Especially for younger individuals, sharing on social media is almost an automatic reflex. Bystanders at any event are likely to constantly be tweeting and/or posting real-time words, pictures and video using their smart phones. Accessing a culmination of that data can provide real-time intelligence of what’s happening on the ground at any event or location before emergency responders or police even get on the scene.
There are multiple ways security can benefit from an affordable social media intelligence solution. Organizing social media data by location, in particular, supplies real-time situational awareness as well as intelligence for investigations after the fact. Immediate security benefits might include the ability to prevent violence at workplaces or schools. After the fact, law enforcement has already realised the benefits of using social media for investigations, notably after the Boston Marathon bombing in 2013.
"Customers have a big appetite for data coming from their locations, whether it’s a city or a corporation with facilities worldwide," says Phil Harris, CEO of Geofeedia, a software system that monitors and collects social media data based on location. Geofeedia aggregates information from multiple social media sources – Facebook, Twitter, Instagram, YouTube, Flickr, Picasa, and Viddy.
Geofeedia provides software as a service (SaaS); customers can buy annual or multi-year subscriptions that allow access to the platform at Geofeedia.com using a Web browser. Customers can access data of any location worldwide, do searches, and store data using the system.
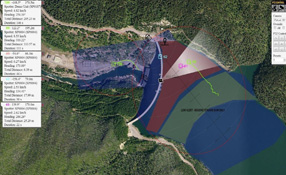
A location to be accessed can be defined as specifically as a building or a neighborhood block, or as broadly as a state. All data has a latitude and longitude associated with it, all searchable. A Google maps-based platform allows operators to zoom in on an area, or to define an area to be accessed using a circle or polygon. Alternatively, a corporate customer, for example, could define hundreds or even thousands of locations worldwide, and could actively record all the data whether they are logged in or not.The system can provide alerts and notifications based on the various “Geofeeds” from specific areas and can overlay alert criteria such as customisable word searches (e.g., "shoot my boss"). There is a best-practices generic list of search terms based on threats, and the customer can also customize the list. For example, for cities seeking to monitor gang activity, search terms can be customized to the specific and varied languages used by various gangs.
Here are some other ways that accessing social network data can be used to achieve security goals:
- Executive protection. If a VIP is being treated confidentially at a hospital, how can a company keep word of the hospital treatment from leaking out via social media? Such information could negatively impact the stock price if the VIP were a high-profile executive at a public company, for example. In the case of a stalker, a Geofeed around a VIP’s residence could provide an alert if a person using a certain IP address were to enter the perimeter.
- Prevention of counterfeiting. Companies know where their goods are manufactured and sold. Social media photos of their goods being made or sold somewhere else can alert them to counterfeiting.
- Monitoring protests. A large company that is especially sensitive to the risks of a protest could observe specific locations for protest-related social media content to “get ahead” of the situation, respond with public relations targeting local news, etc.
- Guarding intellectual property. If a company has an event previewing a future new product launch for dealers or internal groups, how can the company ensure details (even photos) of the new product(s) don’t leak out before the public announcement? Setting up a Geofeed around the event allows the corporation to monitor what information is being shared via social media.
"It goes back to the data," says Harris. "For the first time in human history, you can get on-the-ground information without a person or a camera there. We pull publicly available information and organize it in a matter of seconds." Corroboration is another benefit – multiple people tweeting can confirm the genuine nature of an event that might more likely be a hoax if tweeted by only one person.
Data can be analyzed and exported in multiple ways. A “map view” shows “pins” on a map of where social media sources are. A "collage view" enables fast scanning of video and images. A “streamer view” during a live event continually pushes data live, cascading down a screen. An "analytics view" organises by data source, hashtag, phrase, date range, spikes in volume, and by user – the operator can query whatever he or she wants. Alerts and notifications are provided based on user-defined triggers.
Data can also be exported into Excel, RSS or other system. Geofeedia has an application programming interface (API) to enable integration with PSIMs and other security systems.
Harris says the software provides an opportunity to garner real-time intelligence without additional overhead. "We are aligning ourselves with responsible groups to address real risks in the dynamic global environment," he adds.
For security, early adopters have included Microsoft, the Mall of America, and the Los Angeles sheriff’s department. Since beginning to sell the system in mid-2013, Geofeedia reports it has signed up "several hundred" security-related customers, including corporate enterprises and small and large towns.
The additional information supplied by images and video are a benefit of the Geofeedia system compared to text-only monitoring systems. Geofeedia collects all the social media photos and video associated with a certain area and allows the user to scroll down through the images to decide whether they are relevant. There may be no text associated with the video, which would make it impossible to search for otherwise.
Since beginning to sell the system |
The approach to monitoring social media can be proactive (watching the area around a stadium during a large event), or reactive (observing the area of a 911 call even before emergency responders arrive). "There is value to images and especially video, which can show movement over space and time with fairly high resolution," says Harris. For example, there is a good likelihood that if a fight were to break out at a sporting event, someone would be videotaping the whole time. A message like "OMG a fight broke out" might be tied to a detailed video that could be valuable to investigators.
The identity of social media users is often obvious from the photos associated with their social media account, including pictures of a user that may be easy to recognize if he or she is an employee, for example. If the social media user cannot be identified from the social media content, the company or law enforcement agency would have to use other means (including subpoenas) to get additional information from a social media provider (none of which is part of the Geofeedia system).
"Just like any powerful technology, using it in the proper way is important," says Harris. "We don’t replace the judgment of a security professional, we just give them additional intelligence. Customers decide whether to intervene in a situation. We’re a data source that organises the information to be more useful."