatever and wherever we need. The learning curve was short and sweet.” The change The Brivo system allows CCC to continue to scale its access control across facilities. The system allows for creating and managing hundreds of groups with different access privileges. Dorms are locked 24/7 with controlled access to provide a high level of security for students. An extra measure of security is provided with limited-access holiday scheduling. The team can provide controlled access for vendors to come and go from different buildings. The system provides the confidence that CCC has an effective emergency plan in place.


Products


Round table discussion
Technology can be a powerful tool, but it can also be misused. Ethical principles help ensure that technology is used in a way that minimizes risks and avoids causing harm to people or society. Issues could include factors such as data privacy and algorithmic bias of certain technologies. As the security industry embraces advanced and evolving technologies, we asked this week’s Expert Panel Roundtable: What are the biggest ethical considerations of using emerging technologies in physical security?
Technological leaps in the last several decades have revolutionised biometrics. The technologies are constantly evolving, spanning facial recognition to iris scanning to fingerprints, to provide new levels of security and convenience. Biometrics are everywhere, from smartphones to border control, constantly evolving to meet the needs of our increasingly digital world. They are also more accurate and easier to use than ever. We asked this week's Expert Panel Roundtable: What’s new with biometrics?
In today's interconnected world, the lines between physical and digital security are blurring. This means that threats can easily exploit vulnerabilities in both realms, potentially causing significant damage. That's why the convergence of cyber- and physical security systems is becoming increasingly important. It has already been a topic of discussion in the security market for more than a decade. To get a reality check, we asked this week’s Expert Panel Roundtable: Has convergence been achieved in security systems? Why or why not?
White papers
Simple Security Solutions for SMBs
Download
Security Investments Retailers Should Consider For Their 2021 Budget
Download
Understanding Video Management Systems
Download
H.265 High Efficiency Coding: Video Compression For Security Applications
Download
Innovative Edge Storage Solutions For The Video Surveillance Industry
Download
Enhanced Ethernet Technology (ePoE)
Download

Videos
Digital Video Recorders: Manufacturers & Suppliers
- Dahua Technology Digital Video Recorders
- Hikvision Digital Video Recorders
- Honeywell Security Digital Video Recorders
- Vicon Digital Video Recorders
- Hanwha Vision Digital Video Recorders
- Bosch Digital Video Recorders
- eneo Digital Video Recorders
- MobileView Digital Video Recorders
- LILIN Digital Video Recorders
- Dedicated Micros Digital Video Recorders
- DALI Digital Video Recorders
- Genie CCTV Limited Digital Video Recorders
- LTV Europe Digital Video Recorders
- Messoa Digital Video Recorders
- 360 Vision Digital Video Recorders
- Everfocus Digital Video Recorders
- artec Digital Video Recorders
- Visionhitech Digital Video Recorders
- Vanderbilt Digital Video Recorders
- Ganz Digital Video Recorders

Multi-Residential Access Management And Security
Download
Guide For HAAS: New Choice Of SMB Security System
Download
Precision And Intelligence: LiDAR's Role In Modern Security Ecosystems
Download
Hikvision: Solar Powered Product Introduction + HCP
Download
Facial Recognition
Download